Search
Content type: Report
In the months following the beginning of the Covid-19 pandemic, more than half the world’s countries enacted emergency measures. With these measures came an increase in executive powers, a suspension of the rule of law, and an upsurge in security protocols – with subsequent impacts on fundamental human rights. Within this broader context, we have seen a rapid and unprecedented scaling up of governments’ use of technologies to enable widespread surveillance. Surveillance technologies exacerbated…
Content type: Long Read
The defense and protection of the environment continues to come at a high cost for activists and human rights defenders. In 2021, the murders of environment and land defenders hit a record high. This year, a report by Global Witness found that more than 1,700 environmental activists have been murdered in the past decade.
While the issue of surveillance of human rights defenders has received attention, evidence of the surveillance of environmental activists keeps mounting, with recent examples…
Content type: Report
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content type: News & Analysis
The UK government has acknowledged that section 8(4) of the Regulation of Investigatory Powers Act (“RIPA”) (which has since been repealed) violated Articles 8 and 10 of the European Convention on Human Rights (ECHR). In relation to Article 10, it specifically acknowledged that the way in which security agencies handled confidential journalistic material violated fundamental rights protected by Article 10.
As part of a friendly settlement with two applicants, the UK government acknowledged…
Content type: News & Analysis
*Photo by Michelle Ding on Unsplash
Pat Finucane was killed in Belfast in 1989. As he and his family ate Sunday dinner, loyalist paramilitaries broke in and shot Pat, a high profile solicitor, in front of his wife and children.
The Report of the Patrick Finucane Review in 2012 expressed “significant doubt as to whether Patrick Finucane would have been murdered by the UDA [Ulster Defence Association] had it not been for the different strands of involvement by the…
Content type: Long Read
Miguel Morachimo, Executive Director of Hiperderecho. Hiperderecho is a non-profit Peruvian organisation dedicated to facilitating public understanding and promoting respect for rights and freedoms in digital environments.The original version of this article was published in Spanish on Hiperderecho's website.Where does our feeling of insecurity come from? As we walk around our cities, we are being observed by security cameras most of the time. Our daily movement, call logs, and internet…
Content type: Long Read
*Photo by Kristina Flour on Unsplash
The British government needs to provide assurances that MI5’s secret policy does not authorise people to commit serious human rights violations or cover up of such crimes
Privacy International, along Reprieve, the Committee on the Administration of Justice, and the Pat Finucane Centre, is challenging the secret policy of MI5 to authorise or enable its so called “agents” (not MI5 officials) to commit crimes here in the UK.
So far we have discovered…
Content type: Examples
A woman was killed by a spear to the chest at her home in Hallandale Beache, Florida, north of Miami, in July. Witness "Alexa" has been called yet another time to give evidence and solve the mystery. The police is hoping that the smart assistance Amazon Echo, known as Alexa, was accidentally activated and recorded key moments of the murder. “It is believed that evidence of crimes, audio recordings capturing the attack on victim Silvia Crespo that occurred in the main bedroom … may be found on…
Content type: Advocacy
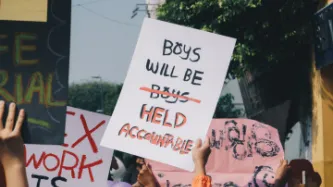
In this submission, Privacy International aims to provide the Office of the UN High Commissioner for Human Rights with information on how surveillance technologies are affecting the right to peaceful protests in new and often unregulated ways.
Based on Privacy International’s research, we provide observations, regarding the following:
the relationship between peaceful protests and the right to privacy;
the impact of new surveillance technologies in the context of peaceful protests…
Content type: Report
“...a mobile device is now a huge repository of sensitive data, which could provide a wealth of information about its owner. This has in turn led to the evolution of mobile device forensics, a branch of digital forensics, which deals with retrieving data from a mobile device.”
