Advanced Search
Content Type: Advocacy
Privacy International and Open Rights Group welcome the Competition and Market Authority (CMA)’s call for information on digital mergers. In this submission, the organisations provide their observations on some of the questions raised in this consultation, focussing on: the ways in which digital products or services are monetized though user data and advertising; questioning the assumption that users pay products or services with personal data; providing examples of…
Content Type: Long Read
Photo by David Werbrouck on Unsplash
This is an ongoing series about the ways in which those searching for abortion information and procedures are being traced and tracked online. This work is part of a broader programme of work aimed at safeguarding the dignity of people by challenging current power dynamics, and redefining our relationship with governments, companies, and within our own communities. As an enabling right, privacy plays an important role in supporting the exercise of…
Content Type: News & Analysis
While people may think that providing their photos and data is a small price to pay for the entertainment FaceApp offers, the app raises concerns about privacy, manipulation, and data exploitation—although these concerns are not necessarily unique to FaceApp.According to FaceApp's terms of use and privacy policy, people are giving FaceApp "a perpetual, irrevocable, nonexclusive, royalty-free, worldwide, fully-paid, transferable sub-licensable license" to use or publish the…
Content Type: Long Read
By Valentina Pavel, PI Mozilla-Ford Fellow, 2018-2019
Our digital environment is changing, fast. Nobody knows exactly what it’ll look like in five to ten years’ time, but we know that how we produce and share our data will change where we end up. We have to decide how to protect, enhance, and preserve our rights in a world where technology is everywhere and data is generated by every action. Key battles will be fought over who can access our data and how they may use it. It’s time to take…
Content Type: Advocacy
Democratic engagement is increasingly mediated by digital technology. Whether through the use of social media platforms for political campaigning, biometric registration of voters and e-voting, police monitoring of political rallies and demonstrations using facial recognition, and other surveillance methods, technology is now infused into the political process.
These technologies rely on collecting, storing, and analysing personal information to operate. Much recent debate around…
Content Type: News & Analysis
This blogpost is a preview of the full 'Our Data Future' story, produced by Valentina Pavel, PI Mozilla-Ford Fellow, 2018-2019.
2030.
Four worlds.
One choice. Which one is yours?
All aboard! Time to step into the imaginarium. Explore four speculative future scenarios, examining how different ways of governing data create vastly different worlds. How is our digital environment going to look like in ten years' time? What’s going to be our relationship with data?
Each of us has a role in…
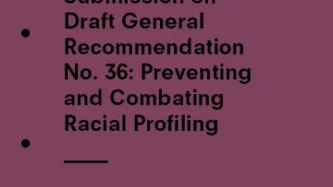
Content Type: Advocacy
During its 98th session, from 23 April to 10 May 2019, the UN Committee on the Elimination of Racial Discrimination (CERD) initiated the drafting process of general recommendation n° 36 on preventing and combatting racial profiling.
