Search
Content type: News & Analysis
Lockdowns and quarantines are an extraordinary measure that help in slowing down the global COVID-19 pandemic, and protecting the population.
However, they come at an even higher cost to some individuals, such as victims of domestic violence, persons in a vulnerable situation, and human rights defenders, who face specific threats that are exacerbated by measures taken by governments to address the global pandemic.
In that context, states should adopt special measures to keep those people…
Content type: News & Analysis
Amid calls from international organisations and civil society urging for measures to protect the migrant populations in Greece and elsewhere, last week, the European Commission submitted a draft proposal to amend the general budget 2020 in order to, among other measures, provide assistance to Greece in the context of the COVID-19 outbreak.
Both at the Turkish-Greek border and in the camps on the Greek islands, there are severe concerns not only about the dire situation in which these people…
Content type: Case Study
In Peru, you get asked for your fingerprint and your ID constantly - when you’re getting a new phone line installed or depositing money in your bank account – and every Peruvian person has an ID card, and is included in the National Registry of Identity – a huge database designed to prove that everyone is who they say they are. After all, you can change your name, but not your fingerprint.
However, in 2019 the National Police of Peru uncovered a criminal operation that was doing just that:…
Content type: Advocacy
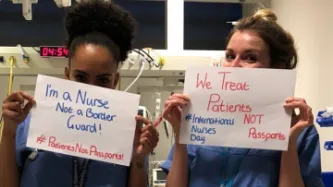
The letter has been signed by more than 40 organisations and it is open for individuals to sign.
At the moment, the Department of Health and Social Care has given no assurance that NHS data will not be shared with the Home Office and used for immigration enforcement, including for those people with a confirmed coronavirus diagnosis.
Assurances which were confirmed by the Irish government as part of their response to COVID-19: last week, during a Parliamentary debate, Irish Minister of Health…
Content type: Case Study
There are 29.4 million refugees and asylum seekers across the globe today. These are people who have fled their countries due to conflict, violence or persecution seeking protection in safer environments.
People have protected those in need fleeing from dire situations since antiquity. However, over recent years, European countries have become increasingly hostile towards refugees - treating them as criminals instead of people in need.
In 2017, German authorities passed a…
Content type: Case Study
The increasing deployment of highly intrusive technologies in public and private spaces such as facial recognition technologies (FRT) threaten to impair our freedom of movement. These systems track and monitor millions of people without any regulation or oversight.
Tens of thousands of people pass through the Kings Cross Estate in London every day. Since 2015, Argent - the group that runs the Kings Cross Estate - were using FRT to track all of those people.
Police authorities rushed in secret…
Content type: Case Study
In 2015, James Bates was charged with first-degree murder in the death of Victor Collins. Collins was found floating face down in Bates’ hot tub in November 2015. Bentonville police served two search warrants ordering Amazon to turn over the “electronic data in the form of audio recordings, transcribed records, text records and other data contained on the Amazon Echo device” in Bates’ home.
The reason for the warrants? According to the police, just because the device was in the house that…
Content type: News & Analysis
Today, the District Court of the Hague ruled that the right to privacy prevailed over the hunt against alleged benefits fraudsters. The ruling could have huge implications for the future of digital welfare around the world.
In NJCM cs/ De Staat der Nederlanden (NJCM vs the Netherlands), also known as the SyRI case, the court considered the legality of the System Risk Indication (SyRI), a system designed by the Dutch government to process large amounts of data collected by various Dutch public…
Content type: News & Analysis
In mid-2019, MI5 admitted, during a case brought by Liberty, that personal data was being held in “ungoverned spaces”. Much about these ‘ungoverned spaces’, and how they would effectively be “governed” in the future, remained unclear. At the moment, they are understood to be a ‘technical environment’ where personal data of unknown numbers of individuals was being ‘handled’. The use of ‘technical environment’ suggests something more than simply a compilation of a few datasets or databases.
