Advanced Search
Content Type: Video
Immediately following the UK general election in December 2019, we worked with Open Rights Group to commission a YouGov poll about public understanding and public opinion about the use of data-driven campaigning in elections.
The poll used a representative sample of 1,664 adults across the UK population.
'Data-driven political campaigning' is about using specific data about you to target specific messages at you. So, for this might involve knowing that you are, for example, likely to…
Content Type: News & Analysis
IMSI catchers (or stingrays as they are known in the US) are one of the surveillance technologies that has come to the forefront again in the protests against police brutality and systemic racism that have been sparked by the murder of George Floyd on 25 May 2020.
An International Mobile Subscriber Identity catcher – in short an “IMSI catcher” – is an intrusive piece of technology that can be used to locate and track all mobile phones that are switched on in a certain area. It does so by…
Content Type: Long Read
Monday, 16 June 2025
It’s 7:33 am. Lila’s GoogBit watch vibrates. “You got 6 hours and 57 minutes of sleep last night, including 2 hours and 12 minutes of deep sleep”, the watch reads. “In total, you tossed and turned for 15 minutes only”. Taking into account Lila’s online browsing activity, her sleep pattern, the recent disruptions in some of her other biorhythms, as well as her daily schedule, GoogBit watch has calculated the very best minute to wake her up.
Content Type: Call to Action
Google wants to know everything about you.It already holds a massive trove of data about you, but by announcing its plans to acquire the health and fitness tracker company Fitbit, it now clearly wants to get its hands on your health too. We don’t think any company should be allowed to accumulate this much intimate information about you. This is why we’re trying to stop its merger with Fitbit.Google and Fitbit need the European Commission’s approval before they can merge. The merger would have…
Content Type: Press release
Today, the ICO has issued a long-awaited and critical report on Police practices regarding extraction of data from people's phones, including phones belonging to the victims of crime.
The report highlights numerous risks and failures by the police in terms of data protection and privacy rights. The report comes as a result of PI’s complaint, dating back to 2018, where we outlined our concerns about this intrusive practice, which involves extraction of data from devices of victims, witnesses…
Content Type: Report
Back in October 2019, PI started investigating advertisers who uploaded personal data to Facebook for targeted advertising purposes. We decided to take a look at "Advertisers Who Uploaded a Contact List With Your Information", a set of information that Facebook provides to users about advertisers who upload files containing their personal data (including unique identifier such as phone numbers, emails etc...). Looking at the limited and often inaccurate information provided by Facebook through…
Content Type: News & Analysis
Traduction réalisée par Nadine Blum.
Le 29 mai, le Congrès nigérien a voté une loi permettant au gouvernement d’intercepter largement certaines communications électroniques. La loi rend légale l’interception de communications, autorisée par le gouvernement, sans protections appropriées ni mécanismes de contrôle.
La loi a été adoptée avec 104 votes pour – le Parlement nigérien compte 171 membres – et sans la participation de l’opposition qui a boycotté la loi. L’opposition a affirmé…
Content Type: News & Analysis
On 29 May, Niger’s Congress voted on a law allowing for broad interception powers of certain electronic communications by the government. The bill makes it lawful for the government to approve the interception of communications without appropriate safeguards or oversight mechanisms.
The law passed with 104 votes – the Nigerien parliament has 171 members – without the participation of the opposition that boycotted the law. The opposition claimed that
the law will allow those, for…
Content Type: Long Read
Covid Apps are on their way to a phone near you. Is it another case of tech-solutionism or a key tool in our healthcare response to the pandemic? It’s fair to say that nobody quite knows just yet.
We’ve been tracking these apps since the early days. We’ve been monitoring Apple and Google closely, have been involved in the UK’s app process, our partners in Chile and Peru have been tracking their governments’ apps, and more.
Of course privacy concerns arise. But only a simplistic analysis would…
Content Type: Long Read
Today is 1st May, an international day of protest. It also marks a year since PI launched our new programme of work called ‘Defending Democracy and Dissent’.
One year on we find ourselves in a situation where 1 May protests in the streets will not be going ahead. Rights have been restricted around the world. Sadly we’re seeing some actors exploit this public health crisis to enhance their own power, expanding surveillance and opportunism.
Against this challenging back-drop we wanted to…
Content Type: Long Read
‘Let’s build an app for that’ has become the response to so many things. It’s no surprise it’s happening now.
