Advanced Search
Content Type: Long Read
Valentine’s Day is traditionally a day to celebrate relationships, but many relationships that begin romantically can quickly become controlling, with partners reading emails, checking texts and locations of social media posts. This can be just the beginning.
Today, Friday 14th February, Privacy International and Women’s Aid are launching a series of digital social media cards giving women practical information on how to help stay safe digitally from control and abuse.
Did you know…
Content Type: Long Read
We are excited to spotlight our Reproductive Rights and Privacy Project!
The Project is focused on researching and exposing organisations that collect and exploit the information of those seeking to exercise their reproductive rights. Working together with PI partners, other international grassroots organisations and NGOs, PI is researching and advocating against this data exploitation.
So, what are reproductive rights?
Sexual and reproductive rights, which are contained within Economic,…
Content Type: News & Analysis
Privacy shouldn’t be a luxury.
Google claim to agree with us - we know that because Sundar Pichai, their CEO, said so this May in the New York Times. And yet, Google are enabling an ecosystem that exploits people who own low-cost phones.
Today we, along with over 50 organisations including Amnesty International, DuckDuckGo, and the ACLU are asking Google to step up, and we’re asking you to join us in pressuring them to do the right thing.
Sign the petition
Google has the power to…
Content Type: Advocacy
You can find the letter below. Add your voice to this campaign by signing our petition if you believe that its time Google stopped enabling exploitation.
Note: This letter is also available in French and Spanish
Dear Mr. Pichai,
We, the undersigned, agree with you: privacy cannot be a luxury offered only to those people who can afford it.
And yet, Android Partners - who use the Android trademark and branding - are manufacturing devices that contain pre-installed apps that cannot be deleted…
Content Type: Advocacy
Puede encontrar la carta a continuación. Agregue su voz a esta campaña firmando nuestra petición si cree que es hora de que Google deje de permitir la explotación.
Nota: Esta carta también está disponible en francés e inglés.
Estimado Sr. Pichai,
Nosotros, los firmantes, estamos de acuerdo con usted: la privacidad no puede ser un lujo reservado para las personas que tienen la capacidad de pagar por ella.
Sin embargo, los socios de Android Partner –que utilizan la marca y la imagen de…
Content Type: Call to Action
You should know what new technologies police are deploying on your local community. We want to find out if UK police are using cloud extraction tech, what law exists to protect your rights and what safeguards are in place. We need your help.
See our new report for more info on cloud extraction
If you are not based in the UK but have a FOIA regime in your country you can still use our template text below and check if there is a FOIA platform to use here to send it in your own…
Content Type: Advocacy
Vous pouvez trouver la lettre ci-dessous. Ajoutez votre voix à cette campagne en signant notre pétition si vous pensez qu'il est temps que Google cesse d'activer l'exploitation.
Ce contenu est également disponible en anglais et en espagnol.
Cher M. Pichai,
Nous, les organisations signataires, sommes d’accord avec vous :
la vie privée n’est pas un luxe, offert seulement à ceux qui en ont les moyens.
Pourtant, les « Android Partners » – qui utilisent la marque déposée…
Content Type: News & Analysis
Send a Freedom of Information Request to your local police for to see if they are using cloud extraction here.
On 12 December 2018 a member of Lancashire Police Department UK told viewers of a Cellebrite webinar that they were using Cellebrite's Cloud Analyser to obtain cloud based 'evidence'. In response to a Freedom of Information request Hampshire Constabulary told Privacy International they were using Cellebrite Cloud Analyser.
They are not alone. In Cellebrite's…
Content Type: Press release
A large number of apps on smart phones store data in the cloud. Law enforcement can access these vast troves of data from devices and from popular apps with the push of a button using cloud extraction technology.
