Fighting the global crypto wars: bringing the tech and policy communities together
What happened
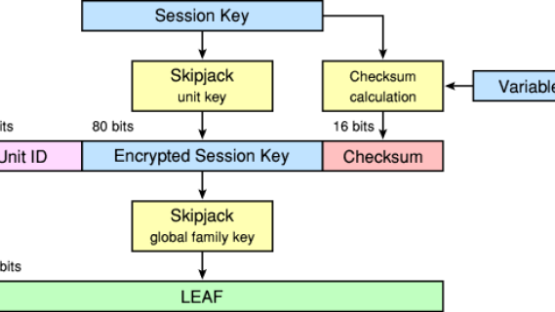
The Clinton Administration kicked off the cypto-wars in 1993 with the Clipper Chip. The continued application of export controls restrained the deployment of strong cryptography in products at a key moment of internet history: as it began to be embedded in software and networking.
What we did
In the early phases of the crypto-wars we placed pressure on global industry to implement encryption in their products. We ran campaigns and events across the world on the need for strong encryption. We worked with technology experts to communicate with policy-makers. We advised NGOs on the use of encryption products at a time when individuals who were taking it out of the US were being prosecuted. We campaigned at the OECD to get governments to recognise the security benefits of encryption as being essential to trust in digital society and commerce.
When governments started legislating, along with organisations like the Foundation for Information Policy Research we campaigned against policies requiring the storing of decryption keys with ‘trusted third parties’. We raised sufficient concern about the reality of these policies that they were withdrawn.
We also campaigned against policies requiring individuals to provide access to decryption keys. During the legislative debates in the UK and in Europe, we worked with industry bodies to get them to articulate strong positions on encryption and the risks to trust arising from government compulsion to disclose. While some amendments were legislated, ultimately the UK Regulation of Investigatory Powers Bill became law with the power to compel disclosure of keys — but not before we had bruised it and made it clear to other governments that it was a step too far, rather than a model to be replicated.
We repeatedly pressured companies to deploy transport-level encryption only to get pushback on grounds of efficiency and lack of consumer interest. We repeatedly called for end-to-end encryption and transparency over how encryption was deployed in products like Skype; only for industry to remain silent.
Where things stand now
The war against cryptography continues. There is continued rhetoric that there shouldn’t be any safe places where the government cannot go in the UK and there are continued calls for ‘responsible encryption’ that would replace ‘warrant proof’ in the US. We are seeing countries around the world continue to implement restrictions on cryptography and politicians campaign against end-to-end encryption. The war on cryptography is cross-party: governments do not want individuals to be able to exclude them from their lives.
What we learned
Governments play a long game and pressure on industry must be continuous to effect change. Industry was often tempted to do as governments wanted of them — and we had to constantly pressure them to avoid ‘solutions’ like key escrow.
Even though governments ‘lost’ the crypto-wars in the 1990s as encryption was liberalised from export controls and Western governments decided against mandating specific forms of use, encryption did not get embedded in early phases of the internet.
Hard lessons
Despite all this work, governments continued to undermine crypto in secret, and companies continued to resist in the deployment of strong crypto. The hard work wasn't just winning policy fights; we should have pushed harder on companies, even past their complaints that implementing crypto hurt performance, for instance.
Ultimately we are asking companies to exclude themselves from our data, and in the data-driven economy, this is something companies rarely want to do.
What we are doing now
The crypto-wars were a very specific fight against very obtuse restrictions. New government approaches focus on end-to-end encryption, access to devices, and government hacking powers which will require a different set of strategies.
We are supporting the work of our partners in countries where encryption is still regulated. We are promoting a framing of cyber security that secures people and their data. We are fighting government hacking laws, that are often interpreted as a necessary step in the face of encryption but is more likely a complementary power. We are fighting for a future where end-to-end encryption is widely deployed, securing individuals and their data from all.