Apps are notorious for their lack of security and privacy safeguards, exploiting people’s data and devices. Now we’re being asked to trust governments with their proposed apps -- of which there are many. These are the very same governments who have been keen to exploit data in the past. For instance, PI currently has four outstanding legal cases arising from the last times governments…
Content Type: News & Analysis
Almost a year and a half ago we complained about seven companies to three data protection authorities in Europe. These companies, ranging from AdTech to data brokers and credit rating agencies, thrive on the collection, exploitation and processing of personal data. They profile and categorise people - without our knowledge and infringing multiple legal requirements.
Now, the French Data Protection Authority CNIL has informed us that they are following the same route and …
Content Type: Long Read
Commercial interests seem to often overshadow the EU’s stance as a global privacy leader. After looking at Europes's shady funds to border forces in the Sahel area, Niger's new biometric voting system, and attempts to dismantle smugglers networks powered by Europe's gifts of surveillance, freelance journalist Giacomo Zandonini looks at the battle for data protection and digital rights in the continent.
What do a teenage labourer on a marijuana farm in Lesotho, a…
Content Type: Long Read
Background
Kenya’s National Integrated Identity Management Scheme (NIIMS) is a biometric database of the Kenyan population, that will eventually be used to give every person in the country a unique “Huduma Namba” for accessing services. This system has the aim of being the “single point of truth”, a biometric population register of every citizen and resident in the country, that then links to multiple databases across government and, potentially, the private sector.
NIIMS was introduced…
Content Type: Case Study
Anyone who is arrested should be informed of the reasons for their arrest and any charges against them. Anyone who is detained is also entitled to a trial within a reasonable time, or to be released if no charges are held against them.
Privacy enhances these protections. It provides limitations on the manner in which information can be obtained about you, and the kind of information that can be accessed about you by law enforcement, who can access that information and how they can use it.…
Content Type: Case Study
In early May 2019, it was revealed that a spyware, exploiting a vulnerability in Facebook’s WhatsApp messaging app, had been installed onto Android and iOS phones. The spyware could be used to turn on the camera and mic of the targeted phones and collect emails, messages, and location data. Citizen Lab, the organization that discovered the vulnerability, said that the spyware was being used to target journalists and human rights advocates in different countries around the world. The spyware…
Content Type: News & Analysis
In mid-2019, MI5 admitted, during a case brought by Liberty, that personal data was being held in “ungoverned spaces”. Much about these ‘ungoverned spaces’, and how they would effectively be “governed” in the future, remained unclear. At the moment, they are understood to be a ‘technical environment’ where personal data of unknown numbers of individuals was being ‘handled’. The use of ‘technical environment’ suggests something more than simply a compilation of a few datasets or databases.
The…
Content Type: News & Analysis
On 30 January 2020, Kenya’s High Court handed down its judgment on the validity of the implementation of the National Integrated Identity Management System (NIIMS), known as the Huduma Namba. Privacy International submitted an expert witness testimony in the case. We await the final text of the judgment, but the summaries presented by the judges in Court outline the key findings of the Court. Whilst there is much there that is disappointing, the Court found that the implementation of NIIMS…
Content Type: Long Read
It was a quiet evening in Agadez, a bustling Saharan city in the centre of Niger. Thirty-five year old Agali Ahmed was sipping tea at a friend’s place, as he often did, when he received a message: police were at his uncle’s house. When he got there, Ahmed saw men in plainclothes, standing around the building’s gate. Inside, more men were searching the apartment. Three white men, who Ahmed guessed were Spanish, asked for his phone and started taking pictures of him. They told him to follow them…
Content Type: News & Analysis
Today Advocate General (AG) Campos Sánchez-Bordona of the Court of Justice of the European Union (CJEU), issued his opinions (C-623/17, C-511/18 and C-512/18 and C-520/18) on how he believes the Court should rule on vital questions relating to the conditions under which security and intelligence agencies in the UK, France and Belgium could have access to communications data retained by telecommunications providers.
The AG addressed two major questions:
(1) When states seek to impose…
Content Type: Advocacy
In December 2019 Privacy International made submissions to Police Scotland in relation to documents designed to explain to the public how cyber kiosks will work and what information will be given to victims when Police Scotland extract data from their phone.
