Advanced Search
Content Type: Advocacy
Privacy International welcomes the UK House of Lord’s Justice and Home Affairs Committee’s investigation and subsequent report on electronic monitoring.The UK currently monitors some individuals who have interacted with the criminal justice system, and all individuals released on bail from immigration detention, through fitted GPS tags and non-fitted monitoring devices.In the immigration context, the Home Office touts electronic monitoring as a less restrictive way to maintain contact with…
Content Type: News & Analysis
Governments weaponising data against people is one of the top themes of 2025. In this latest example, tax agency uses post-9/11 era travel surveillance to administer tax benefits, and to wrongly accuse people of fraud.The UK Government has paused cuts to parents’ child benefits after it was revealed that one of its surveillance practices had made numerous mistakes.Her Majesty’s Revenue & Customs (HRMC), the UK tax agency, had suspended 23,500 payments to nearly 350 families, erroneously…
Content Type: Advocacy
On 3 July 2025, the General Conference of the International Labour Organization (ILO) adopted a resolution committing the ILO to adopt a Convention supplemented by a Recommendation concerning decent work in the platform economy following a second discussion on this issue in 2026. PI welcomes the ILO's decision as a step in the right direction to protect platform workers who have been at the forefront of new forms of data exploitation in the workplace as we have been documenting for many…
Content Type: Long Read
INTRODUCCIÓN
Desde hace algunos años, los modelos de negocio de las grandes plataformas tecnológicas han evolucionado a gran velocidad. A pesar de su posición dominante en varios mercados, los gigantes tecnológicos como Google y Meta están incursionando en nuevos territorios con el fin de ampliar su base de usuarios. Una de sus apuestas más llamativas ha sido su incursión en el “mercado de la conectividad” a través de cuantiosas, y en ocasiones fallidas, inversiones en infraestructura de red.…
Content Type: Long Read
In their gold rush to build cloud and AI tools, Big Tech is also enabling unprecedented government surveillance. Thanks to reporting from The Guardian, +972 Magazine, Local Call, and The Intercept, we have insights into the murky deals between the Israeli Government and Big Tech firms. Designed to insulate governments from scrutiny and accountability, these deals bode a dark future for humanity, one that is built using the same tools that once promised a bright, positive world.On 25 September…
Content Type: Long Read
On the basis of a year of legal research by PI as well as documents obtained by other civil society organisations, and evidence provided by legal representatives fighting these automated systems on behalf of their clients, on the 18th August 2025, we issued a formal complaint to the UK Information Commissioner (ICO) regarding the UK Home Office’s use of two ‘automated recommendation-making tools’ (ARMTs), the Identify and Prioritise Immigration Cases tool (IPIC) and the Electronic Monitoring…
Content Type: News & Analysis
Yesterday the Investigatory Powers Tribunal announced next steps in Apple’s and PI’s challenges to the purported UK order undermining iCloud’s security.The Tribunal declared that it will aim to hear much of Apple’s case, as well as PI and our co-claimants’, in public based on assumed facts. The Tribunal will convene a seven day hearing to be scheduled in early 2026. Its aim will be to hear Apple’s case and PI’s case during those seven days.This ‘case management order’ follows submissions from…
Content Type: News & Analysis
We’ve been warning for a while now about the risks of AI Assistants. Are these assistants designed for us or to exploit us?The answer to that question hinges on whether the firms building these tools are considering security and privacy from the outset. The initial launches over the last couple of years were not promising.Now with OpenAI’s agent launch, users deserve to know whether these firms are considering these risks and designing their service for people in the real world. The OpenAI…
Content Type: Long Read
In June 2025, a team of researchers exposed how Meta and Yandex abused Android and browser-specific tools to track users outside of their application and collect associated data. The technique used to achieve this was truly innovative, and akin to malware behaviour. It exploited protocols to break the isolation between apps and browser, a fundamental security concept meant to protect users. This allowed these companies to tie the browsing history of individuals with their accounts on the…
Content Type: Advocacy
The International Labour Organisation (ILO) is developing standards for decent work in the platform economy. Gig workers are exposed to a range of harms because of the precarious nature of their work and the use of opaque algorithms to manage them.Privacy International has come together with Human Rights Watch, TEDIC, IT for Change, Derechos Digitales and more than 30 other organisations to demand that this new ILO standard puts a stop to harmful practice, protects and promotes workers' rights…
Content Type: Long Read
