Advanced Search
Content Type: Long Read
On the basis of a year of legal research by PI as well as documents obtained by other civil society organisations, and evidence provided by legal representatives fighting these automated systems on behalf of their clients, on the 18th August 2025, we issued a formal complaint to the UK Information Commissioner (ICO) regarding the UK Home Office’s use of two ‘automated recommendation-making tools’ (ARMTs), the Identify and Prioritise Immigration Cases tool (IPIC) and the Electronic Monitoring…
Content Type: Long Read
In June 2025, a team of researchers exposed how Meta and Yandex abused Android and browser-specific tools to track users outside of their application and collect associated data. The technique used to achieve this was truly innovative, and akin to malware behaviour. It exploited protocols to break the isolation between apps and browser, a fundamental security concept meant to protect users. This allowed these companies to tie the browsing history of individuals with their accounts on the…
Content Type: News & Analysis
Layla looks at her calendar on her phone. She’s in charge of planning her book club’s monthly meeting. After thinking for a second, she summons her AI assistant: “Hey Assistant, can you book me a table at that tapas restaurant I read about last week, and invite everyone from the book club? The restaurant should be in my browsing history. Let me know if the journey is more than 1-hour for anyone”. As the assistant compiles a response, she wonders if anyone else will hear this.Technology has made…
Content Type: Long Read
“Hey [enter AI assistant name here], can you book me a table at the nearest good tapas restaurant next week, and invite everyone from the book club?” Billions of dollars are invested in companies to deliver on this. While this is a dream that their marketing departments want to sell, this is a potential nightmare in the making.Major tech companies have all announced flavours of such assistants: Amazon’s Alexa+, Google’s Gemini inspired by Project Astra, Microsoft’s Copilot AI companion and…
Content Type: Press release
FOR IMMEDIATE RELEASELONDON - 7 April 2025The Investigatory Powers Tribunal (IPT) has confirmed it will hear Privacy International, Liberty and two individuals’ challenge to the legality of the Home Secretary’s decision to use her powers to secretly force Apple to allegedly give the UK Government access to users’ secured data stored on iCloud. The challenge will also cover the legality of the Government issuing these types of notices at all. Privacy International and Liberty,…
Content Type: Long Read
On 13 March 2025, we filed a complaint against the UK government challenging their use of dangerous, disproportionate and intrusive surveillance powers to undermine the privacy and security of people all over the world. Here, we answer some key questions about the case and the recent events that led to this development.Note: This post was last updated on 13 March 2025.What’s the fuss about?A month ago, it was reported that the UK government demanded Apple Inc – maker of the iPhone, iPads, Macs…
Content Type: Advocacy
We believe the Government's position of refusing to confirm or deny the existence of the Technical Capability Notice or acknowledge Apple's appeal is untenable and violates principles of transparency and accountability.
Content Type: Explainer
Imagine this: a power that secretly orders someone anywhere in the world to abide and the receiver can’t tell anyone, can’t even publicly say if they disagree, and can’t really question the power in open court because the secret order is, well, secret. Oh and that power affects billions of people’s security and their data. And despite being affected, we too can’t question the secret order.In this piece we will outline what’s ridiculous, the absurd, and the downright disturbing about what’s…
Content Type: News & Analysis
Is the AI hype fading? Consumer products with AI assistant are disappointing across the board, Tech CEOs are struggling to give examples of use cases to justify spending billions into Graphics Processing Units (GPUs) and models training. Meanwhile, data protection concerns are still a far cry from having been addressed.
Yet, the believers remain. OpenAI's presentation of ChatGPT was reminiscent of the movie Her (with Scarlett Johannsen's voice even being replicated a la the movie), Google…
Content Type: Advocacy
We are responding to the UK Government's consultation to expand its powers around Technical Capabilities Notices and National Security Notices.
