Privacy International challenges GCHQ's unlawful hacking of computers, mobile phones
Privacy International today filed a legal complaint demanding an end to the unlawful hacking being carried out by GCHQ which, in partnership with the NSA, is infecting potentially millions of computer and mobile devices around the world with malicious software that gives them the ability to sweep up reams of content, switch on users' microphones or cameras, listen to their phone calls and track their locations.
The complaint, filed in the UK’s Investigatory Powers Tribunal, is the first UK legal challenge to the use of hacking tools by intelligence services. It contends that the infection of devices with malicious software, which enables covert intrusion into the devices and lives of ordinary people, is so invasive that it is incompatible with democratic principles and human rights standards. Moreover, given that GCHQ and the NSA have no clear lawful authority to conduct hacking, which if performed by a private individual would involve the commission of criminal offences, their conduct is unlawful and must be halted immediately.
The extent of GCHQ’s capabilities was revealed by the Snowden documents, which detail how GCHQ and NSA are using malware to conduct surveillance that is potentially far more intrusive than any other current surveillance technique, including the interception of communications. GCHQ's hacking capabilities are so advanced that they are able to surreptitiously:
- take over a device's microphone and record conversations taking place near the device (NOSEY SMURF);
- take over a device's webcam and snap photographs (GUMFISH);
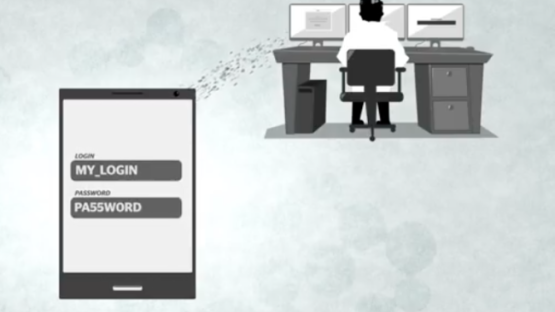
- record Internet browsing histories and collect login details and passwords used to access websites and email accounts (FOGGYBOTTOM);
- log keystrokes entered into a device (GROK);
- extract data from removable flash drives that connect to an infected computer (SALVAGERABBIT);
- identify the geographic whereabouts of the user (TRACKER SMURF); and
- retrieve any content from a phone, including text messages, e-mails, web history, call records, videos, photos, address books, notes, and calendars.
These forms of invasive surveillance allow intelligence agencies access to the most personal and sensitive information about an individual’s life – their location, age, gender, marital status, finances, health information, ethnicity, sexual orientation, education, family relationships, private communications, and potentially, their most intimate thoughts.
Worse still, the logging of keystrokes, the tracking of location, or the covert photography or recording of the user and those around them enables agencies to conduct real-time surveillance, while access to stored data enables analysis of a user's location for up to one year prior to the search.
In sum, the use of malicious software to hack into a computer or mobile device is equivalent to covert, complete, real-time physical and electronic surveillance, as well as historical surveillance, of everything that person does, sees and says.
Privacy International argues that the use of such capabilities is a clear violation of Article 8 (the right to privacy) and Article 10 (right to freedom of expression) of the European Convention on Human Rights, and must end immediately.
Eric King, Deputy Director of Privacy International, said:
The hacking programmes being undertaken by GCHQ are the modern equivalent of the government entering your house, rummaging through your filing cabinets, diaries, journals and correspondence, before planting bugs in every room you enter. Intelligence agencies can do all this without you even knowing about it, and can invade the privacy of anyone around the world with a few clicks.
All of this is being done under a cloak of secrecy without any public debate or clear lawful authority. Arbitrary powers such as these are the purview of dictatorships not democracies. Unrestrained, unregulated Government spying of this kind is the antithesis of the rule of law and Government must be held accountable for their actions.”