The situation in Scotland regarding the use of mobile phone extraction has come a long way since the secret trials were exposed. The inquiry by the Justice Sub-Committee, commenced on 10 May 2018, has brought much…
Content type: Examples
In late 2017, the residents of the small town of Santa Maria Tonantzintla, about three-hours away from Mexico City, discovered their town was intended to become a pilot smart city in a collaboration between the state of Puebla and the organisation Alianza Smart Latam. The town's residents, who had already lost its distinctive cobblestones, the clock tower, and a stucco bridge as part of the early stages of the project, filed an injunction to halt the project, which had failed to obtain the…
Content type: Long Read
Image credit: Emil Sjöblom [ShareAlike 2.0 Generic (CC BY-SA 2.0)]
Prepaid SIM card use and mandatory SIM card registration laws are especially widespread in countries in Africa: these two factors can allow for a more pervasive system of mass surveillance of people who can access prepaid SIM cards, as well as exclusion from important civic spaces, social networks, and education and health care for people who cannot.
Mandatory SIM card registration laws require that people provide personal…
Content type: Examples
The Lumi by Pampers nappies will track a child's urine (not bowel movements) and comes with an app that helps you "Track just about everything". The activity sensor that is placed on the nappy also tracks a baby's sleep.
Concerns over security and privacy have been raised, given baby monitors can be susceptible to hackers and any app that holds personal information could potentially expose that information.
Experts say the concept could be helpful to some parents but that there…
Content type: Advocacy
During its 98th session, from 23 April to 10 May 2019, the UN Committee on the Elimination of Racial Discrimination (CERD) initiated the drafting process of general recommendation n° 36 on preventing and combatting racial profiling.
As part of this process, CERD invited stakeholders, including States, UN and regional human rights mechanisms, UN organisations or specialised agencies, National Human Rights Institutions, Non-Governmental Organisations (NGOs), research…
Content type: Examples
In 2017, US Immigration & Customs Enforcement (ICE) announced that it would seek to use artificial intelligence to automatically evaluate the probability of a prospective immigrant “becoming a positively contributing member of society.” In a letter to acting Department of Homeland Security Secretary Elaine Duke, a group of 54 concerned computer scientists, engineers, mathematicians, and researchers objected to ICE’s proposal and demanded that ICE abandon this approach because it would be…
Content type: Examples
US Immigrations & Customs Enforcement (ICE) used social media monitoring to track groups and people in New York City associated with public events opposing the Trump administration’s policies, including ones related to immigration and gun control. The investigative branch of ICE created and circulated a spreadsheet, entitled ‘Anti-Trump Protest Spreadsheet 07/31/2018,” that provided details of events planned between July 31, 2018, and August 17, 2018. The spreadsheet pulled data from…
Content type: Examples
The US government created a database of more than 50 journalists and immigrant rights advocates, many of whom were American citizens, associated with the journey of migrants travelling from Central America to the Mexico-US border in late 2018. Officials from Customs and Border Protection (CBP), Immigration and Customs Enforcement (ICE), the US Border Patrol, Homeland Security Investigations, and the Federal Bureau of Investigation (FBI) had access to this database. This list allowed the…
Content type: Examples
A private intelligence company, LookingGlass Cyber Solutions, used social media to monitor more than 600 “Family Separation Day Protests” held across the United States on June 30, 2018, to oppose the Trump administration’s policy family separation policy. The policy was part of a “zero tolerance” approach to deter asylum seekers from coming to the United States by separating children from their parents. After collecting information about these protests through Facebook, including the precise…
Content type: Examples
In August 2017, it was reported that a researcher scraped videos of transgender Youtubers documenting their transition process without informing them or asking their permission, as part of an attempt to train artificial intelligence facial recognition software to be able to identify transgender people after they have transitioned.
These videos were primarily of transgender people sharing the progress and results of hormone replacement therapy, including video diaries and time-lapse videos. The…
Content type: Long Read
Imagine that every time you want to attend a march, religious event, political meeting, protest, or public rally, you must share deeply personal information with police and intelligence agencies, even when they have no reason to suspect you of wrongdoing.
First, you need to go to the police to register; have your photo taken for a biometric database; share the contacts of your family, friends, and colleagues; disclose your finances, health records, lifestyle choices, relationship status, and…