Search
Content type: Explainer
Introduction
Of all the data-intensive initiatives that a government can introduce, some of the largest are ID systems. They have implications across a broad range of human and civil rights. How do we begin to critique an ID system, to begin to understand its strengths and weaknesses? There are a series of issues that we believe should be addressed in the development of any ID system.
This could be of particular relevance to civil society organisations (CSOs): this is because civil…
Content type: Long Read
The Privacy International Network is celebrating Data Privacy Week, where we’ll be talking about how trends in surveillance and data exploitation are increasingly affecting our right to privacy. Join the conversation on Twitter using #dataprivacyweek.
Innovations in surveillance and data exploitation present challenges in the fight to protect personal data across the world. Since 1990 we have been working to build a global movement through working with others - from leading civil society…
Content type: State of Privacy
Table of contents
Introduction
Right to Privacy
Communication Surveillance
Data Protection
Identification Schemes
Policies and Sectoral Initiatives
Introduction
Acknowledgement
The State of Privacy in Paraguay is the result of an ongoing collaboration by Privacy International and TEDIC in Paraguay.
Key privacy facts
1. Constitutional privacy protection: The constitution does not mention the word privacy but protects private life under the "right to intimacy."
2. Data protection…
Content type: State of Privacy
Table of contents
Introduction
Right to Privacy
Communication Surveillance
Data Protection
Identification Schemes
Policies and Sectoral Initiatives
Introduction
Acknowledgment
The State of Privacy in Lebanon is the result of an ongoing collaboration between Privacy International and SMEX.
Key privacy facts
1. Constitutional privacy protection: The Lebanon constitution does not explicitly mention the right to privacy.
2. Data protection law: The Electronic Transactions and…
Content type: State of Privacy
Table of contents
Introduction
Right to Privacy
Communication Surveillance
Data Protection
Identification Schemes
Policies and Sectoral Initiatives
Introduction
Acknowledgement
The State of Privacy in Colombia is the result of an ongoing collaboration by Privacy International and Fundación Karisma and Dejusticia.
Key Privacy Facts
1. Constitutional privacy protection: The constitution contains an explicit protection of the right to privacy (Article 15 of the 1991 constitution).
2…
Content type: State of Privacy
Table of contents
Introduction
Right to Privacy
Communication Surveillance
Data Protection
Identification Schemes
Policies and Sectoral Initiatives
Introduction
Acknowledgement
The State of Privacy in the Philippines is the result of an ongoing collaboration by Privacy International and Foundation for Media Alternatives.
Key privacy facts
1. Constitutional privacy protection: The constitution contains an explicit protection of the right to privacy (Art. III, section 3).
2.…
Content type: State of Privacy
Table of contents
Introduction
Right to Privacy
Communication Surveillance
Data Protection
Identification Schemes
Policies and Sectoral Initiatives
Introduction
Acknowledgment
The State of Surveillance in Morocco is the result of an ongoing collaboration by Privacy International and its partners.
Key privacy facts
1. Constitutional privacy protection: The constitution contains an explicit protection of the right to privacy.
2. Data protection law: There is a data…
Content type: State of Privacy
Table of contents
Introduction
Right to Privacy
Communication Surveillance
Data Protection
Identification Schemes
Policies and Sectoral Initiatives
Introduction
Acknowledgment
The State of Privacy in Indonesia is the result of an ongoing collaboration by Privacy International and The Institute for Policy Research and Advocacy (ELSAM).
Key privacy facts
Key privacy facts
1. Constitutional privacy protection: The constitution does not explicitly mention privacy.
2. Data protection…
Content type: State of Privacy
Table of contents
Introduction
Right to Privacy
Communication Surveillance
Data Protection
Identification Schemes
Policies and Sectoral Initiatives
Introduction
Acknowledgement
The State of Privacy in Brazil is the result of an ongoing collaboration by Privacy International and Coding Rights.
Between 2014-2017, Privacy LatAm contributed to previous versions of this briefing.
Key privacy facts
1. Constitutional privacy protection: The constitution contains an explicit…
Content type: State of Privacy
Introduction
Acknowledgement
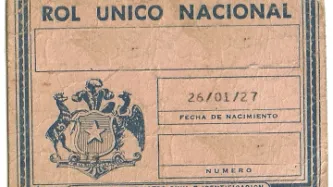
The State of Surveillance in Chile is the result of an ongoing collaboration between Privacy International and its Chilean partners Derechos Digitales and Fundación Datos Protegidos.