Period tracking apps and the rollback of reproductive rightsThe aftermath of the overturning of Roe v. Wade in the United States (US) sparked widespread debate and concern that data from period tracking apps could be use to criminalise those seeking abortion care.While the surveillance and criminalisation of reproductive choices are neither new nor unique to the US, the scale and intensity of today’s crisis continue to grow. To put it into perspective, 22 million women and girls of reproductive…
Content Type: News & Analysis
Layla looks at her calendar on her phone. She’s in charge of planning her book club’s monthly meeting. After thinking for a second, she summons her AI assistant: “Hey Assistant, can you book me a table at that tapas restaurant I read about last week, and invite everyone from the book club? The restaurant should be in my browsing history. Let me know if the journey is more than 1-hour for anyone”. As the assistant compiles a response, she wonders if anyone else will hear this.Technology has made…
Content Type: Long Read
If you’ve ever used TikTok, Instagram, or X/Twitter, you will already be familiar with centralised social media.Centralised social media means big company owns the app, controls the software, and keeps all your data.For example, ByteDance makes TikTok. They own it, run the servers, decide what you see in your feed, and hold onto every video you like or comment on. They call the shots when it comes to your data.But what if social media didn’t work that way? What if no single company was in…
Content Type: Long Read
“Hey [enter AI assistant name here], can you book me a table at the nearest good tapas restaurant next week, and invite everyone from the book club?” Billions of dollars are invested in companies to deliver on this. While this is a dream that their marketing departments want to sell, this is a potential nightmare in the making.Major tech companies have all announced flavours of such assistants: Amazon’s Alexa+, Google’s Gemini inspired by Project Astra, Microsoft’s Copilot AI companion and…
Content Type: Press release
FOR IMMEDIATE RELEASELONDON - 7 April 2025The Investigatory Powers Tribunal (IPT) has confirmed it will hear Privacy International, Liberty and two individuals’ challenge to the legality of the Home Secretary’s decision to use her powers to secretly force Apple to allegedly give the UK Government access to users’ secured data stored on iCloud. The challenge will also cover the legality of the Government issuing these types of notices at all. Privacy International and Liberty,…
Content Type: News & Analysis
We’ve been asked a lot lately about whether it is safe to travel, particularly to the US. And it’s not surprising why: the US Government is increasing their cruelty at borders.Border management today is fueled by our data, but government officials want more. They want as much data as they can get to catch you out. They’ve reportedly detained or deported people based on their free speech activities, denying entry on tenuous grounds like having the wrong photos on phones (including in in the ‘…
Content Type: Long Read
On 13 March 2025, we filed a complaint against the UK government challenging their use of dangerous, disproportionate and intrusive surveillance powers to undermine the privacy and security of people all over the world. Here, we answer some key questions about the case and the recent events that led to this development.Note: This post was last updated on 13 March 2025.What’s the fuss about?A month ago, it was reported that the UK government demanded Apple Inc – maker of the iPhone, iPads, Macs…
Content Type: Advocacy
We believe the Government's position of refusing to confirm or deny the existence of the Technical Capability Notice or acknowledge Apple's appeal is untenable and violates principles of transparency and accountability.
Content Type: Explainer
Imagine this: a power that secretly orders someone anywhere in the world to abide and the receiver can’t tell anyone, can’t even publicly say if they disagree, and can’t really question the power in open court because the secret order is, well, secret. Oh and that power affects billions of people’s security and their data. And despite being affected, we too can’t question the secret order.In this piece we will outline what’s ridiculous, the absurd, and the downright disturbing about what’s…
Content Type: Long Read
IntroductionIn early October this year, Google announced its AI Overviews would now have ads. AI companies have been exploring ways to monetise their AI tools to compensate for their eye watering costs, and advertising seems to be a part of many of these plans. Microsoft have even rolled out an entire Advertising API for its AI chat tools.As AI becomes a focal point of consumer tech, the next host of the AdTech expansion regime could well be the most popular of these AI tools: AI chatbots.…
Content Type: Long Read
INTRODUCTION
In recent years, major tech platforms have been rapidly evolving their business models. Despite their dominance in various markets, tech giants like Google and Meta are venturing into new territories to expand their user base. One of the most striking ventures has been their foray into the "connectivity market" through substantial, and occasionally unsuccessful, investments in network infrastructure.
