Search
Content type: Long Read
We are living through a moment of profound transformation as military imperatives and corporate interests are no longer separate threads in the fabric of technological innovation. Instead they are inseparably interwoven. “Innovation” is increasingly framed not as a response to a concrete human need, but in terms of strategic advantage, deterrence, and national security. States and corporations alike are turning to technology which blurs the line between civilian life and military power to…
Content type: Report
Technologies that have both military and civilian applications are known as "dual-use”. Drone start-ups, arms giants, and satellite manufacturers are among the tech companies which are increasingly marketing surveillance products for both military and civil applications, leading to a blurring of the lines between the two domains. This has serious implications for our freedoms, and the militarisation of our societies, and the use of publicly-funded research.Exploring the growing influence of…
Content type: Report
Technologies that have both military and civilian applications are known as "dual-use”. Drone start-ups, arms giants, and satellite manufacturers are among the tech companies which are increasingly marketing surveillance products for both military and civil applications, leading to a blurring of the lines between the two domains. This has serious implications for our freedoms, the militarisation of our societies, and the use of publicly-funded research, particularly from the European Union.…
Content type: Long Read
In their gold rush to build cloud and AI tools, Big Tech is also enabling unprecedented government surveillance. Thanks to reporting from The Guardian, +972 Magazine, Local Call, and The Intercept, we have insights into the murky deals between the Israeli Government and Big Tech firms. Designed to insulate governments from scrutiny and accountability, these deals bode a dark future for humanity, one that is built using the same tools that once promised a bright, positive world.On 25 September…
Content type: Long Read
Go back to the full report pageLimitationsBefore our analysis, we note the technical limitations (and the scope of our research) meant we did not test certain features mentioned, such as Google Fit integrations offered by some apps. We also mention the limitations of our DIAS environment, which only allows us to see web (client-side) interactions, rather than server-side interactions, the latter of which are increasingly common among more advanced platforms that utilise cloud computing (e.…
Content type: Report
In this new briefing, we identify the most significant concerns on the UN Countering Terrorist Travel Programme (CTTP), and put forward a range of recommendations to mitigate some of the human rights risks associated with the surveillance of travellers. We based our briefing on publicly available information and our own research, outlining the purposes and activities of this UN programme. We shared a draft of this briefing with the United Nations Office of Counter- Terrorism (OCT), which…
Content type: Report
With this report, we shed light on the due process implications of the blanket and indiscriminate surveillance of protesters, activists, and human rights defenders participating in protests. We demonstrate that information gathered through the surveillance of protests is being used in criminal proceedings against activists, protesters, and human rights defenders. We also also show that when this information is being admitted as evidence in criminal proceedings it undermines the right to fair…
Content type: Long Read
Our briefing, “When Spiders Share Webs: The creeping expansion of INTERPOL’s interoperable policing and biometrics entrench externalised EU borders in West Africa”, explores the concerning human rights implications of the use of interoperable data-driven policing capabilities and biometric technologies in West African countries rolled out by the International Criminal Police Organisation (INTERPOL)’s European Union (EU)-funded West African Police Information System (WAPIS) programme. We make a…
Content type: Report
Content type: Report
Over the past years, data retention regulation imposing generalised and indiscriminate data retention obligations to telecommunication companies and Internet service provides has been introduced in various jurisdictions across the world. As the data retention practices across the world have evolved this new report is an attempt to shed some light on the current state of affairs in data retention regulation across ten key jurisdictions. Privacy International has consulted with human…
Content type: Report
The methodology employed for this report consists primarily of in-depth interviews held with grassroots political workers and representatives of collectives. The researchers interviewed 14 individuals from various social justice causes such as womens’ rights, climate change, transgender rights, students’ rights and the right to universal internet access in Pakistan. The experiences they have shared with the interviewers along with the real-time developments in the country’s law and order…
Content type: Report
This policy paper seeks to determine the potential for the existing international private military and security companies (PMSCs) regulatory framework to support more effective regulation of surveillance services provided by the private sector.In order to achieve this, and given that this paper addresses an issue that is at the intersection of two domains, it seeks to establish a common language and terminology between security sector governance and surveillance practitioners.In…
Content type: Long Read
The rise of racist and xenophobic narratives around the world has led to a ramping up of brutal migration control policies. Indefinite detention, pushbacks of boats at sea, or deportation for offshore processing of asylum claims all now form part of the arsenal deployed by some governments to “appear tough” on and provide "solutions" to immigration. A stark example is the UK’s “hostile environment” policy, announced 10 years ago by then Home Secretary Theresa May and designed to deter migrants…
Content type: Report
PI has been fighting against police using intrusive & disproportionate surveillance technologies at protests around the world for years. Unregulated surveillance and indiscriminate intrusions on our privacy have a chilling effect on the right to freedom of assembly.
We've fought to uncover the types of technologies that police secretly deploy at protests, and we have detailed how protesters around the world can try to protect their intimate and sensitive data from being captured by the…
Content type: Long Read
The rise of the gig-economy, a way of working relying on short term contracts and temporary jobs rather than on an employed workforce, has enabled the growth of a number of companies over the last few years. But without the rights that comes with full employment, gig economy workers today don't have access to essential protections.