The…
Content type: News & Analysis
On 30 January 2020, Kenya’s High Court handed down its judgment on the validity of the implementation of the National Integrated Identity Management System (NIIMS), known as the Huduma Namba. Privacy International submitted an expert witness testimony in the case. We await the final text of the judgment, but the summaries presented by the judges in Court outline the key findings of the Court. Whilst there is much there that is disappointing, the Court found that the implementation of NIIMS…
Content type: Case Study
Every one of us has an expectation to be legally protected in the same way, to have access to the same human rights, and to be able to defend those rights in court.
However, for trans and non-binary people, this has not always been the case – and in many places around the world it still isn’t the case. The lack of legal recognition for their gender has had significant consequences.
If the law does not recognise you as the person that you are and treats you as someone you are not then you…
Content type: News & Analysis
Today Advocate General (AG) Campos Sánchez-Bordona of the Court of Justice of the European Union (CJEU), issued his opinions (C-623/17, C-511/18 and C-512/18 and C-520/18) on how he believes the Court should rule on vital questions relating to the conditions under which security and intelligence agencies in the UK, France and Belgium could have access to communications data retained by telecommunications providers.
The AG addressed two major questions:
(1) When states seek to impose…
Content type: Case Study
Slavery, servitude, and forced labour are absolutely forbidden today, as is anything that seeks to undermine or limit that restriction. The horrific reality, however, is that modern slavery remains a significant global issue.
Human trafficking is one form of modern slavery. It involves the recruitment, harbouring or transporting of people into a situation of exploitation through the use of violence, deception or coercion and forcing them to work against their will.
Human traffickers do…
Content type: Case Study
On 3 December 2015, four masked men in plainclothes arrested Isnina Musa Sheikh in broad daylight (at around 1 p.m.) as she served customers at her food kiosk in Mandera town, in the North East of Kenya, Human Rights Watch reported. The men didn’t identify themselves but they were carrying pistols and M16 assault rifles, commonly used by Kenyan defence forces and the cars that took her away had their insignia on the doors. Isnina’s body was discovered three days later in a shallow grave about…
Content type: Case Study
The prohibition against torture is absolute. There are no exceptional circumstances whatsoever which can be used to justify torture.
And yet, torture is still being carried out by state officials around the world, driven by states’ ability to surveil dissidents, and intercept their communications.
In 2007, French technology firm Amesys (a subsidiary of Bull) supplied sophisticated communications surveillance systems to the Libyan intelligence services. The systems allegedly permitted the…
Content type: News & Analysis
On 24 October 2019, the Swedish government submitted a new draft proposal to give its law enforcement broad hacking powers. On 18 November 2019, the Legal Council (“Lagråd”), an advisory body assessing the constitutionality of laws, approved the draft proposal.
Privacy International believes that even where governments conduct hacking in connection with legitimate activities, such as gathering evidence in a criminal investigation, they may struggle to demonstrate that hacking as…
Content type: News & Analysis
*Photo by Michelle Ding on Unsplash
Pat Finucane was killed in Belfast in 1989. As he and his family ate Sunday dinner, loyalist paramilitaries broke in and shot Pat, a high profile solicitor, in front of his wife and children.
The Report of the Patrick Finucane Review in 2012 expressed “significant doubt as to whether Patrick Finucane would have been murdered by the UDA [Ulster Defence Association] had it not been for the different strands of involvement by the…
Content type: Long Read
*Photo by Kristina Flour on Unsplash
The British government needs to provide assurances that MI5’s secret policy does not authorise people to commit serious human rights violations or cover up of such crimes
Privacy International, along Reprieve, the Committee on the Administration of Justice, and the Pat Finucane Centre, is challenging the secret policy of MI5 to authorise or enable its so called “agents” (not MI5 officials) to commit crimes here in the UK.
So far we have discovered…
Content type: Advocacy
In this submission, Privacy International aims to provide the Office of the UN High Commissioner for Human Rights with information on how surveillance technologies are affecting the right to peaceful protests in new and often unregulated ways.
Based on Privacy International’s research, we provide observations, regarding the following:
the relationship between peaceful protests and the right to privacy;
the impact of new surveillance technologies in the context of peaceful protests…
Content type: News & Analysis
Photo: The European Union
“Border Externalisation”, the transfer of border controls to foreign countries, has in the last few years become the main instrument through which the European Union seeks to stop migratory flows to Europe. Similar to the strategy being implemented under Trump’s administration, it relies on utilising modern technology, training, and equipping authorities in third countries to export the border far beyond its shores.
