Search
Content type: Video
Links Read more about your optionsLearn more about PI's position on the Cyber Resilience Act
Content type: Long Read
The security of our devices, applications and infrastructure is paramount to the safe functioning of our digital lives. Good security enables trust in our systems, it is fundamental to protecting the critical information we store and exchange through networks and devices. Similar to how we physically secure our homes, offices and schools, securing devices and software allows us to operate in safe and trusted environments where our security is guaranteed and protected.Security for information…
Content type: Advocacy
We believe the Government's position of refusing to confirm or deny the existence of the Technical Capability Notice or acknowledge Apple's appeal is untenable and violates principles of transparency and accountability.
Content type: Advocacy
While PI recognises the threats posed by cybercrime, PI reiterates the need both for a narrow scope for the proposed Convention, focusing solely on core cyber-dependent crimes, as well as for effective safeguards throughout the entire treaty to ensure human rights are respected and protected, especially in the areas of privacy and freedom of expression. Throughout the negotiations most of proposals by Member States and other stakeholders aimed at restricting the scope of the treaty and…
Content type: Long Read
In June 2023, the UK government announced its proposal to expand its surveillance powers by, among others, forcing communications operators to undermine encryption or abstain from providing security software updates globally. Building on our response to the government’s plans, this piece explains why what they want to do puts every one of us at risk.
Why your trust (to technologies you use) matters
Surveillance and privacy are complex concepts to grasp – it’s part of the appeal to us at PI.…
Content type: Advocacy
Privacy International welcomes the aim of the Cyber Resilience Act to bolster cybersecurity rules to ensure more secure hardware and software products. Nevertheless, we note that the proposal put forward by the European Commission contains certain shortcomings which could both hamper innovation and harm consumers who are increasingly relying on digital products and services.It is essential these shortcomings, detailed below, are effectively addressed by the EU co-legislators through the…
Content type: Long Read
The same day that the United Nations General Assembly convened an emergency special session to respond to Russia’s full-scale invasion of Ukraine in early March, a very different set of negotiations was underway in another U.N. conference room. More than two years after its establishment, the Ad Hoc Committee to Elaborate a Comprehensive International Convention on Countering the Use of Information and Communication Technologies for Criminal Purposes (hereinafter the Ad Hoc Committee) held its…
Content type: News & Analysis
On 30 January 2020, Kenya’s High Court handed down its judgment on the validity of the implementation of the National Integrated Identity Management System (NIIMS), known as the Huduma Namba. Privacy International submitted an expert witness testimony in the case. We await the final text of the judgment, but the summaries presented by the judges in Court outline the key findings of the Court. Whilst there is much there that is disappointing, the Court found that the implementation of NIIMS…
Content type: Long Read
Miguel Morachimo, Executive Director of Hiperderecho. Hiperderecho is a non-profit Peruvian organisation dedicated to facilitating public understanding and promoting respect for rights and freedoms in digital environments.The original version of this article was published in Spanish on Hiperderecho's website.Where does our feeling of insecurity come from? As we walk around our cities, we are being observed by security cameras most of the time. Our daily movement, call logs, and internet…
Content type: Long Read
The pressing need to fix our cybersecurity (mis)understandings
Despite all the efforts made so far by different, cybersecurity remains a disputed concept. Some states are still approving cybersecurity laws as an excuse to increase their surveillance powers. Despite cybersecurity and cybercrime being different concepts, the confusion between them and the broad application of criminal statutes is still leading to the criminalise legitimate behaviour.
All of this represents a sizable challenge…
Content type: Long Read
image from portal gda (cc)
Many people are still confused by what is 5G and what it means for them. With cities like London, New York or San Francisco now plastered with ads, talks about national security, and the deployment of 5G protocols being treated like an arms race, what happens to our privacy and security?
5G is the next generation of mobile networks, which is meant to be an evolution of the current 4G protocols that mobile providers have deployed over the last decade, and there are…
Content type: Report
Like many others, PI were alarmed at recent reports that Facebook have been making mobile phone numbers (which users believed to be) provided for the express purpose of "two-factor authentication" (2FA) both searchable, and a target for advertising by default.