Mobile phones remain the most frequently used and most important digital source for law enforcement investigations. Yet it is not just what is physically stored on the phone that law enforcement are after, but what can be accessed from it, primarily data stored in the Cloud.…
Content Type: News & Analysis
In the run up to the UK General Election on 12 December 2019, Privacy International, joined by other organisations called on political parties to come clean about their use of data. The lack of response to these demands combined with other evidence gathered by groups during the run up to the election demonstrates that current regulations are not fit for the digital era.
This briefing to which Privacy International contributed together with Demos, the Computational Propaganda Project at the…
Content Type: Long Read
Over the coming months, PI is going to start to look a bit different. We will have a new logo and a whole new visual identity.
And in turn, our new visual identity will only be one step in a wider process of PI reconnecting with our core mission and communicating it more effectively to you, following on from extensive consultation with our staff, board, our supporters and our international partners.
Our current black ‘redacted’ Privacy International logo, and the austere Cold War era dossier…
Content Type: Long Read
Following a series of FOI requests from Privacy International and other organisations, the Department of Health and Social Care has now released its contract with Amazon, regarding the use of NHS content by Alexa, Amazon’s virtual assistant. The content of the contract is to a big extent redacted, and we contest the Department of Health’s take on the notion of public interest.
Remember when in July this year the UK government announced a partnership with Amazon so that people would now…
Content Type: News & Analysis
On 24 October 2019, the Swedish government submitted a new draft proposal to give its law enforcement broad hacking powers. On 18 November 2019, the Legal Council (“Lagråd”), an advisory body assessing the constitutionality of laws, approved the draft proposal.
Privacy International believes that even where governments conduct hacking in connection with legitimate activities, such as gathering evidence in a criminal investigation, they may struggle to demonstrate that hacking as…
Content Type: Long Read
The pressing need to fix our cybersecurity (mis)understandings
Despite all the efforts made so far by different, cybersecurity remains a disputed concept. Some states are still approving cybersecurity laws as an excuse to increase their surveillance powers. Despite cybersecurity and cybercrime being different concepts, the confusion between them and the broad application of criminal statutes is still leading to the criminalise legitimate behaviour.
All of this represents a sizable challenge…
Content Type: News & Analysis
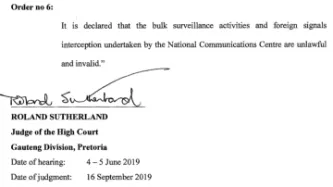
Today, the High Court of South Africa in Pretoria in a historic decision declared that bulk interception by the South African National Communications Centre is unlawful and invalid.
The judgment is a powerful rejection of years of secret and unchecked surveillance by South African authorities against millions of people - irrespective of whether they reside in South Africa.
The case was brought by two applicants, the amaBhungane Centre for Investigative Journalism and journalist Stephen…
Content Type: Advocacy
Privacy International's submission to the consultation initiated by the UN Special Rapporteur on counter-terrorism and human rights on the impact on human rights of the proliferation of “soft law” instruments and related standard-setting initiatives and processes in the counter-terrorism context.
In this submission Privacy International notes its concerns that some of this “soft law” instruments have negative implications on the right to privacy leading to violations of other human…
Content Type: News & Analysis
While people may think that providing their photos and data is a small price to pay for the entertainment FaceApp offers, the app raises concerns about privacy, manipulation, and data exploitation—although these concerns are not necessarily unique to FaceApp.
According to FaceApp's terms of use and privacy policy, people are giving FaceApp "a perpetual, irrevocable, nonexclusive, royalty-free, worldwide, fully-paid, transferable sub-licensable license" to use or publish the…
Content Type: Advocacy
In March 2019, Privacy International responded to a call for evidence for an inquiry by the UK Parliament's Joint Committee on Human Rights into "The Right to Privacy (Article 8) and the Digital Revolution".
Our suggestions included that, the human rights framework should support:
Increasing individuals’ control over their data to encourage the design of technologies that protect peoples’ autonomy and privacy.
