Advanced Search
Content Type: Long Read
On 12 April 2020, citing confidential documents, the Guardian reported Palantir would be involved in a Covid-19 data project which "includes large volumes of data pertaining to individuals, including protected health information, Covid-19 test results, the contents of people’s calls to the NHS health advice line 111 and clinical information about those in intensive care".
It cited a Whitehall source "alarmed at the “unprecedented” amounts of confidential health information being swept up in the…
Content Type: Case Study
IMSI catchers – International Mobile Subscriber Identity catchers – are a particularly intrusive technology being used by police to monitor protesters and intercept their personal information and communications.
IMSI catchers have been used - officially or in secret - across the globe to monitor protests, including in the US and Germany; in the UK, police forces have refused to disclose any information on their use but documents obtained by the Bristol cable show that nine police forces have…
Content Type: News & Analysis
This week International Health Day was marked amidst a global pandemic which has impacted every region in the world. And it gives us a chance to reflect on how tech companies, governments, and international agencies are responding to Covid-19 through the use of data and tech.
All of them have been announcing measures to help contain or respond to the spread of the virus; but too many allow for unprecedented levels of data exploitation with unclear benefits, and raising so many red flags…
Content Type: Case Study
In Peru, you get asked for your fingerprint and your ID constantly - when you’re getting a new phone line installed or depositing money in your bank account – and every Peruvian person has an ID card, and is included in the National Registry of Identity – a huge database designed to prove that everyone is who they say they are. After all, you can change your name, but not your fingerprint.
However, in 2019 the National Police of Peru uncovered a criminal operation that was doing just that:…
Content Type: Advocacy
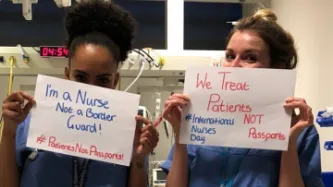
The letter has been signed by more than 40 organisations and it is open for individuals to sign.
At the moment, the Department of Health and Social Care has given no assurance that NHS data will not be shared with the Home Office and used for immigration enforcement, including for those people with a confirmed coronavirus diagnosis.
Assurances which were confirmed by the Irish government as part of their response to COVID-19: last week, during a Parliamentary debate, Irish Minister of Health…
Content Type: Long Read
The UK’s Metropolitan Police have began formally deploying Live Facial Recognition technology across London, claiming that it will only be used to identify serious criminals on “bespoke ‘watch lists’” and on “small, targeted” areas.
Yet, at the same time, the UK’s largest police force is also listed as a collaborator in a UK government-funded research programme explicitly intended to "develop unconstrained face recognition technology", aimed “at making face…
Content Type: Case Study
In 2015, James Bates was charged with first-degree murder in the death of Victor Collins. Collins was found floating face down in Bates’ hot tub in November 2015. Bentonville police served two search warrants ordering Amazon to turn over the “electronic data in the form of audio recordings, transcribed records, text records and other data contained on the Amazon Echo device” in Bates’ home.
The reason for the warrants? According to the police, just because the device was in the house that…
Content Type: Long Read
Background
Kenya’s National Integrated Identity Management Scheme (NIIMS) is a biometric database of the Kenyan population, that will eventually be used to give every person in the country a unique “Huduma Namba” for accessing services. This system has the aim of being the “single point of truth”, a biometric population register of every citizen and resident in the country, that then links to multiple databases across government and, potentially, the private sector.
NIIMS was introduced…
Content Type: Case Study
In 2015, a man in Connecticut was charged with murdering his wife based on evidence from her Fitbit. Richard Dabate, the accused, told the police that a masked assailant came into the couple’s suburban home at around 9am on 23 December 2015, overpowering Dabate then shooting his wife as she returned through the garage.
However, the victim’s fitness tracker told a different story. According to data from the device, which uses a digital pedometer to track the wearer’s steps, Dabate’s wife was…
Content Type: Case Study
Anyone who is arrested should be informed of the reasons for their arrest and any charges against them. Anyone who is detained is also entitled to a trial within a reasonable time, or to be released if no charges are held against them.
