Advanced Search
Content Type: Long Read
Period tracking apps and the rollback of reproductive rightsThe aftermath of the overturning of Roe v. Wade in the United States (US) sparked widespread debate and concern that data from period tracking apps could be use to criminalise those seeking abortion care.While the surveillance and criminalisation of reproductive choices are neither new nor unique to the US, the scale and intensity of today’s crisis continue to grow. To put it into perspective, 22 million women and girls of reproductive…
Content Type: Long Read
If you’ve ever used TikTok, Instagram, or X/Twitter, you will already be familiar with centralised social media.Centralised social media means big company owns the app, controls the software, and keeps all your data.For example, ByteDance makes TikTok. They own it, run the servers, decide what you see in your feed, and hold onto every video you like or comment on. They call the shots when it comes to your data.But what if social media didn’t work that way? What if no single company was in…
Content Type: Advocacy
Our submission made the following recommendations to the Committee regarding the Kenya:Review and amend the proposed digital identity system, the Maisha Numba, to ensure it aligns with Kenya’s national and international human rights obligations in its design and implementation, and adopts legal, policy and technical safeguards to prevent exclusion and marginalisation.Ensure that measures taken to develop digital public infrastructures abide by Kenya’s national and international human rights…
Content Type: Report
First published in 2017, PI’s Guide to International Law and Surveillance is an attempt to collate relevant excerpts from these judgments and reports into a single principled guide that will be regularly updated. This is the fourth edition of the Guide. It has been updated it to reflect the most relevant legal developments until March 2024.The Guide aspires to be a handy reference tool for anyone engaging in campaigning, advocacy, and scholarly research, on these issues. The fourth…
Content Type: Advocacy
BackgroundThe Snowden revelations and subsequent litigation have repeatedly identified unlawful state surveillance by UK agencies. In response, the UK Parliament passed the highly controversial Investigatory Powers Act 2016 (IPA), which authorised massive, suspicionless surveillance on a scale never seen before, with insufficient safeguards or independent oversight.Privacy International led legal challenges to this mass surveillance regime both before and after the Act became law. The Act…
Content Type: Examples
Just as China uses technology system called "Integrated Joint Operations Platform" to control and surveil the persecuted population of Uighurs while restricting their movement and branding dissent as "terrorism", the Israeli military is using facial recognition and a massive database of personal information to control millions of Palestinians in the occupied West Bank. In November 2021, NSO Group's Pegasus spyware was found on the phones of six Palestinian human rights activists, three of whom…
Content Type: Examples
The Israeli minister of public security has joined police in denying claims in an article in Calcalist that the country's police force have used NSO Group's Pegasus software to spy on the phones of people who led protests against former premier Benjamin Netanyahu. Calcalist reported that the surveillance was carried out without court supervision or oversight of how the data was used. The daily Haaretz newspaper also reported that it had seen a 2013 invoice in which NSO billed police @@2.7…
Content Type: Video
In Kenya, if you don’t have an ID, life can be extremely difficult. But for thousands of people across the country, getting an ID can be nigh on impossible. Some Kenyan citizens can’t obtain a national ID because they are registered in the Kenyan refugee database. Often referred to as victims of double registration, their predicaments reveal a deeper problem with ID itself.Now Haki na Sheria - a Kenyan organisation advocating for and supporting the victims of double registration - and three…
Content Type: Long Read
Governments around the world are increasingly making registration in national digital ID systems mandatory for populations, justifying its need on a range of issues from facilitating access to services, to national security and fighting against corruption. This is an attempt to create a "foundational identity" for an individual, or "a single source of truth" about who someone is, according to a government agency. These identity systems are run by governments, sometimes by private companies, or…
Content Type: Advocacy
Some of the most vulnerable groups in Mexico are amongst the groups at risk from a draft General Population Law that creates a biometric “Unique Digital Identity Card” (CUID), argue civil society organisations. The proposed law has now reached the senate, and has raised serious concerns from civil society organisations. Led by our global partner in Mexico Red en Defensa de los Derechos Digitales (R3D), PI along with 25 organisations have signed a joint letter to the members of the senate,…
Content Type: News & Analysis
After almost 20 years of presence of the Allied Forces in Afghanistan, the United States and the Taliban signed an agreement in February 2020 on the withdrawal of international forces from Afghanistan by May 2021. A few weeks before the final US troops were due to leave Afghanistan, the Taliban had already taken control of various main cities. They took over the capital, Kabul, on 15 August 2021, and on the same day the President of Afghanistan left the country.As seen before with regime…
Content Type: Advocacy
On 6 August 2021, the World Health Organisation (WHO) published its technical specifications and implementation guidance for “Digital Documentation of COVID-19 Certificates: Vaccination Status” (DDCC:VS) following months of consultations. As governments around the world are deploying their own Covid-19 certificates, guidance from the global health agency was expected to set a global approach, and one that prioritises public health. As such, we would expect the WHO to identify what these…
Content Type: Press release
Amnesty International, Privacy International and The Centre for Research on Multinational Corporations (SOMO) have published a report uncovering NSO Group’s entire corporate structure, tracking the global money trail of both public and private investment into the lucrative spyware company.
