Search
Content type: Video
Watch Part 1 of our videos on How to use the Data Interception Environment (DIE). It goes through downloading the DIE from PI's GitHub, setting up a virtual phone, and changing network settings to allow data to be intercepted.
Watch Part 2 of our videos on How to use the DIE. It goes through fixing the certificates for the virtual phone, and how to start using the DIE to view and analyse data being sent from the phone.
PI has made this tool available to assist individuals, researchers and…
Content type: Explainer
Following sustained reporting by researchers, journalists and activists around the world, including recent disclosures exposed by the PegasusProject, the surveillance industry is facing scrutiny like never before.
In the latest move, eighteen U.S. lawmakers have today demanded that the U.S. government imposes sanctions on four non-US surveillance companies for, as they mention in their letter, facilitating “disappearance, torture and murder of human rights activists and journalists”.
The move…
Content type: News & Analysis
What if we told you that every photo of you, your family, and your friends posted on your social media or even your blog could be copied and saved indefinitely in a database with billions of images of other people, by a company you've never heard of? And what if we told you that this mass surveillance database was pitched to law enforcement and private companies across the world?
This is more or less the business model and aspiration of Clearview AI, a company that only received worldwide…
Content type: Press release
Today, following an in-depth investigation, the UK Competition and Market Authority (CMA) assessed that the competition concerns can only be addressed by Facebook selling Giphy in its entirety. This is a very significant decision. Facebook, the largest provider of social media sites and display advertising in the UK, acquired Giphy, the largest provider of GIFs. The merger would further increase Facebook’s dominance and Facebook would have benefitted from Giphy’s data collection practices and…
Content type: Video
<br />
Links
Daniel's petition: https://www.change.org/p/uk-parliament-ban-advertisers-from-targeting-eating-disorders
PI's diet ads report: https://privacyinternational.org/long-read/4603/unhealthy-diet-targeted-ads-investigation-how-diet-industry-exploits-our-data
More information on Instagram, targeted ads, and Frances Haugen - the Facebook whistleblower: https://privacyinternational.org/news-analysis/4622/reduce-facebooks-harms-teens-target-its-data-hungry-business-model…
Content type: Long Read
Zimbabwe has a history of state led surveillance that is carried out more for political gain than for the investigation of legitimate criminal activities. During former President Mugabe’s 37 year rule the government used laws and state security structures to carry out targeted surveillance of persons of political interest and more generalised mass surveillance of the population.
Specific laws such as the Interception of Communications Act as well as mandatory SIM-card registration regulations…
Content type: Video
<br />
You can find out more from Karisma here: https://web.karisma.org.co/
You can read the report here: https://web.karisma.org.co/useless-and-dangerous-a-critical-exploration-of-covid-applications-and-their-human-rights-impacts-in-colombia/
Content type: Explainer
With more and more connected devices around us, the chance that you've been hit by an update notification is high. But what do these software updates do? How do they actually work, and why are they important?
Hardware and Software
Modern electronic devices require two main parts to function: the hardware and the software. The hardware usually refers to physical electronic pieces inside a device (usually a collection of microchips, logic gates and specialised processing chips, such as those to…
Content type: Long Read
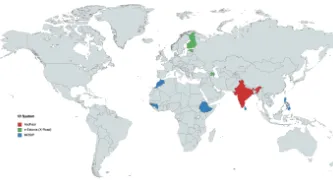
Governments around the world are increasingly making registration in national digital ID systems mandatory for populations, justifying its need on a range of issues from facilitating access to services, to national security and fighting against corruption. This is an attempt to create a "foundational identity" for an individual, or "a single source of truth" about who someone is, according to a government agency. These identity systems are run by governments, sometimes by private companies, or…
Content type: News & Analysis
Update: Based on the complaint, on 30 November 2021 the Ombudsman opened an inquiry into whether the European Commission failed to take into account human rights concerns or carry out human rights impact assessments before providing support to African countries to develop surveillance capabilities.
