Search
Content type: Long Read
The fourth edition of PI’s Guide to International Law and Surveillance provides the most hard-hitting past and recent results on international human rights law that reinforce the core human rights principles and standards on surveillance. We hope that it will continue helping researchers, activists, journalists, policymakers, and anyone else working on these issues.The new edition includes, among others, entries on (extra)territorial jurisdiction in surveillance, surveillance of public…
Content type: Advocacy
While PI recognises the threats posed by cybercrime, PI reiterates the need both for a narrow scope for the proposed Convention, focusing solely on core cyber-dependent crimes, as well as for effective safeguards throughout the entire treaty to ensure human rights are respected and protected, especially in the areas of privacy and freedom of expression. Throughout the negotiations most of proposals by Member States and other stakeholders aimed at restricting the scope of the treaty and…
Content type: Advocacy
BackgroundThe Snowden revelations and subsequent litigation have repeatedly identified unlawful state surveillance by UK agencies. In response, the UK Parliament passed the highly controversial Investigatory Powers Act 2016 (IPA), which authorised massive, suspicionless surveillance on a scale never seen before, with insufficient safeguards or independent oversight.Privacy International led legal challenges to this mass surveillance regime both before and after the Act became law. The Act…
Content type: Advocacy
PI Opening Statement at PEGA Hearing on "Spyware and ePrivacy"
[check against delivery]
Thank you very much for offering us the opportunity to give evidence before this Committee for a second time.
Privacy International (PI) is a London-based non-profit that researches and advocates globally against government and corporate abuses of data and technology. For years we have been tracking the surveillance industry, challenging unlawful surveillance before national courts as well as the Court of…
Content type: Report
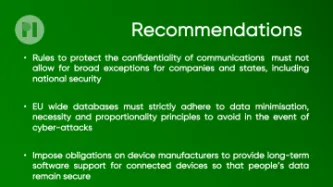
End-to-end encryption (E2EE) contributes significantly to security and privacy. For that reason, PI has long been in favour of the deployment of robust E2EE.Encryption is a way of securing digital communications using mathematical algorithms that protect the content of a communication while in transmission or storage. It has become essential to our modern digital communications, from personal emails to bank transactions. End-to-end encryption is a form of encryption that is even more private.…
Content type: Press release
Amnesty International, Privacy International and The Centre for Research on Multinational Corporations (SOMO) have published a report uncovering NSO Group’s entire corporate structure, tracking the global money trail of both public and private investment into the lucrative spyware company.
Amnesty International and other rights groups have documented dozens of cases of NSO Group’s products being used by repressive governments across the world to put activists, journalists, and opposition…
Content type: Report
In this briefing, Amnesty International, PI and The Centre for Research on Multinational Corporations (SOMO) discuss the corporate structure of NSO group, one of the surveillance industry's well-known participants. The lack of transparency around NSO Group’s corporate structure and the lack of information about the relevant jurisdictions within which it operates are significant barriers in seeking prevention of, and accountability for, human rights violations reportedly linked to NSO Group’s…
Content type: Long Read
On 8 January 2021, the UK High Court issued a judgment in the case of Privacy International v. Investigatory Powers Tribunal. The Secretary of State for Foreign and Commonwealth Affairs and Government Communication Headquarters (GCHQ) appeared as interested parties to the case.
After our initial reaction, below we answer some of the main questions relating to the case.
NOTE: This post reflects our initial reaction to the judgment and may be updated.
What’s the ruling all about?
In…
Content type: News & Analysis
Today, the UK High Court has quashed a decision by the Investigatory Powers Tribunal (IPT) and held that section 5 of the Intelligence Services Act (ISA) 1994 does not permit the issue of general warrants to authorise property interference and certain forms of computer hacking.