Amnesty International and other rights groups have documented dozens of cases of NSO Group’s products being used by repressive governments across the world to put activists, journalists, and opposition…
Content Type: News & Analysis
This article was written by Abdías Zambrano, Public Policy Coordinator at IPANDETEC, and is adapted from a blog entry that originally appeared here.
Digital identity can be described as our digital personal data footprint, ranging from banking information and statistics to images, news we appear in and social network profiles, interactions with and in digital platforms, and information contained in private and public repositories. Our whole life is online, often leaving us with little choice…
Content Type: News & Analysis
Legislation to "strengthen the integrity of UK elections and protect our democracy" through the Elections Integrity Bill was introduced to parliament this week.
This legislation will require people, for the first time in Great Britain, to show a state-issued photo ID, such as a driving license or passport, in order to exercise their right to vote, perhaps by the 2023 General Elections. The changes would affect elections in England, Scotland and Wales while voters in Northern Ireland are already…
Content Type: Report
In this briefing, Amnesty International, PI and The Centre for Research on Multinational Corporations (SOMO) discuss the corporate structure of NSO group, one of the surveillance industry's well-known participants. The lack of transparency around NSO Group’s corporate structure and the lack of information about the relevant jurisdictions within which it operates are significant barriers in seeking prevention of, and accountability for, human rights violations reportedly linked to NSO Group’s…
Content Type: Explainer
What is hacking?
Hacking refers to finding vulnerabilities in electronic systems, either to report and repair them, or to exploit them.
Hacking can help to identify and fix security flaws in devices, networks and services that millions of people may use. But it can also be used to access our devices, collect information about us, and manipulate us and our devices in other ways.
Hacking comprises a range of ever-evolving techniques. It can be done remotely, but it can also include physical…
Content Type: Long Read
On 8 January 2021, the UK High Court issued a judgment in the case of Privacy International v. Investigatory Powers Tribunal. The Secretary of State for Foreign and Commonwealth Affairs and Government Communication Headquarters (GCHQ) appeared as interested parties to the case.
After our initial reaction, below we answer some of the main questions relating to the case.
NOTE: This post reflects our initial reaction to the judgment and may be updated.
What’s the ruling all about?
In…
Content Type: Frequently Asked Questions
On 8 January 2021, the UK High Court issued a judgment in the case of Privacy International v. Investigatory Powers Tribunal. The Secretary of State for Foreign and Commonwealth Affairs and Government Communication Headquarters (GCHQ) appeared as interested parties to the case.
After our initial reaction, below we answer some of the main questions relating to the case.
NOTE: This post reflects our initial reaction to the judgment and may be updated.
Content Type: Report
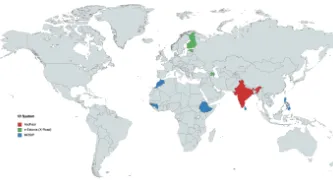
Many countries in the world have existing ID cards - of varying types and prevalence - there has been a new wave in recent years of state “digital identity” initiatives.
