Search
Content type: News & Analysis
Maddie Stone, formally a Senior reverse engineer and tech lead on the Android security team, shockingly revealed a number of examples of how pre-installed apps on Android devices can undermine users privacy and security in her BlackHat USA talk in August 2019. The video of the talk only recently became available to the public in late December 2019.
The apps in question come preloaded on a device when it is purchased and often can't be removed. Stone reveals a litany of abuses carried out by…
Content type: Advocacy
Puede encontrar la carta a continuación. Agregue su voz a esta campaña firmando nuestra petición si cree que es hora de que Google deje de permitir la explotación.
Nota: Esta carta también está disponible en francés e inglés.
Estimado Sr. Pichai,
Nosotros, los firmantes, estamos de acuerdo con usted: la privacidad no puede ser un lujo reservado para las personas que tienen la capacidad de pagar por ella.
Sin embargo, los socios de Android Partner –que utilizan la marca y la imagen de…
Content type: Advocacy
You can find the letter below. Add your voice to this campaign by signing our petition if you believe that its time Google stopped enabling exploitation.
Note: This letter is also available in French and Spanish
Dear Mr. Pichai,
We, the undersigned, agree with you: privacy cannot be a luxury offered only to those people who can afford it.
And yet, Android Partners - who use the Android trademark and branding - are manufacturing devices that contain pre-installed apps that cannot be deleted…
Content type: Advocacy
Vous pouvez trouver la lettre ci-dessous. Ajoutez votre voix à cette campagne en signant notre pétition si vous pensez qu'il est temps que Google cesse d'activer l'exploitation.
Ce contenu est également disponible en anglais et en espagnol.
Cher M. Pichai,
Nous, les organisations signataires, sommes d’accord avec vous :
la vie privée n’est pas un luxe, offert seulement à ceux qui en ont les moyens.
Pourtant, les « Android Partners » – qui utilisent la marque déposée…
Content type: Long Read
Content type: Explainer
Abstract
Over the past few years, smart phones have become incredibly inexpensive, connecting millions of people to the internet for the first time. While growing connectivity is undeniably positive, some device vendors have recently come under scrutiny for harvesting user data and invasive private data collection practices.
Due to the open-source nature of the Android operating system vendors can add pre-installed apps (often called “bundled apps” or "bloatware") to mobile phones.…
Content type: Video
Christopher Weatherhead and Eva Blum-Dumontet Discuss the finding of Privacy International's report on the MyPhone MYA2 from the Philippines
Content type: Report
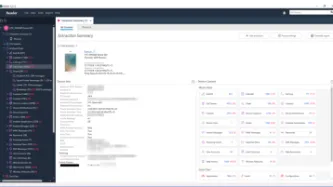
“...a mobile device is now a huge repository of sensitive data, which could provide a wealth of information about its owner. This has in turn led to the evolution of mobile device forensics, a branch of digital forensics, which deals with retrieving data from a mobile device.”
The situation in Scotland regarding the use of mobile phone extraction has come a long way since the secret trials were exposed. The inquiry by the Justice Sub-Committee, commenced on 10 May 2018, has brought much…
Content type: Long Read
In December 2018, Privacy international exposed the dubious practices of some of the most popular apps in the world.Out of the 36 apps we tested, we found that 61% automatically transfer data to Facebook the moment a user opens the app. This happens whether the user has a Facebook account or not, and whether they are logged into Facebook or not. We also found that some of those apps routinely send Facebook incredibly detailed and sometimes sensitive personal data. Again, it didn’t matter if…
Content type: Examples
In October 2018, the Singapore-based startup LenddoEFL was one of a group of microfinance startups aimed at the developing world that used non-traditional types of data such as behavioural traits and smartphone habits for credit scoring. Lenddo's algorithm uses numerous data points, including the number of words a person uses in email subject lines, the percentage of photos in a smartphone's library that were taken with a front-facing camera, and whether they regularly use financial apps on…
Content type: Report
Like many others, PI were alarmed at recent reports that Facebook have been making mobile phone numbers (which users believed to be) provided for the express purpose of "two-factor authentication" (2FA) both searchable, and a target for advertising by default.
One of the myriad ways Facebook displays targeted adverts to users is through so-called "Custom Audiences". These "custom audiences" are lists of contact details, including phone numbers and email addresses, uploaded by advertisers.…
Content type: Explainer
We look at the recently published report on forensic science in the UK, highlight concerns about police not understanding new tech used to extract data from mobile phones; the risk of making incorrect inferences and the general lack of understanding about the capabilities of these tools.
The delivery of justice depends on the integrity and accuracy of evidence and trust that society has in it. So starts the damning report of the House of Lords Science and Technology Select…
Content type: News & Analysis
Privacy International has joined a global coalition of privacy campaigners, tech companies, and technology experts to respond to proposals by British intelligence chiefs aimed at allowing them access to encrypted messaging apps such as WhatsApp or Signal.
If implemented, the proposals would allow government authorities to force messaging platforms to silently add a law enforcement participant to a group chat or call.
