Search
Content type: News & Analysis
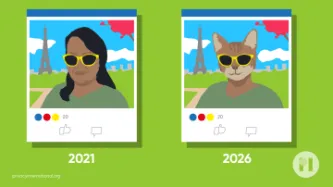
What if we told you that every photo of you, your family, and your friends posted on your social media or even your blog could be copied and saved indefinitely in a database with billions of images of other people, by a company you've never heard of? And what if we told you that this mass surveillance database was pitched to law enforcement and private companies across the world?
This is more or less the business model and aspiration of Clearview AI, a company that only received worldwide…
Content type: News & Analysis
It is difficult to imagine a more intrusive invasion of privacy than the search of a personal or home computer ... when connected to the internet, computers serve as portals to an almost infinite amount of information that is shared between different users and is stored almost anywhere in the world.
R v Vu 2013 SCC 60, [2013] 3 SCR 657 at [40] and [41].
The controversial Police Crime Sentencing and Courts Bill includes provision for extracting data from electronic devices.
The Bill…
Content type: Examples
When Dallas police posted on Twitter asking for videos of the protests taking place after George Floyd's killing, a flood of videos and images of K-pop stars were uploaded to its anonymous iWatch Dallas tip-off app. Law enforcement can call on vast numbers of networked cameras - from cars, food and retail chains that are typically willing to share with police, law enforcement agencies' own networks of surveillance and body cameras as well as object and face recognition software, protesters and…
Content type: Case Study
Facial recognition technology (FRT) is fairly present in our daily lives, as an authentication method to unlock phones for example. Despite having useful applications, FRT can also be just another technology used by those in power to undermine our democracies and carry out mass surveillance. The biometric data collected by FRT can be as uniquely identifying as a fingerprint or DNA. The use of this technology by third parties, specially without your consent, violates your right to privacy.
The…
Content type: Long Read
In April 2018, Amazon acquired “Ring”, a smart security device company best known for its video doorbell, which allows Ring users to see, talk to, and record people who come to their doorsteps.
What started out as a company pitch on Shark Tank in 2013, led to the $839 million deal, which has been crucial for Amazon to expand on their concept of the XXI century smart home. It’s not just about convenience anymore, interconnected sensors and algorithms promise protection and provide a feeling of…
Content type: News & Analysis
Yesterday, Amazon announced that they will be putting a one-year suspension on sales of its facial recognition software Rekognition to law enforcement. While Amazon’s move should be welcomed as a step towards sanctioning company opportunism at the expense of our fundamental freedoms, there is still a lot to be done.
The announcement speaks of just a one-year ban. What is Amazon exactly expecting to change within that one year? Is one year enough to make the technology to not discriminate…
Content type: Long Read
On 12 April 2020, citing confidential documents, the Guardian reported Palantir would be involved in a Covid-19 data project which "includes large volumes of data pertaining to individuals, including protected health information, Covid-19 test results, the contents of people’s calls to the NHS health advice line 111 and clinical information about those in intensive care".
It cited a Whitehall source "alarmed at the “unprecedented” amounts of confidential health information being swept up in the…
Content type: Case Study
In 2015, James Bates was charged with first-degree murder in the death of Victor Collins. Collins was found floating face down in Bates’ hot tub in November 2015. Bentonville police served two search warrants ordering Amazon to turn over the “electronic data in the form of audio recordings, transcribed records, text records and other data contained on the Amazon Echo device” in Bates’ home.
The reason for the warrants? According to the police, just because the device was in the house that…
Content type: News & Analysis
Cloud extraction allows law enforcement agencies to take huge amounts of your data from the Cloud via a legal back door. If law enforcement seize your phone or take it from a victim of crime, they can extract tokens or passwords from the device which lets them get access to data from apps such as Uber, Instagram, Slack, Gmail, Alexa and WhatsApp.
In so doing, law enforcement agencies can avoid official channels through cloud companies such as Google, Apple…
Content type: Long Read
Mobile phones remain the most frequently used and most important digital source for law enforcement investigations. Yet it is not just what is physically stored on the phone that law enforcement are after, but what can be accessed from it, primarily data stored in the Cloud.
Cellebrite, a prominent vendor of surveillance technology used to extract data from mobile phones, notes in its Annual Trend Survey that in approximately half of all investigations, cloud data ‘appears’ and that…
Content type: Press release
A large number of apps on smart phones store data in the cloud. Law enforcement can access these vast troves of data from devices and from popular apps with the push of a button using cloud extraction technology.
Mobile phones remain the most frequently used and most important digital source for law enforcement investigations. Yet it is not just what is physically stored on the phone that law enforcement are after, but what can be accessed from it, primarily data stored in the Cloud.…
Content type: Examples
A woman was killed by a spear to the chest at her home in Hallandale Beache, Florida, north of Miami, in July. Witness "Alexa" has been called yet another time to give evidence and solve the mystery. The police is hoping that the smart assistance Amazon Echo, known as Alexa, was accidentally activated and recorded key moments of the murder. “It is believed that evidence of crimes, audio recordings capturing the attack on victim Silvia Crespo that occurred in the main bedroom … may be found on…
Content type: Examples
In yet another murder case, a New Hampshire judge ordered Amazon to turn over two days of Amazon Echo recordings in a double murder case in November 2018.
Prosecutors believe that recordings from an Amazon Echo in the Farmington home where two women were murdered in January 2017 may yield further clues as to who their killer might be. Though the Echo was seized when police secured the crime scene, the recordings are stored on Amazon servers.
Timothy Verrill, of Dover, New Hampshire, was…
Content type: Examples
In 2015, James Bates (of Arkansas, United States) was charged with first-degree murder in the death of Victor Collins. Collins was found floating face down in Bates’ hot tub in November 2015, police said. Amazon Echo entered the murder case because someone present on the night of Collins’ death recalled hearing music streaming through the device. It was widely reported that Amazon fought the prosecution’s request to hand over data recorded by the device that night. Eventually, the argument…
Content type: Case Study
Our connected devices carry and communicate vast amounts of personal information, both visible and invisible.
What three things would you grab if your house was on fire? It’s a sure bet your mobile is going to rank pretty high. It’s our identity, saying more about us than we perhaps realise. It contains our photos, calendar, internet browsing, locations of where we go, where we’ve been, our emails, social media. It holds our online banking, notes with half written poems, shopping lists, shows…