Key Privacy Facts
1. Constitutional privacy protections: Article 19 of Chile's constitution protects the right to a private life. It was reformed in 2018 to add a specific right to the protection of personal data.
2. Data protection laws: In 1999 Chile became the…
Content type: Explainer
Photo credit: warrenski
Mandatory SIM card registration eradicates the potential for anonymity of communications, enables location-tracking, and simplifies communications surveillance and interception. By facilitating the creation of an extensive database of user information, it places individuals at risk of being tracked or targeted, and having their private information misused. In the absence of comprehensive data protection legislation and judicial oversight, SIM users' information can be…
Content type: Examples
In May 2018, the ACLU of Northern California obtained documents under a FOIA request showing that Amazon was essentially giving away its two-year-old Rekognition facial recognition tools to law enforcement agencies in Oregon and Orlando, Florida. Amazon defended the move by saying the technology has many useful purposes, including finding abducted children and identify attendees at the 2018 wedding of Britain's Prince Harry and Meghan Markle. The company markets Rekognition as useful for…
Content type: Examples
In August 2018, two lawsuits, were filed against NSO Group, one brought in Israel by a Qatari citizen and the other in Cyprus by Mexican journalists and activists. All the plaintiffs had been targeted by the company's Pegasus spyware, which takes control of targets' phones when they click on links sent via carefully crafted phishing messages. The company claims that it sells the technology to governments on condition that they use it exclusively against criminals and it is not responsible for…
Content type: Examples
In August 2018, Facebook announced it would remove more than 5,000 ad targeting options in order to prevent discrimination. Options specifying the exclusion of people interested in "Passover", "Native American culture", or "Islam" could be used as proxies to allow advertisers to exclude ethnic and religious groups in contravention of the law. The announcement came shortly after the US Department of Housing and Urban Development filed a complaint alleging that the company had enabled…
Content type: Case Study
The exclusion caused by ID can have a devastating effect on people, limiting their opportunities and ability to survive.
Names have been changed.
Carolina is in a more privileged position than many other migrants, she admits that. She has a formal job, for one. She is – and has always been – in Chile legally: her previous visa has expired, and her new one is being processed. Under the law, she is permitted to stay and work in the country while this is happening. But she is finding the…
Content type: Case Study
Photo credit: Douglas Fernandes
The exclusion caused by ID can have a devastating effect on people, limiting their opportunities and ability to survive. In September 2018, Privacy International interviewed people in Santiago, Chile who had faced problems from the Chilean ID system, known as the RUT. Names have been changed.
It was never going to be easy for Liliana, entering Chile without a visa. But, in Chile, the ID system – known as the RUT – is ubiquitous; without one, as she would…
Content type: Long Read
Photo credit: Francisco Javier Argel
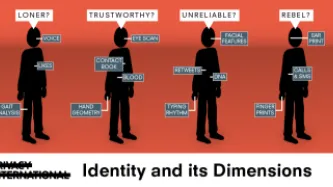
Questions of identification and ID, with their associated privacy risks, are only increasing. There are multiple dimensions to understanding the impact of ID and identification; a key one is to understand how it can exclude. This is why Privacy International is conducting research to explore this important and underreported aspect.
Read our case studies: Carolina and Iliana.
In the identity discourse, identity is often closely linked to themes of “…
Content type: News & Analysis
Photo Credit: Marion S. Trikosko
This month, the World Bank's Identity for Development (ID4D) initiative is launching its inaugural "Mission Billion Challenge", a competition designed to promote innovation in the identity space with the inaugural question: "How can digital identification systems in developing countries be designed to protect people’s privacy and provide them with greater control over their personal data?” But make no mistake: introducing "privacy by design" does…
Content type: App Analysis
This documentation demonstrates actions taken by the test user and the apps subsequent responses.
Test user action 1: The user taps on the application icon, which opens the application
Response from app: The application is initialised and the following data is sent and received by the app:
Immediately after the app is opened, the following data is sent to graph.facebook.com (Graph)
The following HTTP GET request is made to graph.facebook.com
GET https://graph.facebook.…
Content type: Long Read
It’s 15:10 pm on April 18, 2018. I’m in the Privacy International office, reading a news story on the use of facial recognition in Thailand. On April 20, at 21:10, I clicked on a CNN Money Exclusive on my phone. At 11:45 on May 11, 2018, I read a story on USA Today about Facebook knowing when teen users are feeling insecure.
