An explainer on SMS, 30 years down the line
SMS (Short Messaging Service) has been around for 30 years, and is likely to be around for a lot longer. In this piece, we take stock of the varied uses of SMS, and the challenges arising from it: privacy, security and reliability-wise.

What is SMS
SMS - or Short Messaging Service - refers to the widespread messaging service that virtually any of us will be familiar with. This refers to the first form of texting available on mobile phones, which makes use of cellular phone service - not to be confused with more modern instant messaging services making use of the internet instead (iMessage, Whatsapp, Signal ...). This explainer aims to give an overview of the technology, and some of its limitations in today's context and after its 30 years of existence.
The very first SMS message "Merry Christmas" was sent on December 1992, and the protocol remains ever as popular since the day. One recent study found that 1 in 3 people still exchange at least one SMS daily and 54% of people use SMS as a way of reaching people who are not on other instant messaging platforms such as Signal or Whatsapp. Companies also make for big users of SMS, be it to communicate with people about any appointments, the status of deliveries or, more annoyingly, for marketing. Worryingly, fraudsters often also rely on SMS to try and trick people into revealing confidential information about their bank account, credit card, or other personal accounts.
SMS is also one the most commonly offered methods for multi-factor authentication, being used in a variety of contexts from access to banking and government services, to acessing online accounts such as e-mail or social media. While setting up multi-factor authentication is a simple and effective step in keeping your accounts safer, different authentication methods offer different levels of integrity, and despite its popularity, SMS is likely one of the least secure authentication methods you can choose from. We will delve into some of the reasons why bellow. Having an additional authentication factor is still preferable than relying on a username and password only, but you may want to consider using a different method other than SMS.
SMS in today's context
Given the widespread use of SMS, particularly within banking systems and authentication frameworks, you could be led to assume the reason this protocol is so used and relied upon is because it is a secure and effective means of communication.
The reality is quite different though: we have been been living with a quite outdated technology that was never developed with security as an end goal, and relying on it simply because it's accessible to everyone with a mobile phone, no matter how basic and independent from any sort of internet connection. But what does SMS lack you might ask?
SMS was developed taking advantage of breaks in voice and control traffic on the network in order to send the text message accross. Since SMS can only be transmitted in periods when no signalling traffic exists this means that message transmission is done on a lower priority than other traffic like voice, prioritising overall network efficiency over message delivery efficacy. From a useability point of view it means there is no real guarantee that a message will ever be received, with studies saying that around 1-5 percent of all SMS messages are lost in transit "due to expiration or denial of delivery", even when nothing is seemingly wrong with the network.
In order to send SMS one needs to have cell phone service, which can be both limiting and frustrating at times, indifferent to whether you have a strong WI-FI connection. And by relying on cell phone service this also means that the SMS you send are unvariably connected to your unique IMSI and IMEI identifiers which can easily be traced back to you, more so if you live in a country where you need to register your SIM card with any type of ID or biometrics.
Who can see your SMS: Your Carrier
SMS messages are entirely unencrypted, meaning the sender, receiver and content of a message are not concealed at any point in time which makes it possible for your phone provider to see all of the messages you exchange. And while governments often mandate that mobile carriers keep copies of your data, i.e. the content of your communications, and only for a certain amount of time in accordance with data retention laws, the metadata generated as a result of using SMS services - who you communicate with, location data, the time at which you sent a given message, etc - is often kept for even longer, despite the fact it can be as revealing as the messages themselves. Take a journalist working with a sensitive source for example: in this case, having access to metadata about the sender and receiver of messages can work as proof that communication happened, which would be enough to compromise and potentially endanger this source.
“Metadata absolutely tells you everything about somebody’s life. If you have enough metadata, you don’t really need content.”
“We kill people based on metadata.”
- Former NSA Director Michael Hayden
Who can see your SMS: Authorities
In many countries, governments are able to lawfully request and access corporate data about individuals, which in this case means that if your data exists in a telecommunication company's database (or any other company for this effect) then it can also be made available to governments. This will depend on the applicable legal framework and general context, with some countries having higher thresholds for corporate data access than others.
Plain-text SMS messages can be more easily monitored by third parties than its encrypted alternatives, which is something governments or police forces around the world can take advantage of.
SMS monitoring can be performed in a specific geographic area, to monitor a protest for example by making use of Stingrays or IMSI catchers. These are devices which impersonate the cell towers that phones normally connect to, and trick the phones to connect to it instead. This allows for interception and control over SMS messages being exchanged within a certain area.
