Search
Content type: Impact Case Study
What HappenedOn 5 June 2013, The Guardian published the first in a series of documents disclosed by Edward Snowden, a whistleblower who had worked with the NSA. The documents revealed wide-ranging mass surveillance programs conducted by the USA’s National Security Agency (NSA) and the UK’s Government Communications Headquarters (GCHQ), which capture the communications and data of hundreds of millions of people around the world. In addition to revealing the mass surveillance programs of the NSA…
Content type: Advocacy
Este informe es presentado por Derechos Digitales, Ciudadano Inteligente, Fundación ProAcceso y Privacy International. Derechos Digitales es una organización no gubernamental de defensa, promoción y desarrollo de los derechos humanos en el entorno digital. Ciudadano Inteligente es una organización dedicada a fortalecer la democracia y reducir la desigualdad a través de la transparencia y la participación ciudadana. Fundación ProAcceso se dedica a la defensa del derecho de acceso a la…
Content type: Report
In December 2018, the National Coalition of Human Rights Defenders-Kenya published a report analysing the needs and concerns of human rights defenders (HRD) in relation to privacy, data protection and communications surveillance.
A summary of their findings is below. Access the full report on their website.
Content type: News & Analysis
This post was written by William Marks, a former volunteer at Privacy International.
The right to privacy is central to the protection of human dignity, and supports and reinforces other rights, such as the right to freedom of expression and association. Privacy International, supported by the International Human Rights Clinic at Harvard Law School, recently submitted a joint stakeholder report to the United Nations Human Rights Council regarding New Zealand’s protection of the right to…
Content type: Advocacy
This Universal Periodic Review stakeholder report is a submission by Privacy International presented to raise concerns regarding the situation of the violation of the right to privacy in New Zealand as part of the 32nd session of the Universal Periodic Review (UPR) Working Group.
Content type: News & Analysis
Our intervention comes on the back of mounting evidence that the South African state’s surveillance powers have been abused, and so-called “checks & balances” in RICA have failed to protect citizens’ constitutional right to privacy.
Among our core arguments are:
That people have a right to be notified when their communications have been intercepted so that they can take action when they believe their privacy has been unlawfully breached. Currently RICA prevents such notification, unlike…
Content type: Advocacy
This report is presented by Red en Defensa de los Derechos Digitales (R3D) and Privacy International (PI). La Red en Defensa de los Derechos Digitales (R3D) is a non-governmental, non-profit organisation located in Mexico, dedicated to the defence of human rights in the digital environment. Privacy International (PI) is a non-governmental, non-profit organisation located in London, focused on the defence, promotion and protection of the right to privacy around the world.
PI and R3D wish to…
Content type: Explainer graphic
Content type: Examples
In 2013, Edward Snowden, working under contract to the US National Security Agency for the consultancy Booz Allen Hamilton, copied and leaked thousands of classified documents that revealed the inner workings of dozens of previously unknown surveillance programs. One of these was PRISM, launched in 2007, which let NSA use direct access to the systems of numerous giant US technology companies to carry out targeted surveillance of the companies' non-US users and Americans with foreign contacts by…
Content type: News & Analysis
In order to uphold the law and keep us safe, the police can seriously interfere with a range of fundamental human rights. And so transparency and public scrutiny of their actions are essential to protect against misconduct and abuse.
So why is the National Police Chiefs’ Council (NPCC) now permitted to operate in secret?
We all have the right to seek information from most public bodies – including the police – under the Freedom of Information Act (FOIA) 2000. When the law was first…
Content type: Advocacy
Este informe es presentado por la Red en Defensa de los Derechos Digitales (R3D) y Privacy International (PI). La Red en Defensa de los Derechos Digitales (R3D) es una organización no gubernamental, sin fnes de lucro, ubicada en México, dedicada a la defensa de los derechos humanos en el entorno digital. Privacy International (PI) es una organización no gubernamental sin fnes de lucro ubicada en Londres enfocada en la defensa, promoción y protección del derecho a la privacidad alrededor del…
Content type: Advocacy
This Universal Periodic Review (“UPR”) stakeholder report is a submission by Privacy International and Paradigm Initiative.
