Advanced Search
Content Type: Long Read
The final report on the 2022 Kenyan election is the result of a collaboration with the Carter Center as part of a joint pre-election assessment focussing on the use of technology in the run up to and during the Kenyan election which took place 9 August. The final report, published this month, follows our preliminary statement of September 2022.
Below we set out a few key observations in connection with the use of data and technology, as well as some of the key data protection incidents.
Key…
Content Type: Case Study
This piece was written by Privacy International, based on publicly available information and on research by our partners at Hiperderecho
Overview
The Documento Nacional de Identidad (DNI) is the personal ID card recognised by the Peruvian State in any situation where a person might have to identify themselves, be it in an administrative, judicial, civil, or commercial context. The DNI also grants its holder the right to vote.
The DNI issuing and overseeing body is the Registro Nacional de…
Content Type: Report
PI has been fighting against police using intrusive & disproportionate surveillance technologies at protests around the world for years. Unregulated surveillance and indiscriminate intrusions on our privacy have a chilling effect on the right to freedom of assembly.
We've fought to uncover the types of technologies that police secretly deploy at protests, and we have detailed how protesters around the world can try to protect their intimate and sensitive data from being captured by the…
Content Type: Long Read
The rise of the gig-economy, a way of working relying on short term contracts and temporary jobs rather than on an employed workforce, has enabled the growth of a number of companies over the last few years. But without the rights that comes with full employment, gig economy workers today don't have access to essential protections.
In 2021, PI worked with ACDU and Worker Info Exchange to shed a light on the power imbalance between workers and gig economy platforms, exposing how workers find…
Content Type: Report
In the months following the beginning of the Covid-19 pandemic, more than half the world’s countries enacted emergency measures. With these measures came an increase in executive powers, a suspension of the rule of law, and an upsurge in security protocols – with subsequent impacts on fundamental human rights. Within this broader context, we have seen a rapid and unprecedented scaling up of governments’ use of technologies to enable widespread surveillance. Surveillance technologies exacerbated…
Content Type: Long Read
Introduction
India’s educational system is the largest in the world, with over 250 million students, 50% of whom attend publicly administered schools.
The autonomy given by the Indian Constitution to the 28 states and 8 union territories means that the right to education is implemented quite differently in each one, respecting culture, language, and other local specificities. Educational policies are suggested at the national level by various autonomous agencies and states can implement them in…
Content Type: Report
Introduction
Several policy initiatives are in progress at the EU level. They seek to address the sustainability of connected devices such as smartphones, tablets and smart speakers. While initiatives to extend the useful life of hardware are important, software must not be ignored. Almost any digital device with which we interact today relies on software to function, which acts as a set of instructions that tells the hardware what to do. From smart thermostats to smart speakers, to our…
Content Type: Press release
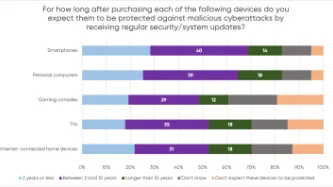
A YouGov survey commissioned by PI shows that consumers expect their smartphones, computers, smart TVs and gaming consoles to receive security updates for a much longer period than what several manufacturers actually provide, leaving consumers with expensive tech that is vulnerable to cyberattacks.
The majority of consumers in the survey assumed their devices would be protected beyond two years, but current industry practices fail to meet these expectations. PI investigated the software…
Content Type: Report
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content Type: Long Read
Introduction
In response to the unprecedented social, economic, and public health threats posed by the Covid-19 pandemic, the World Bank financed at least 232 "Covid-19 Response" projects. The projects were implemented across countries the World Bank classifies as middle and low-income.
This article will focus on eight (8) Covid-19 Response projects which sought to deliver social assistance to individuals and families on a "non-contributory" basis (this means that the intended beneficiaries…
Content Type: Long Read
The global COVID-19 health crisis not only induced a public health crisis, but has led to severe social, economic and educational crises which have laid bare any pre-existing gaps in social protection policies and frameworks. Measures identified as necessary for an effective public health response such as lockdowns have impacted billions workers and people's ability to sustain their livelihood worldwide, with countries seeing unprecedented levels of applications for welfare benefits support,…
Content Type: Long Read
Imagine your performance at work was assessed directly from the amount of e-mails sent, the amount of time consumed editing a document, or the time spent in meetings or even moving your mouse. This may sound ludicrous but your boss might be doing exactly that. There are more and more stories emerging of people being called into meetings to justify gaps in their work only to find out their boss had been watching them work without their knowledge.
The Covid-19 global pandemic has reshuffled the…
Content Type: Call to Action
Content Type: Report
Privacy International’s submissions for the Independent Chief Inspector of Borders and Immigration inspection of the Home Office Satellite Tracking Service Programme
The Home Office have introduced 24/7 electronic monitoring and collection of the location data of migrants via GPS ankle tags. This seismic change cannot be overstated. The use of GPS tags and intention to use location data, kept for six years after the tag is removed, in immigration decision-making goes far beyond the mere…
Content Type: Report
El informe se basa en investigación documental y empírica (cualitativa y cuantitativa) realizada por Privacy International (PI) en 2021. Más concretamente, PI envió una encuesta a varios reguladores antimonopolio y a organizaciones de la sociedad civil con sede y/o que operan en diversas partes del mundo.
