Search
Content type: Long Read
“Hey [enter AI assistant name here], can you book me a table at the nearest good tapas restaurant next week, and invite everyone from the book club?” Billions of dollars are invested in companies to deliver on this. While this is a dream that their marketing departments want to sell, this is a potential nightmare in the making.Major tech companies have all announced flavours of such assistants: Amazon’s Alexa+, Google’s Gemini inspired by Project Astra, Microsoft’s Copilot AI companion and…
Content type: Long Read
On 13 March 2025, we filed a complaint against the UK government challenging their use of dangerous, disproportionate and intrusive surveillance powers to undermine the privacy and security of people all over the world. Here, we answer some key questions about the case and the recent events that led to this development.Note: This post was last updated on 13 March 2025.What’s the fuss about?A month ago, it was reported that the UK government demanded Apple Inc – maker of the iPhone, iPads, Macs…
Content type: Guide step
In your day-to-day life, your smartphone silently captures and stores a digital footprint of your whereabouts by keeping a location history: this history is then used to enhance your mobile experience, such as by aiding in navigation and customizing app experiences according to your location habits.
Yet, it's essential to recognize the potential risks tied to this seemingly innocuous practice. Understanding how your location data is handled becomes vital, as it can impact your privacy in ways…
Content type: Guide step
Many mainstream Internet platforms, such as YouTube and X, often collect extensive user data, track online activities, and employ algorithms to create content recommendations based on individual preferences. For a privacy-conscious user, this is nothing short of a nightmare. Making use of alternative front-ends allows you to access the content you want, while minimising the data collected about you. Essentially, this corresponds to using a different website to access the same content. By using…
Content type: Long Read
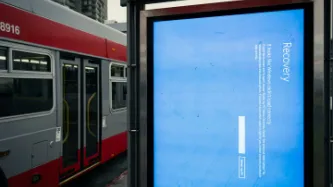
What happened?On 19 July 2024, American cybersecurity company CrowdStrike released an update to its CrowdStrike Falcon software that ultimately caused 8.5 million computers running Microsoft Windows to crash. The damage done was both deep and wide: deep because the computers affected were unable to recover without direct user intervention. Wide because a whole range of companies - from airlines to healthcare to media - across a whole range of countries - from Sweden to India to New Zealand -…
Content type: Long Read
IntroductionIn early October this year, Google announced its AI Overviews would now have ads. AI companies have been exploring ways to monetise their AI tools to compensate for their eye watering costs, and advertising seems to be a part of many of these plans. Microsoft have even rolled out an entire Advertising API for its AI chat tools.As AI becomes a focal point of consumer tech, the next host of the AdTech expansion regime could well be the most popular of these AI tools: AI chatbots.…
Content type: Long Read
IntroductionHarnessing new digital technology to improve people’s health is now commonplace across the world. Countries and international organisations alike are devising digital health strategies and looking to emerging technology to help solve tricky problems within healthcare. At the same time, more and more start-ups and established tech companies are bringing out new, and at times innovative, digital tools aimed at health and wellbeing.
Content type: Examples
Google has settled a case brought in 2020 by the parents of an Illinois girl who sued the company in state court alleging that it had violated two sections of the Biometric Information Privacy Act. The case also alleged that Google had violated the law by failing to obtain parental consent to collect, store, and use biometric data belonging to millions of children and had illegally harvest other data such as physical location, website histories, personal contact lists, passwords, and…
Content type: Long Read
INTRODUCTION
In recent years, major tech platforms have been rapidly evolving their business models. Despite their dominance in various markets, tech giants like Google and Meta are venturing into new territories to expand their user base. One of the most striking ventures has been their foray into the "connectivity market" through substantial, and occasionally unsuccessful, investments in network infrastructure.