Such a capability poses serious threats to…
Content type: Examples
In February 2019 Google engineers announced that they had created faster, more efficient encryption system that could function on less-expensive Android phones that were too low-powered to implement existing full-device encryption. The scheme, known as Adiantum, uses established and well-vetted encryption tools and principles. Android has required smartphones to support encryption since 2015's version 6, but low-end devices were exempt because of the performance hit. It will now be up to device…
Content type: News & Analysis
A mobile device is a huge repository of sensitive data, which could provide a wealth of information about its owner and many others with whom the user interacts.
Companies like Cellebrite, MSAB and Oxygen Forensics sell software and hardware to law enforcement. Once your phone is connected to one of these mobile phone extraction tools, the device extracts, analyses and presents the data contained on the phone.
What data these tools can extract and what method is used will…
Content type: News & Analysis
According to the International Organization for Migration, an estimated 258 million people are international migrants – that is, someone who changes their country of usual residence, That’s one in every 30 people on earth.
These unprecedented movements levels show no sign of slowing down. It is predicted that by 2050, there will be 450 million migrants across the world.
Nowadays, it is politically acceptable to demonise migrants, and countless leaders have spewed divisive and xenophobic…
Content type: Long Read
(In order to click the hyperlinks in the explainer below, please download the pdf version at the bottom of the page).
Content type: Explainer graphic
You can also read a more detailed explainer about mobile phone extraction here.
Content type: Examples
In November 2016, the security contractor Krytowire discovered that cheap Chinese Android phones often include pre-installed software that monitors users' locations, messaging, and contacts, and sends the gathered information to China every 72 hours. Shanghai Adups Technology Company, the Chinese firm responsible for the software, said its code had been installed on more than 700 million phones, cars, and other devices without informing users, but that it was not intended for American phones.…
Content type: Examples
In July 2018, researchers at the London-based security and mobile commerce firm Upstream Systems found that millions of cheap smartphones sold in developing countries lacking privacy protections come with pre-installed apps that harvest users' data for the purpose of targeting advertising and that can only be removed with difficulty. One such app, which Singtech includes on the thousands of smartphones it sells in Myanmar and Cambodia, as well as others sold in Brazil or made by Indian and…
Content type: Examples
In September 2018, researchers discovered that websites accessed via mobile phones could access an array of device sensors, unlike apps, which request permissions for such access. The researchers found that 3,695 of the top 100,000 websites incorporate scripts that tap into one or more sensors, including Wayfair, Priceline, and Kayak. Unlike location sensors, motion, lighting, and proximity sensors have no mechanism for notifying users and requesting permission. Ad blockers were not effective…
Content type: Examples
Google launched its first version of Android in 2009. Based on a modified Linux kernel and other open source software, Android provides the operating system for mobile phones, tablets, televisions, cars, wrist watches, and many other devices including digital cameras, game consoles, PCs, and personal video recorders. By 2017, Android had become the best-selling operating system in the world, with over 2 billion monthly active users. Even in 2009, critics warned that the operating system, which…
Content type: Examples
The Danish company Blip Systems deploys sensors in cities, airports, and railway stations to help understand and analyse traffic flows and improve planning. In the UK's city of Portsmouth, a network of BlipTrack sensors was installed in 2013 by VAR Smart CCTV, and the data it has collected is used to identify problem areas and detect changing traffic patterns. The city hope that adding more sensors to identify individual journeys will help reduce commuting times, fuel consumption, and vehicular…
Content type: Long Read
We found the image here.
When we browse the internet, go to work, drive down the street, go shopping, interact with institutions, or simply move through the city, data is collected about us.
Advanced profiling technologies answer questions we did not raise. They generate knowledge we did not anticipate, but are eager to apply. As knowledge is power, profiling changes the power relationships between the profilers and the profiled.
In a world where everything we do becomes more and more…
Content type: News & Analysis
This op-ed originally appeared in the New Statesman.
Imagine the police searching your home without good reason, without a warrant, without your knowledge. For good measure let’s also imagine that they take a full inventory of all of your possessions and store this in a secret database indefinitely.
A peculiar feature of modernity is that what we would find dystopian in the real world is banal in our virtual world. And the irony is that this can be a greater violation of our privacy and…
Content type: Press release
Key points:
Privacy International have today published a report entitled 'Digital Stop and search: how the UK police can secretly download everything from your mobile phone', based on Freedom of Information requests to 47 police forces across the UK about their use of 'mobile phone extraction' technologies, which enable them to download all the content and data from a mobile phone.
Police forces across the UK are secretly downloading data from the smartphones of people across…
Content type: Video
Content type: Explainer
Phone networks are divided between two networks: the physical and the mobile. The physical runs on the Public Switched Telephone Network (PSTN) that serves your home phone. Mobile networks are dominant in the age of communication and are used to relay mobile communications to the PSTN. The most prominent mobile networks are GSM networks (Global System for Mobile communications) and are what we use everyday to communicate with one another. Another system is known as CDMA (Code Division Multiple…
Content type: Case Study
Gig economy jobs that depend on mobile applications allow workers’ movements to be monitored, evaluated, and exploited by their employers.
The so-called “gig economy” has brought to light employers’ increasing ability and willingness to monitor employee performance, efficiency, and overall on-the-job conduct. Workplace surveillance of gig economy workers often happens without employees’ awareness or consent. This is especially evident in the app-based gig economy, where apps act both as an…