Las preguntas planteadas a los reguladores y a la sociedad civil versaron sobre su trabajo en la economía digital. Se preguntó a los reguladores y a las OSC si incorporaban consideraciones…
Content Type: Report
The report builds on both desk and empirical (qualitative and quantitative) research that was carried out by Privacy International (PI) in 2021. Specifically, PI sent out a survey to several antitrust regulators and CSOs based and/or operating in various parts of the world. The questions posed to regulators and civil society revolved around their work in the digital economy. Regulators and CSOs were asked to comment on whether and how personal data considerations were incorporated into their…
Content Type: Report
This briefing takes a look at the private intelligence industry, a collection of private detectives, corporate intel firms, and PR agencies working for clients around the world that have made London their hub.
Often staffed by ex-spooks, and promising complete secrecy, little is known about them. But reports over the years have exposed their operations, including things like hacking and targeting of anti-corruption officials, spying on peaceful environment activists, and running fake '…
Content Type: Report
Democratic engagement is increasingly mediated by digital technology, from campaigning to election results transmission. A key example of the application of new technologies to democratic processes is the growing practice of micro-targeting in political campaigning around the globe, including Colombia.
In 2018, the mayor of Bogotá, Enrique Peñalosa, was accused of hiring Cambridge Analytica during his 2015 election campaign. That same year, Cambridge Analytica’s former director acknowledged…
Content Type: Long Read
In a previous article, we mapped the influence of the Chinese company Huawei across the world and how their sales of smart city infrastructures are contributing to the reshaping of our public space.
We should be alarmed by some of their product deployments – such as the installation of facial recognition technologies in countries with concerning human rights records. But also the deployments of facial recognition technology in countries without strong data protection laws are as such…
Content Type: Long Read
The smart city market is booming. And with a booming market comes companies that are profiting and reshaping our public space, like the Chinese tech company Huawei.
While the term ‘Smart City’ is a broad one that encompasses many different initiatives, some with little to no impact on our privacy and other rights. Certain issues are nevertheless recurrent: the lack of transparency around public-private partnerships, the absence of consultation, and the appetite for a “tech quick fix…
Content Type: Video
<br />
Links
Find out more about PI's work with and on humanitarian organisations uses of data here: https://privacyinternational.org/learn/humanitarian-sector
Read more about the Humanitarian Metadata Problem in our report on doing no harm in the digital age co-authored with the ICRC here: https://privacyinternational.org/report/2509/humanitarian-metadata-problem-doing-no-harm-digital-era
And you can learn more about the history of…
Content Type: Long Read
When you buy a brand-new low-cost phone, it’s likely to come pre-installed with insecure apps and an outdated operating system. What this means is that you or your loved ones could be left vulnerable to security risks or to having their data exploited. Privacy shouldn’t be a luxury. That’s why we advocate for companies to provide the latest security features and privacy protections for both low- and high-cost phones.
Content Type: Long Read
For many, browsing the internet or checking social media comes with its fair share of being targeted with ads selling “fad diet” subscription-based programmes, magic weight-loss powders, or promising a secret trick to lose weight quickly. Some of the products and programmes sold have been described as scams, with a very real impact for those suffering from eating disorders and those who fall prey to these ads. This is even more problematic due to the Covid-19 pandemic, which has seen the…
Content Type: Report
In this briefing, Amnesty International, PI and The Centre for Research on Multinational Corporations (SOMO) discuss the corporate structure of NSO group, one of the surveillance industry's well-known participants. The lack of transparency around NSO Group’s corporate structure and the lack of information about the relevant jurisdictions within which it operates are significant barriers in seeking prevention of, and accountability for, human rights violations reportedly linked to NSO Group’s…
Content Type: Report
In Somalia, international entities like the US Department of Defense (DoD) and intergovernmental organizations such as the United Nations (UN) have used biometrics in the name of counterterrorism, collecting and indefinitely storing biometric data, frequently in the absence of full disclosure or appropritate regulation. These biometric initiatives have had dubious benefits and known detrimental effects on local populations. Nevertheless, most Somalis have little knowledge or say over how their…
Content Type: Report
In Afghanistan and Iraq, the U.S. Department of Defense developed its biometric program in confluence with US military operations in. Its expansion was tightly linked to the goals of military commanders during the “War on Terror”: to distinguish insurgents and terrorists from the local civilian population. This research shows how the DOD’s biometric programme was developed and implemented without prior assessment of its human rights impact and without the safeguards necessary to prevent its…
Content Type: Report
In Israel/Palestine, the Israeli government has been deploying biometrics, including cutting-edge facial recognition technology, in the name of counter-terrorism. The Israeli state routinely surveils and severely restricts Palestinians’ freedom of movement using myriad technologies, including biometrics, which result in furthering the policies of systemic segregation. Since many Palestinians live under Israeli occupation, they have little control over the way their sensitive data is turned…
Content Type: Long Read
Since the September 11th attacks, decision makers across the globe have embraced overreaching surveillance technologies. The global “War on Terror” ushered in and normalized an array of invasive surveillance technologies. Collection and storage of biometrics data and the application of statistical methods to such data have been touted as uniquely suited to twenty-first century threats. Yet, biometrics technologies are not seamless, panoptic technologies that allow for perfect control. They can…
Content Type: Long Read
Summary
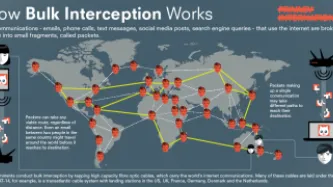
This case began in the UK in 2013, following Edward Snowden’s revelations that UK’s GCHQ was secretly intercepting, processing, and storing data concerning millions of people’s private communications, even when those people were of clearly of no intelligence interest (the ‘Tempora’ programme). It was also revealed that the UK government was accessing communications and data collected by the USA’s National Security Agency and other countries’ intelligence agencies. All of this was…