Advanced Search
Content Type: Examples
Article extract:
"Anti-smoking campaigners have expressed alarm that "big tobacco" has been employing two of the world's most powerful lobbying companies in a bid to stymie the introduction of plain packaging for cigarettes.
Crosby Textor, which has been hired by the Conservative party to provide "strategic direction" at the next election, has played a powerful behind-the-scenes role in mobilising opposition to the Australian government's plans for plain packaging, which became law on…
Content Type: Examples
Article extract:
"The lobbying firm founded by election guru Lynton Crosby is reported to have advised private healthcare providers on how to exploit failings in the NHS..."
"...Crosby Textor advised an umbrella group of private healthcare providers on how to exploit perceived “failings”, according to a leaked document obtained by the Guardian.
The newspaper published extracts from a slideshow presentation produced for the H5 Private Healthcare Alliance, which stated that people believe the…
Content Type: Examples
Article extract:
"The lobbying firm run by Boris Johnson’s close ally Sir Lynton Crosby has secretly built a network of unbranded “news” pages on Facebook for dozens of clients ranging from the Saudi government to major polluters, a Guardian investigation has found.
In the most complete account yet of CTF Partners’ outlook and strategy, current and former employees of the campaign consultancy have painted a picture of a business that appears to have professionalised online disinformation,…
Content Type: Long Read
Introduction
A growing number of governments around the world are embracing hacking to facilitate their surveillance activities. Yet hacking presents unique and grave threats to our privacy and security. It is far more intrusive than any other surveillance technique, capable of accessing information sufficient to build a detailed profile of a person, as well as altering or deleting that information. At the same time, hacking not only undermines the security of targeted systems, but also has…
Content Type: Long Read
This piece was orignally published in Slate in February 2017
In 2015, the FBI obtained a warrant to hack the devices of every visitor to a child pornography website. On the basis of this single warrant, the FBI ultimately hacked more than 8,700 computers, resulting in a wave of federal prosecutions. The vast majority of these devices—over 83 percent—were located outside the United States, in more than 100 different countries. Now, we are in the midst of the first cases…
Content Type: Long Read
This piece was written by Ashley Gorski, who is an attorney at the American Civil Liberties Union, and PI legal officer Scarlet Kim and originally appeared in The Guardian here.
In recent weeks, the Hollywood film about Edward Snowden and the movement to pardon the NSA whistleblower have renewed worldwide attention on the scope and substance of government surveillance programs. In the United States, however, the debate has often been a narrow one, focused on the…
Content Type: Long Read
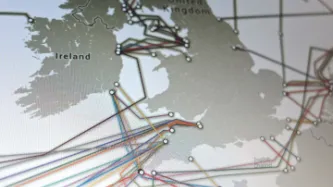
This week, Privacy International, together with nine other international human rights NGOs, filed submissions with the European Court of Human Rights. Our case challenges the UK government’s bulk interception of internet traffic transiting fiber optic cables landing in the UK and its access to information similarly intercepted in bulk by the US government, which were revealed by the Snowden disclosures. To accompany our filing, we have produced two infographics to illustrate the…
Content Type: Long Read
This piece originally appeared here.
On both sides of the Atlantic, we are witnessing the dramatic expansion of government hacking powers. In the United States, a proposed amendment to Rule 41 of the Federal Rules of Criminal Procedure would permit the government to obtain a warrant, in certain circumstances, to hack unspecified numbers of electronic devices anywhere in the world. Meanwhile, across the pond, the British Parliament is currently debating the Investigatory…
Content Type: Long Read
Few revelations have been been as troubling for the right to privacy as uncovering the scope of the Five Eyes alliance. The intelligence club made up of Australia, Canada, New Zealand, the United Kingdom and the United States has integrated its collection efforts, staff, bases, and analysis programs. Yet the legal rulebook governing how the agencies ensure the most comprehensive joint surveillance effort in the history of mankind remains secret.
The little that is known suggests a…
Content Type: Long Read
Many people imagine intelligence sharing to be a practice whereby men in trench coats silently slide manilla envelopes containing anonymous tip-offs or intelligence reports marked TOP SECRET across tables in smoke-filled rooms.
While such practices certainly exist, they represent only a tiny slice of intelligence sharing activities, and are vastly overshadowed by the massive exchange of bulk unanlysed (raw) intelligence data that takes place between the UK and its Five Eyes allies.…
Content Type: Long Read
Bad analogies about surveillance technology pervade newspaper reports, politicians’ speeches, and legal arguments. While it’s natural to want simple explanations to understand complex technology, it does us a disservice when governments, the media, or the courts mislead us through analogies that are inadequate. It is even worse if these analogies are used as a basis for policy change.
Privacy International’s legal challenge against GCHQ’s mass surveillance rests…
Content Type: Long Read
The recent revelations, made possible by NSA-whistleblower Edward Snowden, of the reach and scope of global surveillance practices have prompted a fundamental re- examination of the role of intelligence services in conducting coordinated cross-border surveillance.
The Five Eyes alliance of States – comprised of the United States National Security Agency (NSA), the United Kingdom’s Government Communications Headquarters (GCHQ), Canada’s Communications Security Establishment Canada (CSEC), the…
Content Type: Report
The recent revelations, made possible by NSA-whistleblower Edward Snowden, of the reach and scope of global surveillance practices have prompted a fundamental re-examination of the role of intelligence services in conducting coordinated cross-border surveillance.
The Five Eyes alliance of States – comprised of the United States National Security Agency (NSA), the United Kingdom’s Government Communications Headquarters (GCHQ), Canada’s Communications Security Establishment Canada (CSEC), the…
Content Type: News & Analysis
With the launch of the "Eyes Wide Open" project, Privacy International has put together a fact sheet about the secretive Five Eyes alliance. Consider this a guide to the secret surveillance alliance that has infiltrated every aspect of the modern global communications system.
Beginning in 1946, an alliance of five English-speaking countries (the US, the UK, Australia, Canada and New Zealand) developed a series of bilateral agreements over more than a decade that became known as the UKUSA…
Content Type: Long Read
Britain's spy agency, GCHQ, is secretly conducting mass surveillance by tapping fibre optic cables, giving it access to huge amounts of data on both innocent citizens and targeted suspects, according to a report in the Guardian.
Mass, indiscriminate surveillance of this kind goes against an individual's fundamental human right to privacy. The scope and scale of this program, which monitors the entire British public and much of the world, is neither necessary nor proportionate and thus,…