___
Privacy International (PI) together with a coalition of human rights groups have today called on the European Ombudsman, the EU’s oversight body, to investigate evidence that the block is…
Content type: Long Read
In early August, the African Union (AU) issued a statement condemning Denmark’s Aliens Act which, among other things, allows Demark to relocate asylum seekers to countries outside the European Union while their cases are being processed.
The AU argues that this amounts to an abdication by Denmark of “…its international responsibility to provide asylum and protection to those that enter its territory…’’ More importantly, the AU says this is an “extension of the borders of such countries and an…
Content type: News & Analysis
Introduction
The European Parliament has adopted a nonbinding resolution against the use of artificial intelligence (AI) by law enforcement in public spaces and a ban on facial recognition databases, such as the ones used by Clearview AI.
It is a significant and hugely welcome step in an ongoing campaign to ensure the EU leads the world in protecting against dangerous applications of AI within its borders.
The Resolution recognises the need to safeguard against application of AI and mass…
Content type: News & Analysis
Photo by Emmanuel Olguín on Unsplash
After many denials and much distraction, the truth is out. According to Facebook’s own internal research, Instagram is toxic to teen girls’ mental health.
This week, the Wall Street Journal reported on a collection of internal Facebook documents which it says demonstrate how the platform is acutely aware of the harmful effects Instagram has on the mental health of teens. The Journal reported that Facebook’s own research showed that use of the image…
Content type: Long Read
Introduction
Technology has driven a number of changes in the way that financial services are packaged and accessed by consumers. These changes have led to the rise of fintech, a data intensive industry that has been touted for its convenience and as an alternative to traditional financial services.
The current article looks at the use of digital loan Apps in Philippines and Kenya and contextualises the global discussions on fintech which we have been monitoring for some years. Research…
Content type: News & Analysis
After almost 20 years of presence of the Allied Forces in Afghanistan, the United States and the Taliban signed an agreement in February 2020 on the withdrawal of international forces from Afghanistan by May 2021. A few weeks before the final US troops were due to leave Afghanistan, the Taliban had already taken control of various main cities. They took over the capital, Kabul, on 15 August 2021, and on the same day the President of Afghanistan left the country.
As seen before with regime…
Content type: News & Analysis
Our relationship with ‘public space’ is being redefined, not just by a global pandemic, but also by a new era of biometric surveillance technologies. Biometric mass surveillance enables companies and authorities to track us based on unique personal data and identify us whenever, wherever we go.The increasing use of facial recognition and other biometric surveillance technologies – on our streets, in train stations, at protests, at sports matches and even in our global ‘town square’, Facebook –…
Content type: News & Analysis
Today Apple announced a set of measures aimed at improving child safety in the USA. While well-intentioned, their plans risk opening the door to mass surveillance around the world while arguably doing little to improve child safety.
Among the measures, Apple has announced that it is to introduce “on-device machine learning” which would analyse attachments for sexually explicit material, send a warning, and begin scanning every photo stored on its customers’ iCloud in order to detect child…
Content type: News & Analysis
As Amnesty International and Forbidden Stories continue to publish crucial information about the potential targets of NSO Group’s spyware, we know this much already: something needs to be done.
But what exactly needs to be done is less obvious. Even though this is not the first time that the world has learned about major abuses by the surveillance industry (indeed, it’s not even the first time this month), it’s difficult to know what needs to change.
So how can the proliferation and use of…
Content type: News & Analysis
A new industry is offering border agencies around the world access to advanced space-based surveillance capabilities once reserved for the most advanced intelligence agencies. Using satellites able to track signals from satellite phones and other emitters, these companies are then selling access to the data obtained to anyone willing to pay, including UK and EU border agencies.
