Search
Content type: Report
Introduction
Several policy initiatives are in progress at the EU level. They seek to address the sustainability of connected devices such as smartphones, tablets and smart speakers. While initiatives to extend the useful life of hardware are important, software must not be ignored. Almost any digital device with which we interact today relies on software to function, which acts as a set of instructions that tells the hardware what to do. From smart thermostats to smart speakers, to our…
Content type: Press release
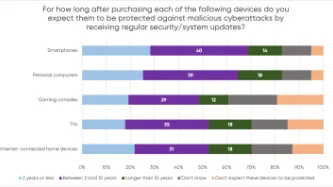
A YouGov survey commissioned by PI shows that consumers expect their smartphones, computers, smart TVs and gaming consoles to receive security updates for a much longer period than what several manufacturers actually provide, leaving consumers with expensive tech that is vulnerable to cyberattacks.
The majority of consumers in the survey assumed their devices would be protected beyond two years, but current industry practices fail to meet these expectations. PI investigated the software…
Content type: Long Read
Image Source: "Voting Key" by CreditDebitPro is licensed under CC BY 2.0
Democratic society is under threat from a range of players exploiting our data in ways which are often hidden and unaccountable. These actors are manifold: traditional political parties (from the whole political spectrum), organisations or individuals pushing particular political agendas, foreign actors aiming at interfering with national democratic processes, and the industries that provide products that …
Content type: Key Resources
Introduction
Why We Are So Concerned about Government Hacking for Surveillance
Scope of Our Safeguards
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4. Judicial Authorisation
5. Integrity of information
6. Notification
7. Destruction and Return of Data
8. Oversight and Transparency
9. Extraterritoriality
10. Effective Remedy
Commentary on each
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4.…
Content type: News & Analysis
This guest piece was written by Elonnai Hickok and Vipul Kharbanda of the Centre for Internet and Society. It does not necessarily reflect the views or position of Privacy International.
In light of the complex challenges and threats posed to, and by, the field of information telecommunications in cyberspace, in 1998 the draft resolution in the First Committee of the UN General Assembly was introduced and adopted without a vote (A/RES/53/70)…
Content type: News & Analysis
In the wake of tragic attacks in France, politicians from across the world are calling for dramatically expanded surveillance powers, to spy on our phonecalls, ban encrypted communications such as WhatsApp and iMessage, and store details about our international travels for years on end.
If it feels like you've heard this story before, it's because you have. With each violent attempt by extremists to terrorise society, our political leaders dust off old, failed proposals such as the UK…