Police Scotland rely on 'consent' to seize a phone from a victim. We believe the lack of information provided to the individual regarding extraction, examination, retention, deletion, sharing and search parameters undermines that any…
Content Type: News & Analysis
Updated January 18th 2021
The Government of Myanmar is pushing ahead with plans to require anyone buying a mobile SIM card to be fingerprinted and hand over their ID cards, according to procurement documents circulated to prospective bidders.
The plans are a serious threat to privacy in a country lacking any data protection or surveillance laws and where minorities are systematically persecuted, and must be scrapped.
According to technical requirements developed by Myanmar’s Post and…
Content Type: Advocacy
As any data protection lawyer and privacy activist will attest, there’s nothing like a well-designed and enforced data protection law to keep the totalitarian tendencies of modern Big Brother in check.
While the EU’s data protection rules aren’t perfect, they at least provide some limits over how far EU bodies, governments and corporations can go when they decide to spy on people.
This is something the bloc’s border control agency, Frontex, learned recently after coming up with a plan to…
Content Type: News & Analysis
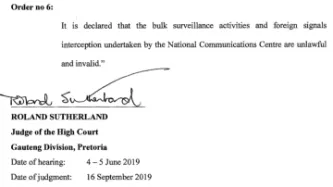
Today, the High Court of South Africa in Pretoria in a historic decision declared that bulk interception by the South African National Communications Centre is unlawful and invalid.
The judgment is a powerful rejection of years of secret and unchecked surveillance by South African authorities against millions of people - irrespective of whether they reside in South Africa.
The case was brought by two applicants, the amaBhungane Centre for Investigative Journalism and journalist Stephen…
Content Type: News & Analysis
The global counter-terrorism agenda is driven by a group of powerful governments and industry with a vested political and economic interest in pushing for security solutions that increasingly rely on surveillance technologies at the expenses of human rights.
To facilitate the adoption of these measures, a plethora of bodies, groups and networks of governments and other interested private stakeholders develop norms, standards and ‘good practices’ which often end up becoming hard national laws…
Content Type: News & Analysis
The Watson/Tele2 decision of the CJEU concerned section 1 and 2 of DRIPA and the Data Retention Regulations 2014. This contained the legislative scheme concerning the power of the Secretary of State to require communications service providers to retain communications data. Part 3 of the Counter-Terrorism and Security Act 2015 amended DRIPA so that an additional category of data - that necessary to resolve Internet Protocol addresses - could be included in a requirement to retain…
Content Type: Advocacy
RESPONSE OF PRIVACY INTERNATIONAL TO THE CONSULTATION ON THE GOVERNMENT’S PROPOSED RESPONSE TO THE RULING OF THE COURT OF JUSTICE OF THE EUROPEAN UNION ON 21 DECEMBER 2016 REGARDING THE RETENTION OF COMMUNICATIONS DATA
[Full response below]
Introduction
The consultation is in response to the judgment in Tele2 Sverige AB v Post-och telestyrelsen (Case-203/15) and R (Watson) v Secretary of State for the Home Department (Case C-698/15) [“Watson judgment”].
The case concerned…
Content Type: Long Read
Six years after NSA contractor Edward Snowden leaked documents providing details about how states' mass surveillance programmes function, two states – the UK and South Africa – publicly admit using bulk interception capabilities.Both governments have been conducting bulk interception of internet traffic by tapping undersea fibre optic cables landing in the UK and South Africa respectively in secret for years.Both admissions came during and as a result of legal proceedings brought by Privacy…
Content Type: Explainer
Recently the role of social media and search platforms in political campaigning and elections has come under scrutiny. Concerns range from the spread of disinformation, to profiling of users without their knowledge, to micro-targeting of users with tailored messages, to interference by foreign entities, and more. Significant attention has been paid to the transparency of political ads - what are companies doing to provide their users globally with meaningful transparency into how they…
Content Type: News & Analysis
Today, Privacy International, along with nine other NGOs including Liberty and Amnesty International, attended a hearing before the Grand Chamber of the European Court of Human Rights (ECtHR) to revisit the Court's first ruling on our case challenging UK mass surveillance and intelligence sharing. In September 2018, the First Section of the ECtHR ruled that the UK government's mass interception program violates the rights to privacy and freedom of expression. Notwithstanding the positve aspects…