Together Privacy International and Paradigm Initiative wish to bring their concerns about the protection and promotion of the right to privacy in Nigeria before the Human Rights Council for consideration in Nigeria’s upcoming review at the 31st session of the Working Group on the Universal Periodic Review.
Content type: Advocacy
This stakeholder report is a submission by Privacy International (PI) and the Jordan Open Source Association (JOSA).
Privacy International and the Jordan Open Source Association wish to bring concerns about the protection and promotion of the right to privacy for consideration in Jordan’s upcoming review at the 31st session of the Working Group on the Universal Periodic Review.
Content type: News & Analysis
En el 2011 se liquidó el DAS. Las violaciones, excesos y abusos de la inteligencia estatal que comenzaban por la intimidad y terminaban con la vida de los ciudadanos habían producido condenas judiciales a varios exdirectores: claro indicador de que se necesitaba un cambio. Siete años ha tenido el Estado colombiano para ordenar la casa y esta semana someterá sus récords de derechos humanos al examen de los miembros de Naciones Unidas. La evaluación analizará, entre otros…
Content type: News & Analysis
Los frecuentes escándalos sobre el abuso de la vigilancia estatal en actividades de inteligencia, la exagerada obligación legal que tienen las empresas de telefonía de retener los datos de las comunicaciones de sus usuarios por cinco años o la manera como se diluye el concepto de privacidad en el Código de Policía serán parte del examen que se haga en el seno de la ONU sobre la forma como Colombia cumple sus compromisos de derechos humanos.
Dirigido por los Estados y con el auspicio del…
Content type: News & Analysis
In the lead-up to the 30th session of the Universal Periodic Review which took place on 10 May 2018, Fundación Karisma, a partner organisation in the Privacy International Network, joined a coalition of civil society groups in Colombia to raise more awareness about the country's human rights record.
As part of the joint effort, the coalition produced factsheets on various human rights in the Colombian context, including the right to privacy. It is available in both English and Spanish.
Content type: Examples
A new examination of documents detailing the US National Security Agency's SKYNET programme shows that SKYNET carries out mass surveillance of Pakistan's mobile phone network and then uses a machine learning algorithm to score each of its 55 million users to rate their likelihood of being a terrorist. The documents were released as part of the Edward Snowden cache. The data scientist Patrick Ball, director of research at the Human Rights Data Analysis Group, which produces scientifically…
Content type: Impact Case Study
PI and our global partners have been at the forefront of challenging communications data retention for over a decade.
What is the problem
Communications data, also known as metadata, tells a story about your digital activity and answers the who, when, what, and how of a specific communication. While communications data doesn't include the contents of a message, all of the other information about the message can be very revealing about people, their habits, thoughts, health and personal…
Content type: Impact Case Study
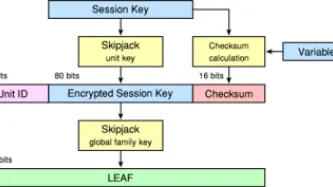
What happenedThe Clinton Administration kicked off the cypto-wars in 1993 with the Clipper Chip. The continued application of export controls restrained the deployment of strong cryptography in products at a key moment of internet history: as it began to be embedded in software and networking. What we didIn the early phases of the crypto-wars we placed pressure on global industry to implement encryption in their products. We ran campaigns and events across the world on the need for strong…
Content type: Impact Case Study
What is the problem
For over two decades we have been documenting an alarming use and spread of surveillance. It is no longer just the wars on terror or drugs or migration that is driving this trend. The management of health crises and distribution of welfare regularly are among others being used to justify this turn to increasingly invasive forms of surveillance. From country to country we see the same ideas and the same profiteers expanding their reach.