In 2021, PI worked with ACDU and Worker Info Exchange to shed a light on the power imbalance between workers and gig economy platforms, exposing how workers find…
Content type: Report
In the months following the beginning of the Covid-19 pandemic, more than half the world’s countries enacted emergency measures. With these measures came an increase in executive powers, a suspension of the rule of law, and an upsurge in security protocols – with subsequent impacts on fundamental human rights. Within this broader context, we have seen a rapid and unprecedented scaling up of governments’ use of technologies to enable widespread surveillance. Surveillance technologies exacerbated…
Content type: Long Read
Introduction
India’s educational system is the largest in the world, with over 250 million students, 50% of whom attend publicly administered schools.
The autonomy given by the Indian Constitution to the 28 states and 8 union territories means that the right to education is implemented quite differently in each one, respecting culture, language, and other local specificities. Educational policies are suggested at the national level by various autonomous agencies and states can implement them in…
Content type: Report
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content type: Long Read
Introduction
In response to the unprecedented social, economic, and public health threats posed by the Covid-19 pandemic, the World Bank financed at least 232 "Covid-19 Response" projects. The projects were implemented across countries the World Bank classifies as middle and low-income.
This article will focus on eight (8) Covid-19 Response projects which sought to deliver social assistance to individuals and families on a "non-contributory" basis (this means that the intended beneficiaries…
Content type: Long Read
Imagine your performance at work was assessed directly from the amount of e-mails sent, the amount of time consumed editing a document, or the time spent in meetings or even moving your mouse. This may sound ludicrous but your boss might be doing exactly that. There are more and more stories emerging of people being called into meetings to justify gaps in their work only to find out their boss had been watching them work without their knowledge.
The Covid-19 global pandemic has reshuffled the…
Content type: Call to Action
Content type: Report
Privacy International’s submissions for the Independent Chief Inspector of Borders and Immigration inspection of the Home Office Satellite Tracking Service Programme
The Home Office have introduced 24/7 electronic monitoring and collection of the location data of migrants via GPS ankle tags. This seismic change cannot be overstated. The use of GPS tags and intention to use location data, kept for six years after the tag is removed, in immigration decision-making goes far beyond the mere…
Content type: Report
This briefing takes a look at the private intelligence industry, a collection of private detectives, corporate intel firms, and PR agencies working for clients around the world that have made London their hub.
Often staffed by ex-spooks, and promising complete secrecy, little is known about them. But reports over the years have exposed their operations, including things like hacking and targeting of anti-corruption officials, spying on peaceful environment activists, and running fake '…
Content type: Long Read
In a previous article, we mapped the influence of the Chinese company Huawei across the world and how their sales of smart city infrastructures are contributing to the reshaping of our public space.
We should be alarmed by some of their product deployments – such as the installation of facial recognition technologies in countries with concerning human rights records. But also the deployments of facial recognition technology in countries without strong data protection laws are as such…
Content type: Long Read
The smart city market is booming. And with a booming market comes companies that are profiting and reshaping our public space, like the Chinese tech company Huawei.
While the term ‘Smart City’ is a broad one that encompasses many different initiatives, some with little to no impact on our privacy and other rights. Certain issues are nevertheless recurrent: the lack of transparency around public-private partnerships, the absence of consultation, and the appetite for a “tech quick fix…
Content type: Video
<br />
Links
Find out more about PI's work with and on humanitarian organisations uses of data here: https://privacyinternational.org/learn/humanitarian-sector
Read more about the Humanitarian Metadata Problem in our report on doing no harm in the digital age co-authored with the ICRC here: https://privacyinternational.org/report/2509/humanitarian-metadata-problem-doing-no-harm-digital-era
And you can learn more about the history of…
Content type: Report
In this briefing, Amnesty International, PI and The Centre for Research on Multinational Corporations (SOMO) discuss the corporate structure of NSO group, one of the surveillance industry's well-known participants. The lack of transparency around NSO Group’s corporate structure and the lack of information about the relevant jurisdictions within which it operates are significant barriers in seeking prevention of, and accountability for, human rights violations reportedly linked to NSO Group’s…
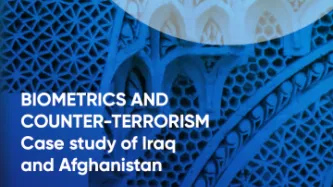
Content type: Report
In Afghanistan and Iraq, the U.S. Department of Defense developed its biometric program in confluence with US military operations in. Its expansion was tightly linked to the goals of military commanders during the “War on Terror”: to distinguish insurgents and terrorists from the local civilian population. This research shows how the DOD’s biometric programme was developed and implemented without prior assessment of its human rights impact and without the safeguards necessary to prevent its…
Content type: Report
In Israel/Palestine, the Israeli government has been deploying biometrics, including cutting-edge facial recognition technology, in the name of counter-terrorism. The Israeli state routinely surveils and severely restricts Palestinians’ freedom of movement using myriad technologies, including biometrics, which result in furthering the policies of systemic segregation. Since many Palestinians live under Israeli occupation, they have little control over the way their sensitive data is turned…
Content type: Long Read
Since the September 11th attacks, decision makers across the globe have embraced overreaching surveillance technologies. The global “War on Terror” ushered in and normalized an array of invasive surveillance technologies. Collection and storage of biometrics data and the application of statistical methods to such data have been touted as uniquely suited to twenty-first century threats. Yet, biometrics technologies are not seamless, panoptic technologies that allow for perfect control. They can…