Search
Content type: Report
In the months following the beginning of the Covid-19 pandemic, more than half the world’s countries enacted emergency measures. With these measures came an increase in executive powers, a suspension of the rule of law, and an upsurge in security protocols – with subsequent impacts on fundamental human rights. Within this broader context, we have seen a rapid and unprecedented scaling up of governments’ use of technologies to enable widespread surveillance. Surveillance technologies exacerbated…
Content type: Long Read
Introduction
India’s educational system is the largest in the world, with over 250 million students, 50% of whom attend publicly administered schools.
The autonomy given by the Indian Constitution to the 28 states and 8 union territories means that the right to education is implemented quite differently in each one, respecting culture, language, and other local specificities. Educational policies are suggested at the national level by various autonomous agencies and states can implement them in…
Content type: Report
Introduction
Several policy initiatives are in progress at the EU level. They seek to address the sustainability of connected devices such as smartphones, tablets and smart speakers. While initiatives to extend the useful life of hardware are important, software must not be ignored. Almost any digital device with which we interact today relies on software to function, which acts as a set of instructions that tells the hardware what to do. From smart thermostats to smart speakers, to our…
Content type: Press release
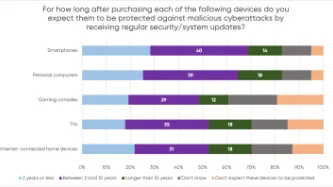
A YouGov survey commissioned by PI shows that consumers expect their smartphones, computers, smart TVs and gaming consoles to receive security updates for a much longer period than what several manufacturers actually provide, leaving consumers with expensive tech that is vulnerable to cyberattacks.
The majority of consumers in the survey assumed their devices would be protected beyond two years, but current industry practices fail to meet these expectations. PI investigated the software…
Content type: Report
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content type: Long Read
Introduction
In response to the unprecedented social, economic, and public health threats posed by the Covid-19 pandemic, the World Bank financed at least 232 "Covid-19 Response" projects. The projects were implemented across countries the World Bank classifies as middle and low-income.
This article will focus on eight (8) Covid-19 Response projects which sought to deliver social assistance to individuals and families on a "non-contributory" basis (this means that the intended beneficiaries…
Content type: Long Read
The global COVID-19 health crisis not only induced a public health crisis, but has led to severe social, economic and educational crises which have laid bare any pre-existing gaps in social protection policies and frameworks. Measures identified as necessary for an effective public health response such as lockdowns have impacted billions workers and people's ability to sustain their livelihood worldwide, with countries seeing unprecedented levels of applications for welfare benefits support,…
Content type: Long Read
Imagine your performance at work was assessed directly from the amount of e-mails sent, the amount of time consumed editing a document, or the time spent in meetings or even moving your mouse. This may sound ludicrous but your boss might be doing exactly that. There are more and more stories emerging of people being called into meetings to justify gaps in their work only to find out their boss had been watching them work without their knowledge.
The Covid-19 global pandemic has reshuffled the…
Content type: Call to Action
Content type: Report
Privacy International’s submissions for the Independent Chief Inspector of Borders and Immigration inspection of the Home Office Satellite Tracking Service Programme
The Home Office have introduced 24/7 electronic monitoring and collection of the location data of migrants via GPS ankle tags. This seismic change cannot be overstated. The use of GPS tags and intention to use location data, kept for six years after the tag is removed, in immigration decision-making goes far beyond the mere…
Content type: Report
El informe se basa en investigación documental y empírica (cualitativa y cuantitativa) realizada por Privacy International (PI) en 2021. Más concretamente, PI envió una encuesta a varios reguladores antimonopolio y a organizaciones de la sociedad civil con sede y/o que operan en diversas partes del mundo.
Las preguntas planteadas a los reguladores y a la sociedad civil versaron sobre su trabajo en la economía digital. Se preguntó a los reguladores y a las OSC si incorporaban consideraciones…
Content type: Report
The report builds on both desk and empirical (qualitative and quantitative) research that was carried out by Privacy International (PI) in 2021. Specifically, PI sent out a survey to several antitrust regulators and CSOs based and/or operating in various parts of the world. The questions posed to regulators and civil society revolved around their work in the digital economy. Regulators and CSOs were asked to comment on whether and how personal data considerations were incorporated into their…
Content type: Report
This briefing takes a look at the private intelligence industry, a collection of private detectives, corporate intel firms, and PR agencies working for clients around the world that have made London their hub.
Often staffed by ex-spooks, and promising complete secrecy, little is known about them. But reports over the years have exposed their operations, including things like hacking and targeting of anti-corruption officials, spying on peaceful environment activists, and running fake '…