Search
Content type: Long Read
In their gold rush to build cloud and AI tools, Big Tech is also enabling unprecedented government surveillance. Thanks to reporting from The Guardian, +972 Magazine, Local Call, and The Intercept, we have insights into the murky deals between the Israeli Government and Big Tech firms. Designed to insulate governments from scrutiny and accountability, these deals bode a dark future for humanity, one that is built using the same tools that once promised a bright, positive world.On 25 September…
Content type: Advocacy
BackgroundThe Snowden revelations and subsequent litigation have repeatedly identified unlawful state surveillance by UK agencies. In response, the UK Parliament passed the highly controversial Investigatory Powers Act 2016 (IPA), which authorised massive, suspicionless surveillance on a scale never seen before, with insufficient safeguards or independent oversight.Privacy International led legal challenges to this mass surveillance regime both before and after the Act became law. The Act…
Content type: Long Read
IntroductionData about our health reveals some of the most sensitive, intimate - and potentially embarrassing - information about who we are. Confidentiality is, and has always been, at the very heart of medical ethics. People need to be able to trust their doctors, nurses and other healthcare providers so that they are not afraid to tell them something important about their health for fear of shame, judgement or social exclusion.It’s no surprise then that data protection regimes around…
Content type: Long Read
We won our case against the UK’s Security Service (MI5) and the Secretary of State for the Home Department (SSHD). The Investigatory Powers Tribunal (IPT) – the judicial body responsible for monitoring UK’s intelligence and security agencies – held that MI5 acted unlawfully by knowingly holding people’s personal data in systems that were in breach of core legal requirements. MI5 unlawfully retained huge amounts of personal data between 2014 and 2019. During that period, and as a result of these…
Content type: Press release
In a landmark judgment, handed down today (Monday 30 January 2023), the Investigatory Powers Tribunal have found that there were “very serious failings” at the highest levels of MI5 to comply with privacy safeguards from as early as 2014, and that successive Home Secretaries did not to enquire into or resolve these long-standing rule-breaking despite obvious red flags.Human rights organisations Liberty and Privacy International, who brought this significant legal case in January 2020, have…
Content type: Report
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content type: News & Analysis
After almost 20 years of presence of the Allied Forces in Afghanistan, the United States and the Taliban signed an agreement in February 2020 on the withdrawal of international forces from Afghanistan by May 2021. A few weeks before the final US troops were due to leave Afghanistan, the Taliban had already taken control of various main cities. They took over the capital, Kabul, on 15 August 2021, and on the same day the President of Afghanistan left the country.As seen before with regime…
Content type: Long Read
Additionally, in January 2020 Privacy International and UK-based NGO Liberty filed a new claim against MI5 and the Secretary of State for the Home Department in the Investigatory Powers Tribunal (the “Ungoverned Spaces Case”, this time, the case sought to hold MI5 and the SSHD accountable for systemic, long-term failures in the way they handle and retain millions of people’s personal data. As part of this claim, PI requested that the IPT re-opens parts of the original BPD/BCD. This aspect of…
Content type: Long Read
The Grand Chamber of the European Court of Human Rights ruled that the UK government’s historical mass interception program violates the rights to privacy and freedom of expression. The Court held that the program “did not contain sufficient “end-to-end” safeguards to provide adequate and effective guarantees against arbitrariness and the risk of abuse.” As a result the Court ruled that UK law "did not meet the “quality of law” requirement and was therefore incapable of keeping the “…
Content type: News & Analysis
Today, the Constitutional Court of South Africa in a historic judgment declared that bulk interception by the South African National Communications Centre is unlawful and invalid.
The judgment is a confirmation of the High Court of South Africa in Pretoria’s powerful rejection of years of secret and unchecked surveillance by South African authorities against millions of people - irrespective of whether they reside in South Africa.
The case was brought by two applicants, the amaBhungane Centre…
Content type: Long Read
Over the last two decades we have seen an array of digital technologies being deployed in the context of border controls and immigration enforcement, with surveillance practices and data-driven immigration policies routinely leading to discriminatory treatment of people and undermining peoples’ dignity.And yet this is happening with little public scrutiny, often in a regulatory or legal void and without understanding and consideration to the impact on migrant communities at the border and…
Content type: Examples
An engineering and computer science professor and his team from The Ohio State University discovered a design flaw in low-powered Bluetooth devices that leaves them susceptible to hacking.
Zhiqiang Lin, associate professor of computer science and engineering at the university, found the commonly used Bluetooth Low Energy devices, such as fitness trackers and smart speakers, are vulnerable when they communicate with their associated apps on the owner’s mobile phone.
"There is a fundamental…
Content type: News & Analysis
In mid-2019, MI5 admitted, during a case brought by Liberty, that personal data was being held in “ungoverned spaces”. Much about these ‘ungoverned spaces’, and how they would effectively be “governed” in the future, remained unclear. At the moment, they are understood to be a ‘technical environment’ where personal data of unknown numbers of individuals was being ‘handled’. The use of ‘technical environment’ suggests something more than simply a compilation of a few datasets or databases.
The…
Content type: Examples
After an 18-month investigation involving interviews with 160 life insurance companies, in January 2019 New York Financial Services, the state's top financial regulator, announced it would allow life insurers to use data from social media and other non-traditional sources to set premium rates for its customers. Insurers will be required to demonstrate that their use of the information doesn't unfairly discriminate against specific customers. New York is the first state to issue specific…
Content type: News & Analysis
According to the International Organization for Migration, an estimated 258 million people are international migrants – that is, someone who changes their country of usual residence, That’s one in every 30 people on earth.
