Advanced Search
Content Type: Legal Case Files
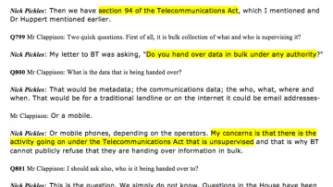
Privacy International in August 2014 filed a legal challenge in the Investigatory Powers Tribunal. Detailed grounds were filed on 10 September 2015 and re-amended on 8 January 2016 following disclosures regarding the use of section 94 of the Telecommunications Act 1984 to include a challenge to the use of section 94 of the Telecommunications Act.
The Respondents provided an amended response on 19 February 2016 which provides detail on the use of section 94 and…
Content Type: Press release
Today Sir Stanley Burnton, the Interception of Communications Commissioner, published a highly critical review of the use of Section 94 of the Telecommunications Act 1984 for gathering vast amounts of our communications data in bulk. This obscure clause pre-dates the internet era, but has been used for nearly two decades for mass surveillance. Today is the first time that these powers have been criticised by an independent statutory body. IOCCO is critical of the Government's use of these…
Content Type: Long Read
This piece originally appeared here.
On both sides of the Atlantic, we are witnessing the dramatic expansion of government hacking powers. In the United States, a proposed amendment to Rule 41 of the Federal Rules of Criminal Procedure would permit the government to obtain a warrant, in certain circumstances, to hack unspecified numbers of electronic devices anywhere in the world. Meanwhile, across the pond, the British Parliament is currently debating the Investigatory…
Content Type: Long Read
1984: A broad law, a broad power and a whole lot of secrecy
In the wake of litigation brought by Privacy International (‘PI’) and as the Government prepared to introduce the Draft Investigatory Powers Bill (‘IP Bill’) in November 2015, there was a cascade of ‘avowals’- admissions that the intelligence agencies carry out some highly intrusive surveillance operations under powers contained in outdated and confusing legislation.
It is disappointing that it has been almost six months since…
Content Type: News & Analysis
The Investigatory Powers Bill introduced on Tuesday 1 March contains the same range of ‘bulk powers’ envisaged in the earlier draft: bulk interception warrants; bulk acquisition warrants; bulk equipment interference warrants; and bulk personal dataset warrants.
These powers, if adopted as currently envisaged in the Bill, would codify a practice of mass, untargeted surveillance by the UK intelligence services.
In the last couple of years, some of the mass surveillance powers used by…
Content Type: Press release
In response to the Investigatory Powers Tribunal (IPT) ruling today that GCHQ's hacking is lawful, we have issued the following press statement:
"We are disappointed by the IPT’s judgment today, which has found Government hacking lawful based on a broad interpretation of a law dating back to 1994, when the internet and mobile phone technology were in their infancy.
Until we brought this case, GCHQ would neither confirm nor deny that it was they were engaging in mass hacking of…
Content Type: Long Read
The Investigatory Powers Tribunal (“IPT”) today held that GCHQ hacking of computers, mobile devices and networks is lawful, wherever it occurs around the world. We are disappointed that the IPT has not upheld our complaint and we will be challenging its findings.
Our complaint is the first UK legal challenge to state-sponsored hacking, an exceptionally intrusive form of surveillance. We contended that GCHQ hacking operations were incompatible with democratic principles and human rights…
Content Type: Press release
Documents released today confirm GCHQ, the UK intelligence agency, is hacking computers in the United Kingdom without individual warrants. The documents contain previously unknown details and defenses of GCHQ's use of "thematic warrants" to hack. The legal challenge in which these documents are being disclosed was brought by Privacy International and seven internet and communications service providers from around the world in response to disclosures made by Edward Snowden.…
Content Type: Press release
The Government has quietly ushered through legislation amending the anti-hacking laws to exempt GCHQ from prosecution. Privacy International and other parties were notified of this just hours prior to a hearing of their claim against GCHQ's illegal hacking operations in the Investigatory Powers Tribunal.
In its legal filings, sent to Privacy International only the day before the hearing began, the Government notified claimants that the Computer Misuse Act was rewritten on 3 March 2015 to…
Content Type: Press release
The British Government has admitted its intelligence services have the broad power to hack into personal phones, computers, and communications networks, and claims they are legally justified to hack anyone, anywhere in the world, even if the target is not a threat to national security nor suspected of any crime.
These startling admissions come from a government court document published today by Privacy International. The document was filed by the government in response to two …
Content Type: Press release
Privacy International today filed a legal complaint demanding an end to the unlawful hacking being carried out by GCHQ which, in partnership with the NSA, is infecting potentially millions of computer and mobile devices around the world with malicious software that gives them the ability to sweep up reams of content, switch on users' microphones or cameras, listen to their phone calls and track their locations.
The complaint, filed in the UK’s Investigatory Powers Tribunal, is the…
Content Type: Long Read
Today, Privacy International lodged a legal challenge to GCHQ's extensive and intrusive hacking of personal computers and devices. Below, we answer a few questions about the law underlying our complaint, and why it matters.
Is hacking legal?
As a result of the Snowden revelations, we have learned that GCHQ, often in partnership with the NSA, has been using malicious software to intrude upon our computers and mobile devices.
This type of activity, often called "hacking," is a…
Content Type: Long Read
Spy agencies have long sought to turn the technologies that improve all our lives against us. From some of the very first forms of remote communications such as telegraph cables, to modern-day means like Skype: if the spies can exploit it, they will.
And, as we’ve learnt over the last few months, the computer and mobile devices that millions of us own and carry around with us every day are no exception to this rule.
The smart phones, laptops, and devices that have changed how we communicate…