While such surveillance can and is being used to save lives, it can also be used for illegal ‘pull backs’ in…
Content type: News & Analysis
What happened
On 22 July 2021, the Investigatory Powers Tribunal (IPT) issued a declaration on our challenge to the UK bulk communications regime finding that section 94 of the Telecommunications Act 1984 (since repealed by the Investigatory Powers Act 2016) was incompatible with EU law human rights standards. The result of the judgment is that a decade’s worth of secret data capture has been held to be unlawful. The unlawfulness would have remained a secret but for PI’s work.
You…
Content type: Press release
Amnesty International, Privacy International and The Centre for Research on Multinational Corporations (SOMO) have published a report uncovering NSO Group’s entire corporate structure, tracking the global money trail of both public and private investment into the lucrative spyware company.
Amnesty International and other rights groups have documented dozens of cases of NSO Group’s products being used by repressive governments across the world to put activists, journalists, and opposition…
Content type: Explainer
An array of digital technologies are being deployed in the context of border enforcement. Satellite and aerial surveillance are part of the surveillance toolkit and yet, they are also used by organisations seeking to hold government actions to account and improve efficacy of their own work. To effectively critique state use and delve into potential benefits of satellite and aerial surveillance, we must first understand it.
In this explainer we dig into a technology which many are aware of for…
Content type: News & Analysis
Last month, the World Health Organization published its guidance on Ethics and Governance of Artificial Intelligence for Health. Privacy International was one of the organisations that was tasked with reviewing the report. We want to start by acknowledging that this report is a very thorough one that does not shy away from acknowledging the risks and limitations of the use of AI in healthcare. As it is often the case with guidance notes of this kind, its effectiveness will depend on the…
Content type: Video
<br />
Links
You can find the Co-win vaccination website here: https://www.cowin.gov.in/
You can support PI at pvcy.org/donate and you can find out more about the Centre for Internet and Society at https://cis-india.org/
CIS also have a podcast, it’s called In flux and you can find it on all your favourite podcast apps and at https://in-flux.cis-india.org/
Like and subscribe to the podcast on which ever platform you use. It’s also available on our website at…
Content type: News & Analysis
This article was written by Abdías Zambrano, Public Policy Coordinator at IPANDETEC, and is adapted from a blog entry that originally appeared here.
Digital identity can be described as our digital personal data footprint, ranging from banking information and statistics to images, news we appear in and social network profiles, interactions with and in digital platforms, and information contained in private and public repositories. Our whole life is online, often leaving us with little choice…
Content type: News & Analysis
Legislation to "strengthen the integrity of UK elections and protect our democracy" through the Elections Integrity Bill was introduced to parliament this week.
This legislation will require people, for the first time in Great Britain, to show a state-issued photo ID, such as a driving license or passport, in order to exercise their right to vote, perhaps by the 2023 General Elections. The changes would affect elections in England, Scotland and Wales while voters in Northern Ireland are already…
Content type: News & Analysis
Around the world, we see migration authorities use technology to analyse the devices of asylum seekers. The UK via the Policing Bill includes immigration officers amongst those who can exercise powers to extract information from electronic devices. There are two overarching reasons why this is problematic:
The sole provision in the Policing Bill to extract information rests on voluntary provision and agreement, which fails to account for the power imbalance between individual and state. This…
Content type: News & Analysis
It is difficult to imagine a more intrusive invasion of privacy than the search of a personal or home computer ... when connected to the internet, computers serve as portals to an almost infinite amount of information that is shared between different users and is stored almost anywhere in the world.
R v Vu 2013 SCC 60, [2013] 3 SCR 657 at [40] and [41].
The controversial Police Crime Sentencing and Courts Bill includes provision for extracting data from electronic devices.
The Bill…
Content type: News & Analysis
Imagine going to a peaceful protest and having to show your ID to the police before you can join it. Or having to fill out a form about why you are attending that particular protest.Sounds absurd, right? Surely we should all be free to protest, without the police knowing who we are?But high tech surveillance of protests is real, and it enables the police to identify, monitor and track protestors, indiscriminately and at scale.For example, your face is increasingly becoming your ID card with the…