Increasing security to result in more rights and protections for…
Content Type: Long Read
Join our campaign with Liberty and write to your local Police and Crime Commissioner (PCC). Your PCC works on your behalf to hold your local police force to account, so you can share your concerns about police spying tech with them.
You can download our new campaign pack (pdf link at the bottom of the page) to learn more about the police surveillance technology that might already be being used in your local area, and find out what you can do to get your police force to be more accountable to…
Content Type: Long Read
IMAGE SOURCE: "My Phone Bought This" by oliver t is licensed under CC BY-NC-ND 4.0.
LAST UPDATE: 16th May 2022.
Mandatory SIM card registration laws require people to provide personal information, including a valid ID or even their biometrics, as a condition for purchasing or activating a SIM card. Such a requirement allows the state to identify the owner of a SIM card and infer who is most likely making a call or sending a message at any given time.
SIM card…
Content Type: Long Read
When you go abroad, you expect to show your passport right? But what if immigration authorities wanted access to your Facebook, Instagram and Twitter accounts before they let you enter a country? What if they wanted to vet you based on your updates, photos, likes, retweets and even your DMs?
We think social media companies, who make literally billions of dollars out of you, and wield massive power and influence, should challenge governments on YOUR behalf. They should be protecting their users…
Content Type: Case Study
In 2030 Amtis finds a future where property rights for data were adopted. Here’s how this future plays out:
My data, my turf. This was the first graffiti I saw as I was walking down the street and I said to myself, “Yeah, big corp, we’re going to get you good!”. I am fed up with companies making insane amounts of money from my data. If this is the game we’re playing, I want my fair share.
I was not the only one thinking like this. A few years back there was a strong push towards adopting…
Content Type: Advocacy
The United Nations Special Rapporteur on extreme poverty and human rights, Philip Alston, is preparing a thematic report to the UN General Assembly on the human rights impacts, especially on those living in poverty, of the introduction of digital technologies in the implementation of national social protection systems. The report will be presented to the General Assembly in New York in October 2019.
As part of this process, the Special Rapporteur invited all interested governments, civil…
Content Type: Advocacy
Refugees are among the most vulnerable people in the world. From the moment they flee their homes, as they pass through 'temporary' places such as refugee camps and detention centres to their 'final' destinations, they are continuously exposed to threats. In the digital age, these threats are increasingly being driven by the processing of vast amounts of highly sensitive personal data: from enrollment and registration processes needed for them to access services, to their identification and…
Content Type: Video
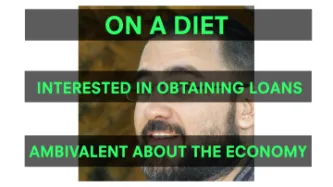
Watch our video primer (1m54s) on how political advertisers use highly detailed data about you to target political adverts at you.
Read about some simple steps you can take to minimise the amount of political ads you see online and questions you can be asking of those that profit from your data.
Content Type: News & Analysis
Planning and participating in peaceful protests against governments or non-state actors’ policies and practices requires the capacity of individuals to communicate confidentially without unlawful interference. From protests in support of LGBTI rights to protests against specific projects that undermine local communities’ wellbeing, these movements would not have been possible without the ability to exchange ideas and develop plans in private spaces.
Unlawful interference with…
Content Type: Explainer graphic
You can also read a more detailed explainer about social media intelligence (SOCMINT) here.
Content Type: Video
Video courtesy of CPDP (https://www.cpdpconferences.org/)
What is the impact of online gender-based violence on survivors? What should be the role of companies in fighting this phenomenon? What is the link between the right to privacy? In this panel, which took place at CPDP in February 2019, academics, civil society and government representatives discuss the issue of online gender based violence with a privacy lens.
Chair: Gloria González Fuster, VUB -LSTS (BE)
Moderator: Valerie…
Content Type: Explainer graphic
You can also read a more detailed explainer about facial recognition cameras here.