These unprecedented movements levels show no sign of slowing down. It is predicted that by 2050, there will be 450 million migrants across the world.
Nowadays, it is politically acceptable to demonise migrants, and countless leaders have spewed divisive and xenophobic…
Content type: Long Read
It’s 15:10 pm on April 18, 2018. I’m in the Privacy International office, reading a news story on the use of facial recognition in Thailand. On April 20, at 21:10, I clicked on a CNN Money Exclusive on my phone. At 11:45 on May 11, 2018, I read a story on USA Today about Facebook knowing when teen users are feeling insecure.
How do I know all of this? Because I asked an advertising company called Quantcast for all of the data they have about me.
Most people will have never heard of…
Content type: Impact Case Study
PI and our global partners have been at the forefront of challenging communications data retention for over a decade.
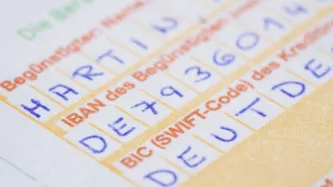
What is the problem
Communications data, also known as metadata, tells a story about your digital activity and answers the who, when, what, and how of a specific communication. While communications data doesn't include the contents of a message, all of the other information about the message can be very revealing about people, their habits, thoughts, health and personal…
Content type: Impact Case Study
What is the problem
For over two decades we have been documenting an alarming use and spread of surveillance. It is no longer just the wars on terror or drugs or migration that is driving this trend. The management of health crises and distribution of welfare regularly are among others being used to justify this turn to increasingly invasive forms of surveillance. From country to country we see the same ideas and the same profiteers expanding their reach.
When we first released our report on…
Content type: Press release
In today’s latest hearing in our ongoing legal challenge against the collection of massive troves of our personal data by the UK intelligence agencies, shocking new evidence has emerged about GCHQ’s attempts to yet again avoid proper independent scrutiny for its deeply intrusive surveillance activities.
In a truly breath-taking exchange of letters between the Investigatory Powers Commissioner’s Office (“IPCO”) and the Director of Legal Affairs at GCHQ, it has emerged that GCHQ have…
Content type: Report
This report sheds light on the current state of affairs in data retention regulation across the EU post the Tele-2/Watson judgment. Privacy International has consulted with digital rights NGOs and industry from across the European Union to survey 21 national jurisdictions (Austria, Belgium, Bulgaria, Croatia, Cyprus, Czech Republic, France, Germany, Hungary, Ireland, Italy, Luxembourg, the Netherlands, Poland, Portugal, Romania, Slovakia, Slovenia, Spain, Sweden, and the United Kingdom).…
Content type: News & Analysis
On a hot day in Nairobi, our researcher is speaking to an officer of Kenya’s National Intelligence Service (NIS). The afternoon is wearing on and the conversation has turned to the presidential elections, taking place in August this year. He has just finished describing the NIS’ highly secret surveillance powers and the disturbing ways in which these powers are deployed.
“It is what you might call ‘acceptable deaths,’” he states about the misuse of communications surveillance powers. “People…
Content type: News & Analysis
This guest piece was written by Jane Duncan of the Right2Know Campaign. It does not necessarily reflect the views or position of Privacy International.
On 23rd March the United Nations Human Rights Committee released its assessment on South Africa’s compliance with the International Covenant on Civil and Political Rights (ICCPR). The report includes a blistering attack on the Government for failing to respect the privacy of the communications of users and makes…
Content type: Press release
The ruling today from the European Court of Justice, invalidating the European Union’s 2006 Data Retention Directive policy, was strong and unequivocal: the right to privacy provides a fundamental barrier between the individual and powerful institutions, and laws allowing for indiscriminate, blanket retention on this scale are completely unacceptable.
As the Court states, it is not, and never was, proportionate to spy on the entire population of Europe. The types of data retained under this…
Content type: Press release
Google's latest Transparency Report, released at 3pm GMT this afternoon, shows that requests by European governments for the browsing history, email communications, documents and IP addresses of Google's users have skyrocketed since the Transparency Report was launched three years ago. Countries in the European Union made 7,254 requests about 9,240 users or accounts between July and December 2012, averaging over 1,200 requests a month. This represents over a third of all requests made by…
Content type: News & Analysis
Privacy International and EPIC praised a vote today in the European Parliament today that rejected the transfer of finacial records to the United States under an interim agreement. A resolution to reject the deal passed 378-16, with 31 abstentions. Members of the parliament stated the proposed agreement lacked adequate privacy safeguards, and was a disproportionat response to US concerns about terrorism that also lacked reciprocity.
Simon Davies, Director General of Privacy International…
Content type: News & Analysis
At its last session on November 21st and 22nd 2006, the Article 29 Working Party has again been dealing with the SWIFT case and has unanimously adopted Opinion 128 on its findings in this case.
In this Opinion, the Article 29 Working Party emphasizes that even in the fight against terrorism and crime fundamental rights must remain guaranteed. The Article 29 Working Party insists therefore on the respect of global data protection principles.
SWIFT is a worldwide financial messaging service…
Content type: News & Analysis
Dear Mr Schrank,
I am writing with regard to the current controversy over the private arrangement between SWIFT and the U.S. Government that facilitates the extradition of confidential financial transaction data from SWIFT to U.S. authorities. You will be aware that Privacy International contends that this arrangement breaches privacy and data protection law, and we have lodged complaints with regulatory authorities in 38 countries.
In my many discussions with SWIFT officials over the past…