One of the myriad ways Facebook displays targeted adverts to users is through so-called "Custom Audiences". These "custom audiences" are lists of contact details, including phone numbers and email addresses, uploaded by advertisers.…
Content type: Explainer
We look at the recently published report on forensic science in the UK, highlight concerns about police not understanding new tech used to extract data from mobile phones; the risk of making incorrect inferences and the general lack of understanding about the capabilities of these tools.
The delivery of justice depends on the integrity and accuracy of evidence and trust that society has in it. So starts the damning report of the House of Lords Science and Technology Select…
Content type: News & Analysis
Privacy International has joined a global coalition of privacy campaigners, tech companies, and technology experts to respond to proposals by British intelligence chiefs aimed at allowing them access to encrypted messaging apps such as WhatsApp or Signal.
If implemented, the proposals would allow government authorities to force messaging platforms to silently add a law enforcement participant to a group chat or call.
Such a capability poses serious threats to…
Content type: Case Study
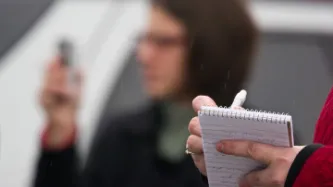
Photo by Roger H. Goun
Chloe is an investigative journalist working for an international broadcast service; we will call the TV show she works for The Inquirer. She travels around the world to work with local journalists on uncovering stories that make the headlines: from human trafficking to drug cartels and government corruption. While her documentaries are watched by many and inspire change in the countries she works in, you would not know who Chloe is if we were to tell you her real name.…
Content type: News & Analysis
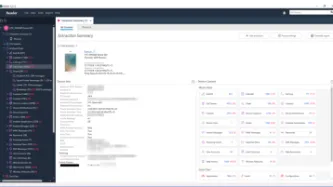
A mobile device is a huge repository of sensitive data, which could provide a wealth of information about its owner and many others with whom the user interacts.
Companies like Cellebrite, MSAB and Oxygen Forensics sell software and hardware to law enforcement. Once your phone is connected to one of these mobile phone extraction tools, the device extracts, analyses and presents the data contained on the phone.
What data these tools can extract and what method is used will…
Content type: News & Analysis
Earlier this month, Brunei attracted international condemnation for a new law that will make gay sex punishable by death. While this is clearly abhorrent, Brunei is not the only country with explicit anti-gay laws.
Homosexuality is criminalised in over 70 countries around the world. And even in countries where gay sex is legal, such as the US, the LGBTIQ+ community still faces discriminatory surveillance and profiling by law enforcement agencies.
Through using the Internet and mobile apps,…
Content type: Long Read
The Privacy International Network is celebrating Data Privacy Week, where we’ll be talking about how trends in surveillance and data exploitation are increasingly affecting our right to privacy. Join the conversation on Twitter using #dataprivacyweek.
Innovations in surveillance and data exploitation present challenges in the fight to protect personal data across the world. Since 1990 we have been working to build a global movement through working with others - from leading civil society…
Content type: Long Read
Since 2004, October has been designated National Cyber Security Awareness Month in the United States. Many other countries have followed suit, as part of the effort to raise awareness about the importance of cybersecurity, and how we can all work together to improve it.
However, cyber security (or sometimes, just ‘cyber’) has not only become a term with multiple and sometimes contradictory meanings - that go from digital security or digital diplomacy to criminal activities with a digital…
Content type: News & Analysis
As the international cyber security debate searches for new direction, little attention is paid to what is going on in Africa. Stepping over the remains of the UN Group of Governmental Experts, and passing by the boardrooms of Microsoft struggling to deliver their Digital Geneva Convention, African nations are following their own individual paths.