When we first released our report on…
Content type: Impact Case Study
What happenedIn the aftermath of 9/11, Governments across the world rushed to legislate to expand surveillance. GovernmentsMoved to limit debate and reduce consultations as they legislated with speed.Created new systems to collect data on all travellers, for the purpose of profiling and risk scoring.Expanded identity schemes, and began demanding biometrics, particularly at borders.Developed financial surveillance mechanisms on an unprecedented scale.What we didFew non-governmental…
Content type: Impact Case Study
What happenedGovernments continuously seek to expand their communications surveillance powers. In the 1990s it was in the context of applying telephone surveillance laws to the internet. In the 2000s a spate of new laws arrived in response to 9/11. Expansions were then sought to monitor over-the-top services within the framing of Web 2.0. Then in the post-Snowden environment Governments rushed to legislate their previously secret powers.What we didWe supported…
Content type: News & Analysis
Image was found here.
As part of Privacy International’s mission, we aim to take the issues emerging from our research and that of our partners to new spaces of debate and to the attention of stakeholders at the national, regional and international level.
In April 2018, Privacy International was able to engage for the first time with the African Commission on Human and People's Rights (ACHPR) at its 62nd Ordinary Session, which took place in Nouakchott, Mauritania.
The right to privacy does…
Content type: Advocacy
A new Privacy International report based on an international collaborative investigation carried out by 40 NGOs in 42 countries has found alarming weaknesses in the oversight arrangements that are supposed to govern the sharing of intelligence between state intelligence agencies, including in the UK. Privacy International urges governments to enact urgent reforms and improve public understanding about the scope of intelligence sharing and the safeguards and oversight currently in place.
Content type: Long Read
A major new report published today by Privacy International has identified alarming weaknesses in the oversight arrangements that are supposed to govern the sharing of intelligence between state intelligence agencies.
'Secret Global Surveillance Networks: Intelligence Sharing Between Governments and the Need for Safeguards' is based on an international collaborative investigation carried out by 40 NGOs in 42 countries.
Previously undisclosed documents obtained by PI via litigation in the…
Content type: Report
‘Secret Global Surveillance Networks’ is a major PI report, based on an unprecedented international collaborative investigation carried out by 40 NGOs in 42 countries.
Our research shows that, globally, the sharing of intelligence is alarmingly under-regulated, opening the door to human rights abuses. Intelligence sharing has evolved dramatically with the rise of new surveillance technologies, enabling governments to collect, store, and share vast troves of personal information, including data…
Content type: News & Analysis
El 10 de mayo de 2018, en el marco del 30º período de sesiones del Examen Periódico Universal (EPU) en el Consejo de Derechos Humanos de las Naciones Unidas, toca la revisión de Colombia, lo que es una oportunidad Colombia y otros Estados para declarar qué acciones han tomado para mejorar la situación de derechos humanos en sus propios países, para cumplir sus obligaciones internacionales en la materia.
Colombia se encuentra actualmente en un punto de inflexión, debido al proceso de transición…
Content type: News & Analysis
On 10 May 2018, Colombia’s human right record will be reviewed as part of the 30th session of the Universal Periodic Review (UPR), under the auspices of the Human Rights Council, which provides the opportunity for each State to declare what actions they have taken to improve the human rights situations in their countries and to fulfil their human rights obligations.
Colombia is at an important turning point in its history as it transitions from four decades of conflict. This provides…
Content type: Advocacy
On 6 March 2018, Privacy International participated in an interactive dialogue with the UN Special Rapporteur on the right to privacy at the 37th Ordinary Session of the Human Rights Council in Geneva. We highlighted the growing trend of governments embracing hacking to facilitate their surveillance activities, and recommended the development of a human rights analysis of government hacking for surveillance purposes, with the view to forming specific…
Content type: Advocacy
Este informe de terceras partes interesadas es una contribución escrita presentada por Dejusticia, Fundación Karisma y Privacy International (PI). Dejusticia es una organización de derechos humanos colombiana que brinda conocimientos especializados sobre derechos humanos. Fundación Karisma es una organización de la sociedad civil colombiana que busca dar respuesta a las oportunidades y a las amenazas que surgen en el contexto de la tecnología para el desarrollo para el ejercicio de los derechos…