Many tech companies are investing resources into network infrastructure, either…
Content type: Explainer
IntroductionThe emergence of large language models (LLMs) in late 2022 has changed people’s understanding of, and interaction with, artificial intelligence (AI). New tools and products that use, or claim to use, AI can be found for almost every purpose – they can write you a novel, pretend to be your girlfriend, help you brush your teeth, take down criminals or predict the future. But LLMs and other similar forms of generative AI create risks – not just big theoretical existential ones – but…
Content type: Long Read
IntroductionFor years PI has been documenting the market dominance and associated power of Big Tech over the digital economy, and the threats this poses to our privacy and wider rights.The digital economy is characterised by a handful of Big Tech companies that have established and maintained dominance over the digital market through opaque and exploitative practices. Big Tech exploits the data of those who use their platforms in ways which interfere with our privacy and wider rights. In…
Content type: Long Read
Table of contentsIntroductionWeighing the (potential) benefits with the risksPrivacy rights and the right to healthThe right to healthPrivacy, data-protection and health dataThe right to health in the digital contextWhy the drive for digitalImproved access to healthcarePatient empowerment and remote monitoringBut these same digital solutions carry magnified risks…More (and more connected) dataData leaks and breachesData sharing without informed consentProfiling and manipulationTools are not…
Content type: News & Analysis
Is the AI hype fading? Consumer products with AI assistant are disappointing across the board, Tech CEOs are struggling to give examples of use cases to justify spending billions into Graphics Processing Units (GPUs) and models training. Meanwhile, data protection concerns are still a far cry from having been addressed.
Yet, the believers remain. OpenAI's presentation of ChatGPT was reminiscent of the movie Her (with Scarlett Johannsen's voice even being replicated a la the movie), Google…
Content type: Examples
Foodinho, the Italian food delivery subsidiary of the Spanish company Glovo, continues to accumulate millions of euros in fines for infringements of labour law such as collecting and misusing riders' data. New research studying Glovo's app indicates that the company appears to have created its own hidden scoring system so evaluate couriers' performance, and shares personally identified riders' after-hours location with Google and other unauthorised third-party trackers.https://algorithmwatch.…
Content type: Examples
Companies like the Australian data services company Appen are part of a vast, hidden industry of low-paid workers in some of the globe's cheapest labour markets who label images, video, and text to provide the datasets used to train the algorithms that power new bots. Appen, which has 1 million contributors, includes among its clients Amazon, Microsoft, Google, and Meta. According to Grand View Research, the global data collection and labelling market was valued at $2.22 billion in 2022 and is…
Content type: Examples
Fairplay and the Center for Digital Democracy are asking the US Federal Trade Commission to investigate whether Google and YouTube are violating the Children's Online Privacy Protection Act and the terms of a 2019 settlement agreement by serving children personalised ads on videos labelled "made for kids". The two organisations, along with EPIC and Common Sense Media, believe the FTC should seek penalties topping tens of billions of dollars. In the 2019 settlement Google and YouTube were…
Content type: Examples
Chromebooks, which many schools purchased at the beginning of the pandemic because of their lower cost compared to PCs and Macs, are proving expensive as their prices rise, the cost of repairs bites, and Google's expiration policy means many models are about to become e-waste. A study from US PIRG finds that doubling the Chromebooks' lifespan could save public schools $1.8 billion. Older Macs and PCs, by contrast, can go on being used and have resale value. Article: Chromebooks expire to…
Content type: Examples
Google is working to extend the lifespan of Chromebooks by providing software updates for up to a decade. The new policy, which will begin in 2024, will ensure that no current Chromebook expires in the next two years. The expiration dates were proving expensive for schools, which were having to spend millions of dollars on replacements because unsupported Chromebooks can't be used for mandatory state testing. Article: Google extends life of ChromebooksPublication: Wall Street JournalWriter…
Content type: Examples
UK government ministers are seeking to ensure schools benefit financially from any future use of pupils’ data by large language models such as those behind ChatGPT and Google Bard. Data from the national pupil database is already available to third-party organisations. The BCS head of education recommends that the Department of Education should write a clear public benefits statement to ensure that initiatives benefit pupils as well as providing financial benefits.https://schoolsweek.co.uk/…
Content type: Examples