But SMS monitoring can also be done in a much wider, indiscriminate and surreptitious way. During its 30 years of existence, the protocols that SMS relies on haven't made many strides forward. Such is the case with SS7 (also known as Common Channel Signaling System 7) which has known vulnerabilities that have been demonstrably and repeatedly exploited. SS7 is used by telecom companies to coordinate how they route texts and calls around the world and it is possible for those who exploit SS7 to track the location of phones and intercept text messages and calls, from any location without hacking the phone itself. This was the case when the US governmental agency NSA was reported by Edward Snowden to be collecting about 200 million text messages a day from all over the globe, and collaborating with GCHQ in the process.
Who can see your SMS: criminal networks
For some time these flaws were mostly taken advantage of by governments and intelligence agencies, but criminal networks have been tapping into them too, and will continue to be able to do so for as long as we continue to rely on such outdated protocols.
Because your SMS communications are intrinsically connected to your SIM card, any attacks on your SIM card will threaten your SMS communications as well, which can put your identity and accounts that depend on SMS as two-factor authentication at risk. Attacks such as SIM hijacking or SIM Swapping which give an attacker access to your SIM card have become more common over the years. In order to attempt such an attack, all a fraudster needs is some initial information about a potential target which could be obtained from a range of sources, including a data leak for example. Having some information is enough for fraudsters to then contact the target's carrier and try to convince them that they are the person they are trying to impersonate. If the attack and impersonation are successful, the fraudster can then log in and compromise the target's accounts that use SMS for two-factor authentication - yet another reason to be mindful of SMS as a two-factor authentication platform for critical services.
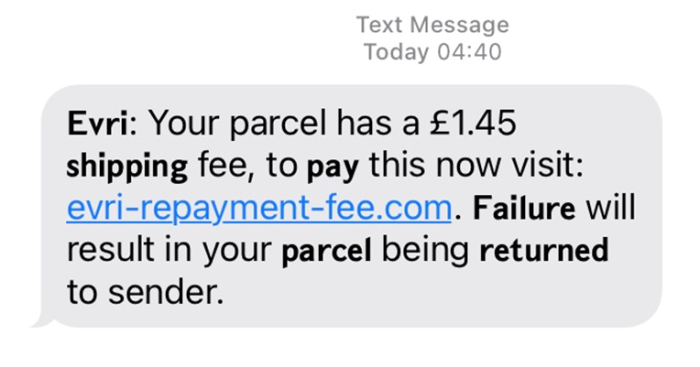
In addition to how easy it can be to spoof someone's phone number, SMS are impossible to authenticate - meaning there is no way to verify that messages are indeed coming from who they say they are coming from. This makes SMS extremely attractive to fraudsters who can use it to try and make you click on malicious links or disclose personal information by pretending they are someone else.
Who can see your SMS: Other apps on your phone
Some apps you install will ask for permission to access your SMS messages. In this case, more than being interested in the messages themselves, companies often seek to learn from the behaviour of their user because it's something they can directly monetise or use to attempt to improve their products and functionalities. Such is the case with Facebook, Google and many Fintech companies that will use the analysis coming from this data to determine someone's creditworthiness for example.
Why SMS then?
Despite all the evidence that SMS is an outdated technology, not built with either privacy or security in mind, it remains a protocol that is widely relied upon because of how widely accesible it is. We've seen the uptake of SMS across a range of essential services, for example in the reproductive and maternal health sector, as well as during during natural disasters or humanitarian crises. In the latter, SMS is often used to quickly disseminate information. In response to these perilous situations, some countries will create emergency response numbers that people can send texts to (such as Haiti when it was hit by an Earthquake) while others have introduced a dedicated service that will be activated when necessary such as the new mobile alert system introduced in Spain.
However, uses of SMS in crisis situations have been questioned because of inherent shortfalls with SMS, namely that targeting users based on their specific location is difficult; SMS are not authenticated, meaning there is no way one can prove that a message is coming from its stated source; and, as discussed above, message delivery is not predictable or guaranteed. In relation to Spain's new mobile alert system mentioned above for example, it is clearly stated that "you must have a modern smartphone for it to be compatible with the system, it won’t work with a very old phone".
Mobile technology and mobile payments have also gained popularity in recent years, particularly during the Covid-19 pandemic as a way to provide essential financial aid to people in need, quickly and at scale. For populations impacted by the combined effect of economic lockdowns, social distancing, and struggling social protection schemes, it is impossible to ignore the benefits that a technology with this level of penetration has brought upon millions, with 73% of the world's population over 10 years of age owning a cellphone nowadays.
All in all, it is crucial that we know the reach and possibilities around the technological tools we have available to us, but more importantly that we learn about their limitations instead of trusting them blindly. That way, we can better understand the risks of a technology, and make choices as to whether it's the best solution in a particular context.