Search
Content type: Press release
In a landmark judgment, handed down today (Monday 30 January 2023), the Investigatory Powers Tribunal have found that there were “very serious failings” at the highest levels of MI5 to comply with privacy safeguards from as early as 2014, and that successive Home Secretaries did not to enquire into or resolve these long-standing rule-breaking despite obvious red flags.Human rights organisations Liberty and Privacy International, who brought this significant legal case in January 2020, have…
Content type: Report
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content type: News & Analysis
Around the world, we see migration authorities use technology to analyse the devices of asylum seekers. The UK via the Policing Bill includes immigration officers amongst those who can exercise powers to extract information from electronic devices. There are two overarching reasons why this is problematic:
The sole provision in the Policing Bill to extract information rests on voluntary provision and agreement, which fails to account for the power imbalance between individual and state. This…
Content type: News & Analysis
It is difficult to imagine a more intrusive invasion of privacy than the search of a personal or home computer ... when connected to the internet, computers serve as portals to an almost infinite amount of information that is shared between different users and is stored almost anywhere in the world.
R v Vu 2013 SCC 60, [2013] 3 SCR 657 at [40] and [41].
The controversial Police Crime Sentencing and Courts Bill includes provision for extracting data from electronic devices.
The Bill…
Content type: Examples
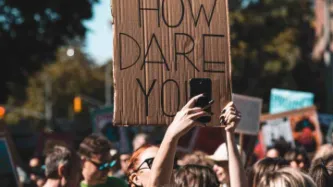
During the Black Lives Matter protests of summer 2020, US police took advantage of a lack of regulation and new technologies to expand the scope of people and platforms they monitor; details typically emerge through lawsuits, public records disclosures, and stories released by police department PR as crime prevention successes. A report from the Brennan Center for Justice highlights New York Police Department threats to privacy, freedom of expression, and due process and the use of a predator…
Content type: Case Study
Facial recognition technology (FRT) is fairly present in our daily lives, as an authentication method to unlock phones for example. Despite having useful applications, FRT can also be just another technology used by those in power to undermine our democracies and carry out mass surveillance. The biometric data collected by FRT can be as uniquely identifying as a fingerprint or DNA. The use of this technology by third parties, specially without your consent, violates your right to privacy.
The…
Content type: Long Read
In December 2019, the Information Rights Tribunal issued two disappointing decisions refusing appeals brought by Privacy International (PI) against the UK Information Commissioner.
The appeals related to decisions by the Information Commissioner (IC), who is responsible for the UK’s Freedom of Information regime, concerning responses by the Police and Crime Commissioner for Warwickshire and the Commissioner of Police for the Metropolis (The Metropolitan Police) to PI’s freedom of information…
Content type: Case Study
IMSI catchers – International Mobile Subscriber Identity catchers – are a particularly intrusive technology being used by police to monitor protesters and intercept their personal information and communications.
IMSI catchers have been used - officially or in secret - across the globe to monitor protests, including in the US and Germany; in the UK, police forces have refused to disclose any information on their use but documents obtained by the Bristol cable show that nine police forces have…
Content type: Long Read
The UK’s Metropolitan Police have began formally deploying Live Facial Recognition technology across London, claiming that it will only be used to identify serious criminals on “bespoke ‘watch lists’” and on “small, targeted” areas.
Yet, at the same time, the UK’s largest police force is also listed as a collaborator in a UK government-funded research programme explicitly intended to "develop unconstrained face recognition technology", aimed “at making face…
Content type: Long Read
Imagine that every time you want to attend a march, religious event, political meeting, protest, or public rally, you must share deeply personal information with police and intelligence agencies, even when they have no reason to suspect you of wrongdoing.
First, you need to go to the police to register; have your photo taken for a biometric database; share the contacts of your family, friends, and colleagues; disclose your finances, health records, lifestyle choices, relationship status, and…