Search
Content type: News & Analysis
This post was written by PI Technologist Ed Geraghty.
At the very heart of ThornSec’s design is that we assume our security will fail. There is nothing perfect on this earth (except kittens). The entire point is to fail well. For charities and NGOs that are fragile, poorly resourced, and often at risk, this is relatively novel thinking. We prepare for that with a strict adherence to good security practice.
It is exactly this element of novelty that makes us more open than your…
Content type: News & Analysis
Overview
CIPIT is currently investigating how the privacy of Kenyan citizens was affected by the use of biometric data during the just concluded 2017 general and repeat elections. The IEBC is mandated by law to register voters, verify their registration details and conduct elections. Accordingly, the IEBC is the custodian of the public voter register. There have been reports that individuals received SMS texts from candidates vying for various political seats during the campaign period of the…
Content type: News & Analysis
There are three good reasons why security is so hard for NGOs. First, we are afraid to speak about meaningful security. Second, we focus on the wrong areas of security and in turn spend money and prioritise the wrong things. Third, we struggle to separate the world we want from the worlds we build within our own organisations. At PI we have failed and struggled with each of these for over 20 years. Out of exhaustion, we decided to do something about it: we are building an open framework, a…
Content type: News & Analysis
This is the story of Privacy International's journey to building more secure services. Data collection and administering sensitive data on the open web is risky, and PI had to learn this the hard way.
Many companies say that the privacy of their audiences is their top priority. But do they mean it? Do they invest in it? Doing security on tight budgets is incredibly hard. But it is the natural state of the non-profit sector. We learned this through challenging experiences.…
Content type: News & Analysis
Photo Credit: MoD UK
‘Security’ in the policy world has practically no currency without a specific prefix. For example, we could discuss 'national' security as distinct from 'consumer' security or 'energy' security. ‘Cyber’ security is the new prefix on the policy block, and it is gradually forcing a rethink on what it means to be secure in a modern society. In the course of Privacy International’s work globally, we have observed that many governments frame cyber security as national security…
Content type: News & Analysis
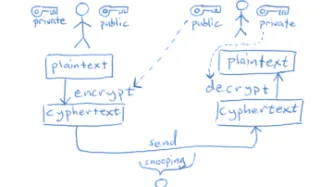
The past few years have seen a huge rise in the number of attacks both active and passive, against organisations big and small. Attacks against organisations happen for a multitude of reasons: extortion via "ransomware", exfiltration of commercial secrets, or just "the lulz". While this can be crippling to a commercial business, it can potentially be devastating to an NGO, especially those which work to hold powerful institutions to account. The types of information held by such NGOs could…
Content type: News & Analysis
Dear Politicians,
With elections coming up and quite a few cringe-worthy comments that have come from many of you and from all sides of the political spectrum, we figured it was time to have a chat about encryption.
First, let’s say what you shouldn’t do:
call for boycotts of companies because they protect their users’ data even from the companies themselves.
say something like “we’ll develop a Manhattan-level project on this” (which, as we’ll remind you, ended up with the creation of a…
Content type: News & Analysis
On a hot day in Nairobi, our researcher is speaking to an officer of Kenya’s National Intelligence Service (NIS). The afternoon is wearing on and the conversation has turned to the presidential elections, taking place in August this year. He has just finished describing the NIS’ highly secret surveillance powers and the disturbing ways in which these powers are deployed.
“It is what you might call ‘acceptable deaths,’” he states about the misuse of communications surveillance powers. “People…