Advanced Search
Content Type: Long Read
This blog is about our new Twitter bot, called @adversarybot. If you want to follow the account, please do watch the pinned 'Privacy Policy' tweet before you do so.
Content Type: Long Read
Six years after NSA contractor Edward Snowden leaked documents providing details about how states' mass surveillance programmes function, two states – the UK and South Africa – publicly admit using bulk interception capabilities.Both governments have been conducting bulk interception of internet traffic by tapping undersea fibre optic cables landing in the UK and South Africa respectively in secret for years.Both admissions came during and as a result of legal proceedings brought by Privacy…
Content Type: Long Read
Image credit: Emil Sjöblom [ShareAlike 2.0 Generic (CC BY-SA 2.0)]
Prepaid SIM card use and mandatory SIM card registration laws are especially widespread in countries in Africa: these two factors can allow for a more pervasive system of mass surveillance of people who can access prepaid SIM cards, as well as exclusion from important civic spaces, social networks, and education and health care for people who cannot.
Mandatory SIM card registration laws require that people provide personal…
Content Type: Long Read
image from portal gda (cc)
Many people are still confused by what is 5G and what it means for them. With cities like London, New York or San Francisco now plastered with ads, talks about national security, and the deployment of 5G protocols being treated like an arms race, what happens to our privacy and security?
5G is the next generation of mobile networks, which is meant to be an evolution of the current 4G protocols that mobile providers have deployed over the last decade, and there are…
Content Type: Long Read
Photo by David Werbrouck on Unsplash
This is an ongoing series about the ways in which those searching for abortion information and procedures are being traced and tracked online. This work is part of a broader programme of work aimed at safeguarding the dignity of people by challenging current power dynamics, and redefining our relationship with governments, companies, and within our own communities. As an enabling right, privacy plays an important role in supporting the exercise of…
Content Type: Long Read
By Valentina Pavel, PI Mozilla-Ford Fellow, 2018-2019
Our digital environment is changing, fast. Nobody knows exactly what it’ll look like in five to ten years’ time, but we know that how we produce and share our data will change where we end up. We have to decide how to protect, enhance, and preserve our rights in a world where technology is everywhere and data is generated by every action. Key battles will be fought over who can access our data and how they may use it. It’s time to take…
Content Type: Long Read
Photo By: Cpl. Joel Abshier
‘Biometrics’ describes the physiological and behavioural characteristics of individuals. This could be fingerprints, voice, face, retina and iris patterns, hand geometry, gait or DNA profiles. Because biometric data is particularly sensitive and revealing of individual’s characteristics and identity, it can be applied in a massive number of ways – and has the potential to be gravely abused.
Identification systems across the world increasingly rely on…
Content Type: Long Read
Whilst innovation in technology and data processing have provided individuals and communities with new opportunities to exercise their fundamental rights and freedoms, this has not come without risks, and these opportunities have not been enjoyed by all equally and freely.
Our relationships and interactions with governments and industry have become increasingly dependent on us providing more and more data and information about ourselves. And, it’s not only the information we provide knowingly…
Content Type: Long Read
Everyday objects and devices that can connect to the Internet -- known as the Internet of Things (IoT) or connected devices -- play an increasing role in crime scenes and are a target for law enforcement. Exploiting new technologies that are in our homes and on our bodies as part of criminal investigations and for use as evidence, raises new challenges and risks that have not been sufficiently explored.
We believe that a discussion on the exploitation of IoT by law enforcement would…
Content Type: Report
Like many others, PI were alarmed at recent reports that Facebook have been making mobile phone numbers (which users believed to be) provided for the express purpose of "two-factor authentication" (2FA) both searchable, and a target for advertising by default.
One of the myriad ways Facebook displays targeted adverts to users is through so-called "Custom Audiences". These "custom audiences" are lists of contact details, including phone numbers and email addresses, uploaded by advertisers.…
Content Type: Long Read
Image courtesy of Michael Coghlan
The long-speculated Facebook cryptocurrency is finally here! Libra!
Libra Association, an entity co-founded by Facebook, has announced the creation of a new cryptocurrency, Libra, "a simple global currency and financial infrastructure that empowers billions of people".
The white paper that outlines the rationale for the new currency makes a number of heady statements, some which anyone who cares about rights should commend -- and some which should…
Content Type: Long Read
The UK public, regulators, and parliamentarians have all expressed concern about the wide use of third-party data by all political parties in the UK and its impact on privacy and democracy. In the week the remaining six candidates to be the UK’s next Prime Minister are reduced to two, Privacy International takes a look at their privacy policies to illustrate how such policies can be used to identify the use of third-party data by political candidates from all political parties.
The…
Content Type: Long Read
Join our campaign with Liberty and write to your local Police and Crime Commissioner (PCC). Your PCC works on your behalf to hold your local police force to account, so you can share your concerns about police spying tech with them.You can download our new campaign pack (pdf link at the bottom of the page) to learn more about the police surveillance technology that might already be being used in your local area, and find out what you can do to get your police force to be more accountable to you…
Content Type: Long Read
IMAGE SOURCE: "My Phone Bought This" by oliver t is licensed under CC BY-NC-ND 4.0.
LAST UPDATE: 16th May 2022.
Mandatory SIM card registration laws require people to provide personal information, including a valid ID or even their biometrics, as a condition for purchasing or activating a SIM card. Such a requirement allows the state to identify the owner of a SIM card and infer who is most likely making a call or sending a message at any given time.