As part of this process, CERD invited stakeholders, including States, UN and regional human rights mechanisms, UN organisations or specialised agencies, National Human Rights Institutions, Non-Governmental Organisations (NGOs), research…
Content Type: Examples
In 2009, Amazon Kindle readers were surprised to find that their copies of George Orwell’s 1984 was missing from their devices. Amazon had remotely deleted these copies after it found out from the publisher that the third-party vendor selling them did not own the rights to the books. Amazon refunded the cost of the books but told its readers who were affected that they could no longer read the books and that the titles were “no longer available for purchase.” This was not the first time that…
Content Type: Examples
From 2014 to early 2017, Amazon used an artificial intelligence (AI) hiring tool to review prospective employees’ resumes and select qualified candidates, based on Amazon’s previous hiring decisions from a ten-year period; however, the tool was much more effective at simply selecting male candidates, rather than the most qualified candidates, because Amazon had hired predominantly male candidates in the past. The hiring tool learned to discriminate against resumes that included the word “women’…
Content Type: Examples
The American Civil Liberties Union (ACLU) used Rekognition, Amazon’s facial recognition software, to compare images of US lawmakers to a publicly available database of 25,000 mugshot photos. The ACLU’s study validated research that has shown that facial recognition technology is more likely to produce false matches for women and people with darker skin. Amazon’s software misidentified 28 lawmakers as being the people in mugshots, and these false matches were disproportionately of members of…
Content Type: Examples
More than 450 Amazon employees delivered a letter to Jeff Bezos and other Amazon executives, demanding that the company immediately stop selling facial recognition software to law enforcement, sever connections to companies like Palantir that help immigration authorities track and deport immigrants, and provide greater employee oversight when making ethical decisions. The employees protested against Amazon allowing its technologies to be used for mass surveillance and abused by those in power,…
Content Type: Examples
Amazon shareholders rejected two non-binding proposals governing its facial recognition software, Rekognition: one would have limited sales of Rekognition to governments, unless a board determined that such sales would not violate peoples’ rights, and the other was to study the extent to which Rekognition infringed peoples’ privacy and other rights. These two proposals were presented to shareholders despite Amazon’s effort to stop the votes, which were thwarted by the US Securities and Exchange…
Content Type: Examples
Millions of people own smart home devices like the Amazon Echo and Echo Dot—equipped with the Alex cloud-based artificial intelligence service—which have concerning implications for privacy rights. While, Amazon’s own policies promise that only the user and Amazon will listen to what those devices record, it was recently reported that Amazon failed to follow its own policy when it erroneously shared one user’s information with a total stranger.
In August 2018, a German customer exercised his…
Content Type: Examples
A 19-year-old medical student was raped and drowned in the River Dresiam in October 2016. The police identified the accused by a hair found at the scene of the crime. The data recorded by the health app on his phone helped identify his location and recorded his activities throughout the day. A portion of his activity was recorded as “climbing stairs”, which authorities were able to correlate with the time he would have dragged his victim down the river embankment, and then climbed…
Content Type: Examples
The body of a 57-year-old was found in the laundry room of her home in Valley View, Adelaide, in September 2016. Her daughter-in-law who was in the house at the time of the murder claimed that she was tied up by a group of men who entered the house and managed to escape when they left. However, the data from the victim's smartwatch did not corroborate her story.The prosecution alleged that the watch had recorded data consistent with a person going into shock and losing consciousness. "The…
Content Type: Examples
The 90-year old suspect when to his stepdaughter's house at San Jose, California for a brief visit. Five days later, his stepdaugter's body, Karen was discovered by a co-worker in her house with fatal lacerations on her head and neck. The police used the data recorded by the victim's Fitbit fitness tracker to determine the time of the murder. It was been reported that the Fitbit data showed that her heart rate had spiked significantly around 3:20 p.m. on September 8, when her stepfather was…
Content Type: Examples
In 2017, US Immigration & Customs Enforcement (ICE) announced that it would seek to use artificial intelligence to automatically evaluate the probability of a prospective immigrant “becoming a positively contributing member of society.” In a letter to acting Department of Homeland Security Secretary Elaine Duke, a group of 54 concerned computer scientists, engineers, mathematicians, and researchers objected to ICE’s proposal and demanded that ICE abandon this approach because it would be…
Content Type: Examples
US Immigrations & Customs Enforcement (ICE) used social media monitoring to track groups and people in New York City associated with public events opposing the Trump administration’s policies, including ones related to immigration and gun control. The investigative branch of ICE created and circulated a spreadsheet, entitled ‘Anti-Trump Protest Spreadsheet 07/31/2018,” that provided details of events planned between July 31, 2018, and August 17, 2018. The spreadsheet pulled data from…