The systems that states put in place to identify citizens and non-citizens bring with them a great deal of risks.
This is particularly the case when they involve biometrics - the physical characteristics of a person, like fingerprints, iris scans, and facial photographs.
Activists and civil society organisations around the…
Content Type: Report
A common theme of all major pieces of national jurisprudence analyzing the rights implications of national identity system is an analysis of the systems’ impacts on the right to privacy.
The use of any data by the State including the implementation of an ID system must be done against this backdrop with respect for all fundamental human rights. The collection of data to be used in the system and the storage of data can each independently implicate privacy rights and involve overlapping and…
Content Type: Report
Identity systems frequently rely on the collection and storage of biometric data during system registration, to be compared with biometric data collected at the point of a given transaction requiring identity system verification.
While courts have arguably overstated the effectiveness and necessity of biometric data for identity verification in the past, the frequency of biometric authentication failure is frequently overlooked. These failures have the potential to have profoundly…
Content Type: Report
National identity systems naturally implicate data protection issues, given the high volume of data necessary for the systems’ functioning.
This wide range and high volume of data implicates raises the following issues:
consent as individuals should be aware and approve of their data’s collection, storage, and use if the system is to function lawfully. Despite this, identity systems often lack necessary safeguards requiring consent and the mandatory nature of systems ignores consent…
Content Type: Report
While identity systems pose grave dangers to the right to privacy, based on the particularities of the design and implementation of the ID system, they can also impact upon other fundamental rights and freedoms upheld by other international human rights instruments including the International Covenant on Civil and Political Right and the International Covenant on Economic, Social and Cultural Rights such as the right to be free from unlawful discrimination, the right to liberty, the right to…
Content Type: Report
Rather than providing a list of arguments, as is the case in the other sections of this guide, the fifth section provides a general overview describing the absence of consideration of these themes in existing jurisprudence and the reasons why these themes warrant future consideration including identity systems’ implications for the rule of law, the role of international human rights law, and considerations of gender identity.
Democracy, the Rule of Law and Access to Justice: This analysis of…
Content Type: Case Study
Privacy matters. It matters when you’re walking the streets of your home town and when you’re fleeing your home in search of safety. It matters if you’re at a protest or if you’re in bed.
Our wellbeing in each of these instances depends on the protection of our privacy. No situation can be fully understood in isolation.
Unjustifiable intrusions on our privacy become a weapon to eradicate communities and prey upon refugees and asylum seekers, push people away from protests in fear of…
Content Type: Case Study
Numerous sexist, mysoginistic, homophobic and racist practices are flourishing online, in ways that are harder for national authorities to stop than when abuse takes place offline. One of these practices is ‘revenge pornography’, which involves online distribution of private sexual images without the consent of the person depicted.
One victim of image based sexual abuse (more commonly known as revenge porn): Chrissy Chambers. Chrissy was 18 years old when her boyfriend convinced her to spend…
Content Type: News & Analysis
New technologies continue to present great risks and opportunities for any users but for some communities the implications and harms can have severe consequences and one of the sectors facing increasing challenges to keep innovating whilst protecting themselves and the people they serve is the humanitarian sector.
Over the course of engagement with the humanitarian sector, one of our key observations has been how risk assessments undertaken in the sector omitted to integrate a hollistic…
Content Type: Video
You can listen and subscribe to the podcast where ever you normally find your podcasts:
Spotify
Apple podcasts
Google podcasts
Castbox
Overcast
Pocket Casts
Peertube
Youtube
Stitcher
And more...
Content Type: Long Read
Immunity Passports have become a much hyped tool to cope with this pandemic and the economic crisis. Essentially, with immunity passports those who are 'immune' to the virus would have some kind of certified document - whether physical or digital. This 'passport' would give them rights and privileges that other members of the community do not have.
This is yet another example of a crisis-response that depends on technology, as we saw with contact-tracing apps. And it is also yet another…