Human raters have played a significant role in the rapid improvement in the machine learning models that fuel modern AI. The raters evaluate the algorithmic output of search engines and AI chatbots and provide "Reinforcement Learning with Human Feedback" (RLHF) – the technical name for the deployment of such ratings to improve AI models. The efforts of these workers, who are mostly located in the global South but include thousands in the US, is downplayed by the technology companies to whom…
Content type: Examples
Delivery drivers in Jakarta use GPS-spoofing apps in order to improve their chances of selection by the Gojek delivery and transport app, an equivalent to Apple Pay, Postmates, Venmo, and Uber all in one. Gojek that operates in more than 200 cities in Indonesia, Singapore, Vietnam, and Thailand. Other grey market apps enlarge details of orders that are too small to read, automate bidding, and apply filters to open orders. Some apps are distributed via Google Play; more are sold via driver…
Content type: Long Read
IntroductionData about our health reveals some of the most sensitive, intimate - and potentially embarrassing - information about who we are. Confidentiality is, and has always been, at the very heart of medical ethics. People need to be able to trust their doctors, nurses and other healthcare providers so that they are not afraid to tell them something important about their health for fear of shame, judgement or social exclusion.It’s no surprise then that data protection regimes around…
Content type: Video
Since we recorded this podcast there has been an update on the Microsoft Activision mergerLinksPI competition page (our "very influential work")More about Dr MantzariEcosystems and competition law in theory and practice - a research paper about ecosystemsPower Imbalances in Online Marketplaces: At the Crossroads of Competition Law and Regulation - one of Dr Deni's papers looking at peconomic dependence in online marketplacesGoogle Android European court case on abuse of dominance and more info…
Content type: Long Read
Introduction
The 28th of September marks International Safe Abortion Day. It remains a day necessary to mobilise and raise awareness of the continued struggles women and girls face when accessing reproductive healthcare, including access to safe abortion. Across the world, abortion continues to be criminalised, restricted and in some places under attack. All of which constitute severe obstacles for women and girls to fully exercise their human rights, particularly their right to privacy, which…
Content type: Examples
Four people in Kenya have filed a petition calling on the government to investigate conditions for contractors reviewing the content used to train large language models such as OpenAI's ChatGPT. They allege that these are exploitative and have left some former contractors traumatized. The petition relates to a contract between OpenAI and data annotation services company Sama. Content moderation is necessary because LLM algorithms must be trained to recognise prompts that would generate harmful…
Content type: Examples
Hong Kong authorities seeking to ensure the complete removal of the popular pro-democracy protest song "Glory to Hong Kong" from search results got an injunction against Google after the technology giant refused to remove it without a court order. The authorities say in the writ that they are seeking to stop anyone with seditious intent from publishing or distributing the song in any media. After a hearing, the court denied the authorities' request.
https://www.scmp.com/news/hong-kong/politics…
Content type: Advocacy
Background
In August 2022, Amazon announced that they had entered into a definitive merger agreement to acquire iRobot, a company that specialises in designing and building consumer robots. The transaction was formally notified to the European Commission on 1 June 2023, while the UK Competition and Markets Authority (CMA) has already launched an investigation into the transaction since April 2023.
We believe that this acquisition is likely to significantly impede effective competition in and…
Content type: Long Read
With the introduction of GPS tracking of people on immigration bail, the UK has recently put GPS ankle tags, and their potential privacy and security issues, under the spotlight. PI has exposed the intrusive nature and shortcomings of these devices through technical explainers and complaints to the UK data protection and forensic science regulators.
But, what better way to understand the risks associated with a device than to actually use one? In order to further consolidate our understanding…
Content type: Long Read
In 2022, Privacy International continued to produce real change by challenging governments and corporations that use data and technology to exploit us. And, we produced substantial impact that directly affects each of us.
Here are a handful of our biggest achievements in 2022.
WE CHALLENGED COMPANIES TO CHANGE THEIR BUSINESS MODELS AND PRACTICES
Regulators in UK, France, Greece, and Italy fined and restricted Clearview AI’s activity
Clearview AI built a massive database of our biometrics, by…
Content type: Examples
In a report, the UK's Digital Futures Commission warns that the explosion of use of education technology brings risks to children's privacy, especially that the data it collects, much of it personally identifiable, will be entered into the heavily commercial global data ecosystem, with uncertain consequences for the future. Although schools have returned to in-person learning, tools such as Google Classroom and Class Dojo have become permanently entrenched even though they have "opaque" privacy…