How do I know all of this? Because I asked an advertising company called Quantcast for all of the data they have about me.
Most people will have never heard of…
Content type: News & Analysis
Privacy International notes a recent ruling issued by Italy’s Supreme Court (Corte di Cassazione) that addresses the need to limit government hacking powers for surveillance purposes and articulates required safeguards when hacking is conducted as part of a criminal investigation.
The ruling addresses the appeals of several individuals involved in a case of corruption; the appeals challenge irregularities in the collection of data as part of the criminal investigation, which resulted in the…
Content type: Long Read
Photo Credit: Max Pixel
The fintech sector, with its data-intensive approach to financial services, faces a looming problem. Scandals such as Cambridge Analytica have brought public awareness about abuses involving the use of personal data from Facebook and other sources. Many of these are the same data sets that the fintech sector uses. With the growth of the fintech industry, and its increase in power and influence, it becomes essential to interrogate this use of data by the…
Content type: Long Read
Image attribution: By Legaleagle86 at en.wikipedia, CC BY-SA 3.0.
In a long-anticipated judgment, the Indian Supreme Court has ruled that India's controversial identification system Aadhaar is Constitutional. They based their conclusion on notes that there are sufficient measures in place to protect data, and that it is difficult to undertake surveillance of citizens on the basis of Aadhaar.
But there is some good in this ruling. The court has demanded that the Government introduce…
Content type: Explainer
In the digital economy there is a trend towards corporate concentration. This is true for social media platforms, search engines, smart phone operating systems, digital entertainment, or online retailers. Meanwhile, the way in which market dominance is measured traditionally does not always capture the extent of their control: firstly, their products and services are often “free” and secondly, it’s often not clear in which “markets” and “sectors” these companies operate, since there is so much…
Content type: Long Read
The Sustainable Development Goals (SDGs) are the United Nations-led initiative to define the development agenda. Building on the eight Millennium Development Goals, the SDG’s 17 goals – and the 169 targets – serve as an opportunity to tackle many of the most pressing issues in the world today. The SDGs are also explicitly grounded in human rights. Goal 16 on “peace, justice, and sustainable institutions” aims to “Promote peaceful and inclusive societies for sustainable development, provide…
Content type: News & Analysis
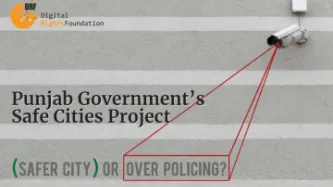
By Digital Rights Foundation, Pakistan
What is a safe city?
The answer to this question is not uniform; in fact it varies according to who you ask.
In a focus group conducted by Digital Rights Foundation in May of last year, consisting of women rights activists from across Pakistan, the answer meant imagining a city that was not only safe for women, in terms of their physical safety, but also welcoming for women and non-binary individuals in its architecture and facilities. Women expressed…
Content type: Long Read
Privacy and data protection are currently being debated more intensively than ever before. In this interview, Frederike Kaltheuner from the civil rights organisation Privacy International explains why those terms have become so fundamentally important to us. The article was first published in the newly launched magazine ROM. The interview was conducted by ROM publisher Khesrau Behroz and writers Patrick Stegemann and Milosz Paul Rosinski.
Frederike Kaltheuner, you work for Privacy…
Content type: Advocacy
Introduction
Why We Are So Concerned about Government Hacking for Surveillance
Scope of Our Safeguards
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4. Judicial Authorisation
5. Integrity of information
6. Notification
7. Destruction and Return of Data
8. Oversight and Transparency
9. Extraterritoriality
10. Effective Remedy
Commentary on each
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4.…
Content type: Explainer
“Smart city” is a marketing term used to define the use of technology – and in particular data collection – to improve the functioning of cities. The idea behind smart cities is that the more local governments know about city inhabitants the better the services they deliver will be. However, the reality is that the term means different things to different actors from companies to governments.
The World Bank suggests two possible definitions of smart cities. The first one is “a technology-…
Content type: News & Analysis
The following piece originally appeared on Linda Raftree's "Wait...What" blog, a site focusing on bridging community development and technology.
New technologies hold great potential for the developing world, and countless development scholars and practitioners have sung the praises of technology in accelerating development, reducing poverty, spurring innovation and improving accountability and transparency.
Worryingly, however, privacy is presented as a luxury that creates barriers…