Many tech companies are investing resources into network infrastructure, either…
Content Type: Advocacy
In May 2024, we made a submission for the forthcoming report of the UN Special Rapporteur on the right to education to the General Assembly in October 2024.
Amongst others we recommend the UN Special Rapporteur for this upcoming report to:
Underline the need for a human rights-based approach to all AI systems in the education sector and describe the necessary measures to achieve it.
Reassert that any interference with the right to privacy and the advancement of the right to education due to…
Content Type: Long Read
Social media is now undeniably a significant part of many of our lives, in the UK and around the world. We use it to connect with others and share information in public and private ways. Governments and companies have, of course, taken note and built fortunes or extended their power by exploiting the digital information we generate. But should the power to use the information we share online be unlimited, especially for governments who increasingly use that information to make material…
Content Type: Video
The case dealt with a Russian law obliging telecommunications service providers to indiscriminately retain content and communications data for certain time periods, as well as a 2017 disclosure order by the Russian Federal Security Service requiring Telegram Messenger company to disclose technical information which would facilitate “the decoding of communications”.Links:PI case pageECtHR judgment in the Podchasov casePI's work on encryptionPI's report on End-to-End Encryption (E2EE)More…
Content Type: Advocacy
We are responding to the UK Government's consultation to expand its powers around Technical Capabilities Notices and National Security Notices.
Background
Following Edward Snowden's revelations about the illegal and expansive secret powers of the US and UK intelligence agencies, the UK Government took the opportunity to, rather than reflect on what powers are proportionate in the modern era, to expand its arsenal of surveillance powers.
One of the powers it added was the ability to issue…
Content Type: Advocacy
Privacy International welcomes the aim of the Cyber Resilience Act to bolster cybersecurity rules to ensure more secure hardware and software products. Nevertheless, we note that the proposal put forward by the European Commission contains certain shortcomings which could both hamper innovation and harm consumers who are increasingly relying on digital products and services.It is essential these shortcomings, detailed below, are effectively addressed by the EU co-legislators through the…
Content Type: Press release
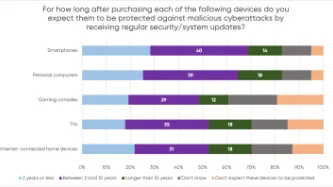
A YouGov survey commissioned by PI shows that consumers expect their smartphones, computers, smart TVs and gaming consoles to receive security updates for a much longer period than what several manufacturers actually provide, leaving consumers with expensive tech that is vulnerable to cyberattacks.
The majority of consumers in the survey assumed their devices would be protected beyond two years, but current industry practices fail to meet these expectations. PI investigated the software…
Content Type: Report
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content Type: Long Read
Introduction
In response to the unprecedented social, economic, and public health threats posed by the Covid-19 pandemic, the World Bank financed at least 232 "Covid-19 Response" projects. The projects were implemented across countries the World Bank classifies as middle and low-income.
This article will focus on eight (8) Covid-19 Response projects which sought to deliver social assistance to individuals and families on a "non-contributory" basis (this means that the intended beneficiaries…
Content Type: Video
Links
More information about how Bounty illegally exploited the data of 14 million mothers and babies: https://pvcy.org/podillegalexploitation
Sign up to our corporate exploitation email list to find out more about our work on brands and the advertising supply chain: https://pvcy.org/podsignup
Original podcast: https://privacyinternational.org/video/3787/podcast-marketing-and-maternity
----------
Orginally Recorded 12th March 2020.
We can’t believe we’re having to say…