Privacy enhances these protections. It provides limitations on the manner in which information can be obtained about you, and the kind of information that can be accessed about you by law enforcement, who can access that information and how they can use it.…
Content Type: News & Analysis
In mid-2019, MI5 admitted, during a case brought by Liberty, that personal data was being held in “ungoverned spaces”. Much about these ‘ungoverned spaces’, and how they would effectively be “governed” in the future, remained unclear. At the moment, they are understood to be a ‘technical environment’ where personal data of unknown numbers of individuals was being ‘handled’. The use of ‘technical environment’ suggests something more than simply a compilation of a few datasets or databases.
The…
Content Type: News & Analysis
On 30 January 2020, Kenya’s High Court handed down its judgment on the validity of the implementation of the National Integrated Identity Management System (NIIMS), known as the Huduma Namba. Privacy International submitted an expert witness testimony in the case. We await the final text of the judgment, but the summaries presented by the judges in Court outline the key findings of the Court. Whilst there is much there that is disappointing, the Court found that the implementation of NIIMS…
Content Type: Case Study
Discriminatory laws on the basis of sexual orientation across the globe exist in stark opposition to the principle that the law should be the same for each and every one of us. We are all entitled to the same protections against any discrimination. Equality before the law dictates that there must be a reasonable justification to regulate any aspect of a person’s life.
Laws discriminating on the basis of sexual orientation interfere with our private lives and development. There can be no…
Content Type: Case Study
Every one of us has an expectation to be legally protected in the same way, to have access to the same human rights, and to be able to defend those rights in court.
However, for trans and non-binary people, this has not always been the case – and in many places around the world it still isn’t the case. The lack of legal recognition for their gender has had significant consequences.
If the law does not recognise you as the person that you are and treats you as someone you are not then you…
Content Type: News & Analysis
Today Advocate General (AG) Campos Sánchez-Bordona of the Court of Justice of the European Union (CJEU), issued his opinions (C-623/17, C-511/18 and C-512/18 and C-520/18) on how he believes the Court should rule on vital questions relating to the conditions under which security and intelligence agencies in the UK, France and Belgium could have access to communications data retained by telecommunications providers.
The AG addressed two major questions:
(1) When states seek to impose…
Content Type: Long Read
Mobile phones remain the most frequently used and most important digital source for law enforcement investigations. Yet it is not just what is physically stored on the phone that law enforcement are after, but what can be accessed from it, primarily data stored in the Cloud.
Cellebrite, a prominent vendor of surveillance technology used to extract data from mobile phones, notes in its Annual Trend Survey that in approximately half of all investigations, cloud data ‘appears’ and that…
Content Type: Case Study
On 3 December 2015, four masked men in plainclothes arrested Isnina Musa Sheikh in broad daylight (at around 1 p.m.) as she served customers at her food kiosk in Mandera town, in the North East of Kenya, Human Rights Watch reported. The men didn’t identify themselves but they were carrying pistols and M16 assault rifles, commonly used by Kenyan defence forces and the cars that took her away had their insignia on the doors. Isnina’s body was discovered three days later in a shallow grave about…
Content Type: Case Study
The prohibition against torture is absolute. There are no exceptional circumstances whatsoever which can be used to justify torture.
And yet, torture is still being carried out by state officials around the world, driven by states’ ability to surveil dissidents, and intercept their communications.
In 2007, French technology firm Amesys (a subsidiary of Bull) supplied sophisticated communications surveillance systems to the Libyan intelligence services. The systems allegedly permitted the…
Content Type: Case Study
In the Xingjiang region of Western China, surveillance is being used to facilitate the government’s persecution of 8.6million Uighur Muslims.
Nurjamal Atawula, a Uighur woman, described how, in early 2016, police began regularly searching her home and calling her husband into the police station, as a result of his WeChat activity.
WeChat is a Chinese multi-purpose messaging, social media and mobile payment app. As of 2013, it was being used by around 1million Uighurs, but in 2014 WeChat was…
Content Type: News & Analysis
We found this image here.
Today, a panel of competition experts, headed by Professor Jason Furman, the former chief economic adviser of in the Obama administration, confirmed that tech giants, like Facebook, Amazon, Google, Apple and Microsoft, do not face enough competition.
Significantly, the report finds that control over personal data by tech giants is one of the main causes preventing competition and ultimately innovation.
Privacy International's research has shown clear examples of…