Unfortunately, these paths increasingly prioritise intrusive state surveillance and criminalisation of legitimate expression online as…
Content type: Advocacy
Tanto la privacidad como la seguridad son esenciales para proteger a los individuos, su autonomía y su dignidad. El detrimento de la privacidad implica el detrimento de la seguridad de los individuos, sus dispositivos y la infraestructura de la que forman parte. La gente necesita privacidad para sentirse libremente segura y proteger su información, así como para gozar plenamente de otros derechos.
Una cantidad cada vez mayor de Gobiernos en el mundo está recurriendo también al hackeo para…
Content type: Advocacy
Privacy and security are both essential to protecting individuals, including their autonomy and dignity. Undermining privacy undermines the security of individuals, their devices and the broader infrastructure. People need privacy to freely secure themselves, their information, and fully enjoy other rights.
A growing number of governments around the world are embracing hacking to facilitate their surveillance activities. When governments hack for surveillance purposes, they seek to…
Content type: Report
The use of biometric technology in political processes, i.e. the use of peoples’ physical and behavioural characteristics to authenticate claimed identity, has swept across the African region, with 75% of African countries adopting one form or other of biometric technology in their electoral processes. Despite high costs, the adoption of biometrics has not restored the public’s trust in the electoral process, as illustrated by post-election violence and legal challenges to the results of…
Content type: Key Resources
Introduction
Why We Are So Concerned about Government Hacking for Surveillance
Scope of Our Safeguards
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4. Judicial Authorisation
5. Integrity of information
6. Notification
7. Destruction and Return of Data
8. Oversight and Transparency
9. Extraterritoriality
10. Effective Remedy
Commentary on each
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4.…
Content type: News & Analysis
Overview
CIPIT is currently investigating how the privacy of Kenyan citizens was affected by the use of biometric data during the just concluded 2017 general and repeat elections. The IEBC is mandated by law to register voters, verify their registration details and conduct elections. Accordingly, the IEBC is the custodian of the public voter register. There have been reports that individuals received SMS texts from candidates vying for various political seats during the campaign period of the…
Content type: News & Analysis
There are three good reasons why security is so hard for NGOs. First, we are afraid to speak about meaningful security. Second, we focus on the wrong areas of security and in turn spend money and prioritise the wrong things. Third, we struggle to separate the world we want from the worlds we build within our own organisations. At PI we have failed and struggled with each of these for over 20 years. Out of exhaustion, we decided to do something about it: we are building an open framework, a…
Content type: News & Analysis
Photo Credit: MoD UK
‘Security’ in the policy world has practically no currency without a specific prefix. For example, we could discuss 'national' security as distinct from 'consumer' security or 'energy' security. ‘Cyber’ security is the new prefix on the policy block, and it is gradually forcing a rethink on what it means to be secure in a modern society. In the course of Privacy International’s work globally, we have observed that many governments frame cyber security as national security…
Content type: News & Analysis
The past few years have seen a huge rise in the number of attacks both active and passive, against organisations big and small. Attacks against organisations happen for a multitude of reasons: extortion via "ransomware", exfiltration of commercial secrets, or just "the lulz". While this can be crippling to a commercial business, it can potentially be devastating to an NGO, especially those which work to hold powerful institutions to account. The types of information held by such NGOs could…
Content type: News & Analysis
On a hot day in Nairobi, our researcher is speaking to an officer of Kenya’s National Intelligence Service (NIS). The afternoon is wearing on and the conversation has turned to the presidential elections, taking place in August this year. He has just finished describing the NIS’ highly secret surveillance powers and the disturbing ways in which these powers are deployed.
“It is what you might call ‘acceptable deaths,’” he states about the misuse of communications surveillance powers. “People…
Content type: News & Analysis
Privacy can be seen as a reflex of innovation. One of the seminal pieces on the right to privacy as the 'right to be let alone emerged in response to the camera and its use by the tabloid media. Seminal jurisprudence is in response to new surveillance innovations... though often with significant delays.
While one approach would be to say that privacy is a norm and that with modern technologies the norm must be reconsidered and if necessary, abandoned; I think there’s an interesting idea around…