SIM card…
Content Type: Long Read
When you go abroad, you expect to show your passport right? But what if immigration authorities wanted access to your Facebook, Instagram and Twitter accounts before they let you enter a country? What if they wanted to vet you based on your updates, photos, likes, retweets and even your DMs?We think social media companies, who make literally billions of dollars out of you, and wield massive power and influence, should challenge governments on YOUR behalf. They should be protecting their users…
Content Type: Case Study
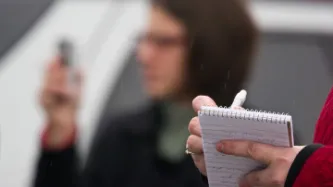
Photo by Roger H. Goun
Chloe is an investigative journalist working for an international broadcast service; we will call the TV show she works for The Inquirer. She travels around the world to work with local journalists on uncovering stories that make the headlines: from human trafficking to drug cartels and government corruption. While her documentaries are watched by many and inspire change in the countries she works in, you would not know who Chloe is if we were to tell you her real name.…
Content Type: Long Read
Like millions of other people, you use messaging apps, social media, share, read and watch content on your phone or computer. If that’s the case then hundreds of AdTech companies collect and exchange your data every single day. AdTech, a short form of advertisement technology, is a catch-all term that describes tools and services that connect advertisers with target audiences and publishers. It’s also a multi-billion-dollar industry that is facing investigations by Data Protection Authorities…
Content Type: Long Read
OPTION 1 - LIMIT TARGETED ADVERTISING
A simple step you can take is turning on strong (as possible) privacy settings on the social media platforms you use. Social media platforms play a key role in targeting ads at you – and they facilitate the use of your data in ways that you probably wouldn’t like. We've made guides to show you how to minimise the targeted ads you see on social media. These steps can help make advertising less targeted, meaning that an advertiser, in theory, will knows less…
Content Type: Long Read
CEOs of the big tech companies have all recently discovered the value of privacy. On Tuesday, 30 April 2019, Mark Zuckerberg, announced his future plans to make Facebook a "privacy-focused social platform". This was followed by Google's Sundar Pichai demand that “privacy must be equally available to everyone in the world.” Meanwhile, Twitter's Jack Dorsey, has described the General Data Protection Regulation (GDPR) as "net-positive", while Apple had already positioned itself as the champion of…
Content Type: Long Read
Image Source: "Voting Key" by CreditDebitPro is licensed under CC BY 2.0
Democratic society is under threat from a range of players exploiting our data in ways which are often hidden and unaccountable. These actors are manifold: traditional political parties (from the whole political spectrum), organisations or individuals pushing particular political agendas, foreign actors aiming at interfering with national democratic processes, and the industries that provide products that …
Content Type: Long Read
Imagine that every time you want to attend a march, religious event, political meeting, protest, or public rally, you must share deeply personal information with police and intelligence agencies, even when they have no reason to suspect you of wrongdoing.
First, you need to go to the police to register; have your photo taken for a biometric database; share the contacts of your family, friends, and colleagues; disclose your finances, health records, lifestyle choices, relationship status, and…
Content Type: Long Read
“Truth exists, but you have to find it”, Oleksandra Matviychuk of Ukraine’s Center for Civil Liberties told me as I interviewed her in central Kyiv one week before the 2019 Ukrainian run-off election, “and in order to do so you have to make some effort”. We’re talking about her experience working on the ground in Ukraine, a country with a long history of battling against disinformation.
Activists in Ukraine have long experience navigating the noisy and chaotic environment that disinformation…
Content Type: Long Read
This image was found here.
Spain is holding a national general election on April 28 (its third in four years). Four weeks later Spaniards will again go to the polls to vote in the European Parliament elections. At Privacy International we are working to investigate and challenge the exploitation of people’s data in the electoral cycle including in political campaigns. This includes looking at the legal frameworks governing the use of data by political parties and their…
Content Type: Long Read
Last week, an investigation by Bloomberg revealed that thousands of Amazon employees around the world are listening in on Amazon Echo users.
As we have been explaining across media, we believe that by using default settings and vague privacy policies which allow Amazon employees to listen in on the recordings of users’ interactions with their devices, Amazon risks deliberately deceiving its customers.
Amazon has so far been dismissive, arguing that people had the options to opt out from the…
Content Type: Long Read
(In order to click the hyperlinks in the explainer below, please download the pdf version at the bottom of the page).
Content Type: Long Read
The UK border authority is using money ring-fenced for aid to train, finance, and provide equipment to foreign border control agencies in a bid to “export the border” to countries around the world.
Under the UK Border Force’s “Project Hunter”, the agency works with foreign security authorities to bolster their “border intelligence and targeting” capabilities with UK know-how and equipment.
As well as the provision of equipment and training, the Border Force is also advising countries on…
Content Type: Long Read
Cellebrite, a surveillance firm marketing itself as the “global leader in digital intelligence”, is marketing its digital extraction devices at a new target: authorities interrogating people seeking asylum.
Israel-based Cellebrite, a subsidiary of Japan’s Sun Corporation, markets forensic tools which empower authorities to bypass passwords on digital devices, allowing them to download, analyse, and visualise data.
Its products are in wide use across the world: a 2019 marketing…
Content Type: Long Read
(In order to click the hyperlinks in the explainer below, please download the pdf version at the bottom of the page).
Content Type: Long Read
(In order to click the hyperlinks in the explainer below, please download the pdf version at the bottom of the page).
Content Type: State of Privacy
Introduction
Acknowledgment
The State of Surveillance in Tunisia is the result of an ongoing collaboration by Privacy International and partners.
On 14 February 2023, the United Nations High Commissioner for Human Rights voiced concern over the deepening crackdown in Tunisia targeting perceived political opponents of President Kais Saied as well as civil society.
We have updated this page to reflect important changes in the state of surveillance in Tunisia.
Key privacy facts
1.…