It is enabled by the adoption…
Content type: Examples
A 17-year-old Palestinian resident of Lebanon, Ismail B. Ajjawi, was deported shortly after he arrived at Boston Airport, where he was due to start attending Harvard University the following week.
Immigration officers subjected him to hours of questioning — at one point leaving to search his phone and computer — according to a written statement by Ajjawi. According to the student, his visa was revoked because of content posted by some social media contacts.
The student alleges that…
Content type: Examples
In October 2018, the Singapore-based startup LenddoEFL was one of a group of microfinance startups aimed at the developing world that used non-traditional types of data such as behavioural traits and smartphone habits for credit scoring. Lenddo's algorithm uses numerous data points, including the number of words a person uses in email subject lines, the percentage of photos in a smartphone's library that were taken with a front-facing camera, and whether they regularly use financial apps on…
Content type: Examples
In 2017, US Immigration & Customs Enforcement (ICE) announced that it would seek to use artificial intelligence to automatically evaluate the probability of a prospective immigrant “becoming a positively contributing member of society.” In a letter to acting Department of Homeland Security Secretary Elaine Duke, a group of 54 concerned computer scientists, engineers, mathematicians, and researchers objected to ICE’s proposal and demanded that ICE abandon this approach because it would be…
Content type: News & Analysis
Today, the British Health Secretary Matt Hancock announced a partnership between the NHS and Amazon to use the NHS’s website content as the source for the answer given to medical question, such as “Alexa, how do I treat a migraine?”
While we welcome Amazon’s use of a trusted source of information for medical queries, we are however extremely concerned about the nature and the implications of this partnership. Amazon is a company with a worrying track record when it comes to the way they…
Content type: Advocacy
Refugees are among the most vulnerable people in the world. From the moment they flee their homes, as they pass through 'temporary' places such as refugee camps and detention centres to their 'final' destinations, they are continuously exposed to threats. In the digital age, these threats are increasingly being driven by the processing of vast amounts of highly sensitive personal data: from enrollment and registration processes needed for them to access services, to their identification and…
Content type: Examples
In February 2019 Google engineers announced that they had created faster, more efficient encryption system that could function on less-expensive Android phones that were too low-powered to implement existing full-device encryption. The scheme, known as Adiantum, uses established and well-vetted encryption tools and principles. Android has required smartphones to support encryption since 2015's version 6, but low-end devices were exempt because of the performance hit. It will now be up to device…
Content type: Long Read
Imagine that every time you want to attend a march, religious event, political meeting, protest, or public rally, you must share deeply personal information with police and intelligence agencies, even when they have no reason to suspect you of wrongdoing.
First, you need to go to the police to register; have your photo taken for a biometric database; share the contacts of your family, friends, and colleagues; disclose your finances, health records, lifestyle choices, relationship status, and…
Content type: News & Analysis
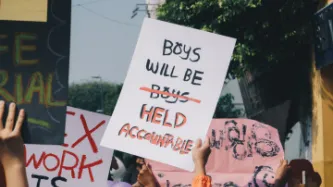
Protest movements throughout history have helped to shape the world we know today. From the suffragettes to the civil rights movement, and to contemporary movements such as those focusing on LGBTIQ+ rights, protests have become a vital way for many, who feel powerless otherwise, to have their voices heard.
But now, making the decision to attend a protest comes with consequences that you may very well be unaware of. This is because policing and security services, always hungry in their quest to…
Content type: News & Analysis
According to the International Organization for Migration, an estimated 258 million people are international migrants – that is, someone who changes their country of usual residence, That’s one in every 30 people on earth.
These unprecedented movements levels show no sign of slowing down. It is predicted that by 2050, there will be 450 million migrants across the world.
Nowadays, it is politically acceptable to demonise migrants, and countless leaders have spewed divisive and xenophobic…
Content type: Long Read
(In order to click the hyperlinks in the explainer below, please download the pdf version at the bottom of the page).