The Court referred to cases dating back to the 18th century, which demonstrate the common law’s insistence that the Government cannot search private premises without lawful authority even in the national security…
Content type: Long Read
Miguel Morachimo, Executive Director of Hiperderecho. Hiperderecho is a non-profit Peruvian organisation dedicated to facilitating public understanding and promoting respect for rights and freedoms in digital environments.The original version of this article was published in Spanish on Hiperderecho's website.Where does our feeling of insecurity come from? As we walk around our cities, we are being observed by security cameras most of the time. Our daily movement, call logs, and internet…
Content type: News & Analysis
One of the UK’s largest telecommunications operators, BT, has said to Privacy International that a report claiming it “co-produces malware” with a surveillance company for the GCHQ is inaccurate – but hasn’t said why or given any more details.
The accusation was made by C5IS – a shadowy online publication claiming to be “the most widely read source of information on surveillance technologies”. In its Big Black Book of Electronic Surveillance, it claims that SS8, a…
Content type: News & Analysis
Privacy International has joined a global coalition of privacy campaigners, tech companies, and technology experts to respond to proposals by British intelligence chiefs aimed at allowing them access to encrypted messaging apps such as WhatsApp or Signal.
If implemented, the proposals would allow government authorities to force messaging platforms to silently add a law enforcement participant to a group chat or call.
Such a capability poses serious threats to…
Content type: News & Analysis
Privacy International welcomes WhatsApp's immediate reaction after the revelation that Israeli cyber intelligence company NSO group had exploited a vulnerability in their software. We encourage all WhatsApp users to update their app as soon as possible. However, we believe WhatsApp needs to be much more transparent with their users. We haven't seen a notification on the app itself that would inform users about both, the bug, and the fix. The current version merely states that you can now see…
Content type: Long Read
Imagine that every time you want to attend a march, religious event, political meeting, protest, or public rally, you must share deeply personal information with police and intelligence agencies, even when they have no reason to suspect you of wrongdoing.
First, you need to go to the police to register; have your photo taken for a biometric database; share the contacts of your family, friends, and colleagues; disclose your finances, health records, lifestyle choices, relationship status, and…
Content type: News & Analysis
Federal law enforcement is deploying powerful computer hacking tools to conduct domestic criminal and immigration investigations.
By Alex Betschen, Student Attorney, Civil Liberties & Transparency Clinic, University at Buffalo School of Law
Hacking by the government raises grave privacy concerns, creating surveillance possibilities that were previously the stuff of science fiction. It also poses a security risk, because hacking takes advantage of unpatched vulnerabilities in our…
Content type: Press release
FOR IMMEDIATE RELEASE
December 21, 2018
CONTACTS:
Alex Betschen, Civil Liberties & Transparency Clinic, [email protected], 716–531–6649
Colton Kells, Civil Liberties & Transparency Clinic, [email protected], 585–766–5119
Abdullah Hasan, ACLU, [email protected], 646–905–8879
NEW YORK — Privacy International, the American Civil Liberties Union, and the Civil Liberties & Transparency Clinic of the University at Buffalo School of Law filed a lawsuit today…
Content type: Long Read
As our four year battle against the UK government’s extraordinarily broad and intrusive hacking powers goes to the Supreme Court, we are launching a new fundraising appeal in partnership with CrowdJustice.
We are seeking to raise £5k towards our costs and need your help. If we lose, the court may order us to pay for the government’s very expensive army of lawyers. Any donation you make, large or small, will help us both pursue this important case and protect the future ability of…
Content type: News & Analysis
Privacy International notes a recent ruling issued by Italy’s Supreme Court (Corte di Cassazione) that addresses the need to limit government hacking powers for surveillance purposes and articulates required safeguards when hacking is conducted as part of a criminal investigation.
The ruling addresses the appeals of several individuals involved in a case of corruption; the appeals challenge irregularities in the collection of data as part of the criminal investigation, which resulted in the…
Content type: News & Analysis
This piece was originally published on Just Security.