Background
Following Edward Snowden's revelations about the illegal and expansive secret powers of the US and UK intelligence agencies, the UK Government took the opportunity to, rather than reflect on what powers are proportionate in the modern era, to expand its arsenal of surveillance powers.
One of the powers it added was the ability to issue…
Content Type: Advocacy
Privacy International welcomes the aim of the Cyber Resilience Act to bolster cybersecurity rules to ensure more secure hardware and software products. Nevertheless, we note that the proposal put forward by the European Commission contains certain shortcomings which could both hamper innovation and harm consumers who are increasingly relying on digital products and services.It is essential these shortcomings, detailed below, are effectively addressed by the EU co-legislators through the…
Content Type: Video
<br />
Links
Read more about the ICO's provisional decision
Support our work
You can find out more about Clearview by listening to our podcast: The end of privacy? The spread of facial recognition
Content Type: Advocacy
Our environment is increasingly populated by devices connected to the Internet, from computers and mobile phones to sound systems and TVs to fridges, kettles, toys, or domestic alarms. There has been research into the negative safety and privacy impacts of inadequate security provided by the software in such devices (such as the creation of large scale botnets). This is also the case with outdated security, a risk enabled by software support periods that are shorter than a product’s usable life…
Content Type: News & Analysis
Unwanted Witness’ research into Safeboda highlighted the company’s failure to comply with some of the law's core data protection principles, with a number of implications for the exercise of data subject rights. The enforcement action against Safeboda by National Information Technology Authority, Uganda (NITA-U) requires the company to make fundamental changes to how they handle people's personal data in order to comply with the Data Protection and Privacy Act, 2019.
This first landmark…
Content Type: Long Read
In 2019, we exposed the practices of five menstruation apps that were sharing your most intimate data with Facebook and other third parties. We were pleased to see that upon the publication of our research some of them decided to change their practices. But we always knew the road to effective openness, transparency, informed consent and data minimisation would be a long one when it comes to apps, which for the most part make profit from our menstrual cycle and even sometimes one’s desire to…
Content Type: Frequently Asked Questions
On 27 October 2020, the UK Information Commissioner's Office (ICO) issued a report into three credit reference agencies (CRAs) - Experian, Equifax and TransUnion - which also operate as data brokers for direct marketing purposes.
After our initial reaction, below we answer some of the main questions regarding this report.
Content Type: News & Analysis
Samsung has announced that the company will commit to providing major software updates for three generations of the Android operating system, but only for its flagship models: the S10, S20, Note 10 and Note 20.
From our reading of the available information, this means that these models will be getting support, including the latest operating system, features and security updates, for three years (as new Android operating systems are released every year).
While this is welcome news, it only…
Content Type: Explainer
At first glance, infrared temperature checks would appear to provide much-needed reassurance for people concerned about their own health, as well as that of loved ones and colleagues, as the lockdown is lifted. More people are beginning to travel, and are re-entering offices, airports, and other contained public and private spaces. Thermal imaging cameras are presented as an effective way to detect if someone has one of the symptoms of the coronavirus - a temperature.
However, there is little…
Content Type: News & Analysis
New technologies continue to present great risks and opportunities for any users but for some communities the implications and harms can have severe consequences and one of the sectors facing increasing challenges to keep innovating whilst protecting themselves and the people they serve is the humanitarian sector.
Over the course of engagement with the humanitarian sector, one of our key observations has been how risk assessments undertaken in the sector omitted to integrate a hollistic…
Content Type: News & Analysis
In September 2019, PI published the report Your Mental Health for Sale. Our investigation looked into popular mental health websites and their data sharing practices.