Content Type: Examples
The US government created a database of more than 50 journalists and immigrant rights advocates, many of whom were American citizens, associated with the journey of migrants travelling from Central America to the Mexico-US border in late 2018. Officials from Customs and Border Protection (CBP), Immigration and Customs Enforcement (ICE), the US Border Patrol, Homeland Security Investigations, and the Federal Bureau of Investigation (FBI) had access to this database. This list allowed the…
Content Type: Examples
On 14 May 2018, the husband of the victim, a pharmacist living in Linthorpe in Middlesbrough, subdued his wife with insulin injection before straggling her. He then ransacked the house to make it appear as a burglary. The data recorded by the health app on the murder’s phone, showed him racing around the house as he staged the burglary, running up and down the stairs. The victim’s app showed that she remained still after her death apart from a movement of 14 paces when her husband moved her…
Content Type: Examples
A private intelligence company, LookingGlass Cyber Solutions, used social media to monitor more than 600 “Family Separation Day Protests” held across the United States on June 30, 2018, to oppose the Trump administration’s policy family separation policy. The policy was part of a “zero tolerance” approach to deter asylum seekers from coming to the United States by separating children from their parents. After collecting information about these protests through Facebook, including the precise…
Content Type: Examples
Absher, an online platform and mobile phone app created by the Saudi Arabian government, can allow men to restrict women’s ability to travel, live in Saudi Arabia, or access government services. This app, which is available in the Google and Apple app stores, supports and enables the discriminatory male guardianship system in Saudi Arabia and violations of womens’ rights, including the right to leave and return to one’s own country. Because women in Saudi Arabia are required to have a male…
Content Type: Examples
A man from Middletown, Ohio, was indicted in January 2017 for aggravated arson and insurance fraud for allegedly setting fire to his home in September 2016. Ohio authorities decided and succeeded to obtain a search warrant for the data recorded on the pacemaker after identifying inconsistencies in the suspect’s account of facts. Ohio authorities alleged that the data showed that the accused was awake when he claimed to be sleeping. It has been reported that a cardiologist, examining data from…
Content Type: Examples
Bahrain has warned its citizens and residents could face legal action simply for following social media accounts it deems anti-government, which raises concerns about the ability of Bahraini citizens and residents to exercise their fundamental rights and freedoms. In May 2019, a state terrorism law was expanded to criminalise anyone “promoting, glorifying, justifying, approving or supporting acts which constitute terrorist activities,” whether within or outside Bahrain. The government’s…
Content Type: Advocacy
Faced with the transnational dimension of terrorist-related activities, United Nations Security Council resolutions have emphasized the need for international cooperation in information-sharing, both for the purposes of collecting intelligence and judicial assistance.
Privacy International recognises the importance and benefit of intelligence sharing in the context of preventing and investigating terrorism or other genuine, serious threats to national security. The organisation is concerned,…
Content Type: Long Read
Photo By: Cpl. Joel Abshier
‘Biometrics’ describes the physiological and behavioural characteristics of individuals. This could be fingerprints, voice, face, retina and iris patterns, hand geometry, gait or DNA profiles. Because biometric data is particularly sensitive and revealing of individual’s characteristics and identity, it can be applied in a massive number of ways – and has the potential to be gravely abused.
Identification systems across the world increasingly rely on…
Content Type: Advocacy
Identification system across the world increasingly rely on biometric data. In the context of border management, security and law enforcement, biometric data can play an important role in supporting the investigation and prevention of acts of terrorism.
This is clearly reflected in UN Security Council resolutions on counter- terrorism. Notably, Resolution 2396 (2017) the UN Security Council decided that states shall develop and implement systems to collect and share biometrics data for…
Content Type: Long Read
Whilst innovation in technology and data processing have provided individuals and communities with new opportunities to exercise their fundamental rights and freedoms, this has not come without risks, and these opportunities have not been enjoyed by all equally and freely.
Our relationships and interactions with governments and industry have become increasingly dependent on us providing more and more data and information about ourselves. And, it’s not only the information we provide knowingly…
Content Type: News & Analysis
Increasingly every interaction migrants have within the immigration enforcement framework requires the processing of their personal data. The use of this data and new technologies are today driving a revolution in immigration enforcement which risks undermining people's rights and requires urgent attention.
This is why Privacy International, and several migrant and digital rights organisation, joined a formal complaint filed by the Platform for International Cooperation on Undocumented…