Ten years ago, an FBI official impersonated an Associated Press reporter to lure and track a teenager suspected of sending in prank bomb threats to his school. To find him, the FBI agent, posing as a reporter, sent the teenager links to a supposed story he was working on, but the links were infested with malware that once clicked on quickly exposed the teen’s location. More recently, the FBI has seized and modified websites so…
Content type: Advocacy
Introduction
Why We Are So Concerned about Government Hacking for Surveillance
Scope of Our Safeguards
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4. Judicial Authorisation
5. Integrity of information
6. Notification
7. Destruction and Return of Data
8. Oversight and Transparency
9. Extraterritoriality
10. Effective Remedy
Commentary on each
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4.…
Content type: Long Read
If you operate an internet company in Russia, you aren’t necessarily surprised to one day open the door to someone, grasping in one hand a bundle of wires and in the other a letter from a government agency demanding access to your servers, with a black box wedged under one arm.
Internet companies in Russia are required by law to store the content of users’ communications for six months and the metadata of users’ communications for three years, essentially meaning that what a person does…
Content type: Impact Case Study
What is the problem
For over two decades we have been documenting an alarming use and spread of surveillance. It is no longer just the wars on terror or drugs or migration that is driving this trend. The management of health crises and distribution of welfare regularly are among others being used to justify this turn to increasingly invasive forms of surveillance. From country to country we see the same ideas and the same profiteers expanding their reach.
When we first released our report on…
Content type: Press release
On 15 March 2017, the Italian Senate voted on a Bill, put forward by Justice Minister Andrea Orlando, that will reform the criminal justice system, including amending the Code of Criminal Procedure. Among the many provisions contained in DDL Orlando, currently pending approval by the Italian House of Representatives, the Government is mandated to regulate, via a legislative decree, the utilisation of malware (commonly referred to as ‘Trojans’ in Italian discourse) to engage hacking for criminal…
Content type: Key Resources
Introduction
Why We Are So Concerned about Government Hacking for Surveillance
Scope of Our Safeguards
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4. Judicial Authorisation
5. Integrity of information
6. Notification
7. Destruction and Return of Data
8. Oversight and Transparency
9. Extraterritoriality
10. Effective Remedy
Commentary on each
1. Legality
2. Security and Integrity of Systems
3. Necessity and Proportionality
4.…
Content type: Press release
On 5 October 2017, Privacy International will appear before the UK Court of Appeal to continue its challenge to the British government's large scale hacking powers. The case questions the decision by the Investigatory Powers Tribunal (IPT) to sanction the UK government's power to hack broad categories of people or property without any individualised suspicion.
TIMELINE AND KEY POINTS
- Privacy International began fighting bulk government hacking in 2014 at the…
Content type: Press release
Please find attached a copy of the briefing along with promotional photographs with the briefing.
Privacy International has today sent top EU and UK Brexit negotiators* a briefing on their vulnerability to potential surveillance by each other, and others. Brexit negotiations are to begin today.
The global privacy rights NGO has highlighted to the negotiators the risk of sophisticated surveillance capabilities being deployed against each other and by others, and provided…
Content type: News & Analysis
Dear Minister Dr. Wolfgang Brandstetter, Minister Mag. Wolfgang Sobotka, Minister Dr.in Pamela Rendi-Wagner, MSs, Minister Mag. Hans Peter Doskozil,
Privacy International is a United Kingdom-based non-governmental organization, which is dedicated to protecting the right to privacy around the world. Privacy International is committed to ensuring that government surveillance complies with the rule of law and the international human rights framework. As part of this commitment, Privacy…
Content type: News & Analysis
Why would we ever let anyone hack anything, ever? Why are hacking tools that can patently be used for harm considered helpful? Let's try to address this in eight distinct points:
1) Ethical hacking is a counter proof to corporate claims of security.
Companies make products and claim they are secure, or privacy preserving. An ethical hack shows they are not. Ethical hackers produce counter-proofs to government or corporate claims of security, and thus defend us, piece by tiny…
Content type: Press release
Privacy International Executive Director Dr Gus Hosein said:
“If today’s leaks are authenticated, they demonstrate what we’ve long been warning about government hacking powers — that they can be extremely intrusive, have enormous security implications, and are not sufficiently regulated. Insufficient security protections in the growing amount of devices connected to the internet or so-called “smart” devices, such as Samsung Smart TVs, only compound the problem, giving governments easier…