Our findings suggest that, at the time of the research, most websites we looked at were using third party tracking for advertising purposes, sometimes relying on programmatic advertising technologies such as Real Time Bidding (RTB), sharing personal data with potentially thousands of actors. Some websites were also found sharing…
Content Type: Call to Action
You might have read our investigation into advertisers who upload your data on Facebook and found out some companies doing the same to you. Well, you can join us and hold them accountable by sending your own Data Subject Access Request (DSAR)!Before you get started we suggest you read our FAQ and take a look at our 7+1 tips to make the most out of your DSAR before and after.To do so you simply need to copy the message bellow and send it to the companies that uploaded your data despite…
Content Type: Report
Back in October 2019, PI started investigating advertisers who uploaded personal data to Facebook for targeted advertising purposes. We decided to take a look at "Advertisers Who Uploaded a Contact List With Your Information", a set of information that Facebook provides to users about advertisers who upload files containing their personal data (including unique identifier such as phone numbers, emails etc...). Looking at the limited and often inaccurate information provided by Facebook through…
Content Type: Examples
Academics have disclosed today a new vulnerability in the Bluetooth wireless protocol, broadly used to interconnect modern devices, such as smartphones, tablets, laptops, and smart IoT devices.
The vulnerability, codenamed BIAS (Bluetooth Impersonation AttackS), impacts the classic version of the Bluetooth protocol, also known as Basic Rate / Enhanced Data Rate, Bluetooth BR/EDR, or just Bluetooth Classic.
The BIAS attack
The BIAS security flaw resides in how devices handle the link key,…
Content Type: Explainer
In a scramble to track, and thereby stem the flow of, new cases of COVID-19, governments around the world are rushing to track the locations of their populace.
In this third installment of our Covid-19 tracking technology primers, we look at Satellite Navigation technology. In Part 1 of our mini-series on we discussed apps that use Bluetooth for proximity tracking. Telecommunications operators ('telcos'), which we discussed in Part 2, are also handing over customer data, showing the cell towers…
Content Type: Long Read
This week saw the release of a coronavirus tracking app within the United Kingdom, initially to be trialled in the Isle of Wight. Privacy International has been following this closely, along with other ‘track and trace’ apps like those seen in over 30 other countries.
The UK’s app is no different. It is a small part of a public health response to this pandemic. As with all the other apps, it is vital that it be integrated with a comprehensive healthcare response, prioritise people, and…
Content Type: News & Analysis
A few weeks ago, its name would probably have been unknown to you. Amidst the covid-19 crisis and the lockdown it caused, Zoom has suddenly become the go-to tool for video chat and conference calling, whether it’s a business meeting, a drink with friends, or a much needed moment with your family. This intense rise in use has been financially good to the company, but it also came with a hefty toll on its image and serious scrutiny on its privacy and security practices.
While Zoom already had a…
Content Type: Examples
An engineering and computer science professor and his team from The Ohio State University discovered a design flaw in low-powered Bluetooth devices that leaves them susceptible to hacking.
Zhiqiang Lin, associate professor of computer science and engineering at the university, found the commonly used Bluetooth Low Energy devices, such as fitness trackers and smart speakers, are vulnerable when they communicate with their associated apps on the owner’s mobile phone.
"There is a fundamental…
Content Type: Explainer
In a scramble to track, and thereby stem the flow of, new cases of Covid-19, Governments around the world are rushing to track the locations of their populace. One way to do this is to write a smartphone app which uses Bluetooth technology, and encourage (or mandate) that individuals download and use the app. We have seen such examples in Singapore and emerging plans in the UK.
Apps that use Bluetooth are just one way to track location. There are several different technologies in a smartphone…
Content Type: Long Read
Valentine’s Day is traditionally a day to celebrate relationships, but many relationships that begin romantically can quickly become controlling, with partners reading emails, checking texts and locations of social media posts. This can be just the beginning.
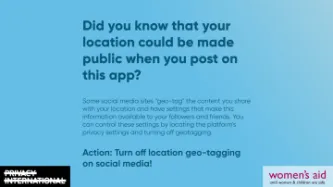
Today, Friday 14th February, Privacy International and Women’s Aid are launching a series of digital social media cards giving women practical information on how to help stay safe digitally from control and abuse.
Did you know…